KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The T-Mobile data breach keeps getting worse as an update to their investigation now reveals that cyberattack exposed over 54 million individuals’ data.
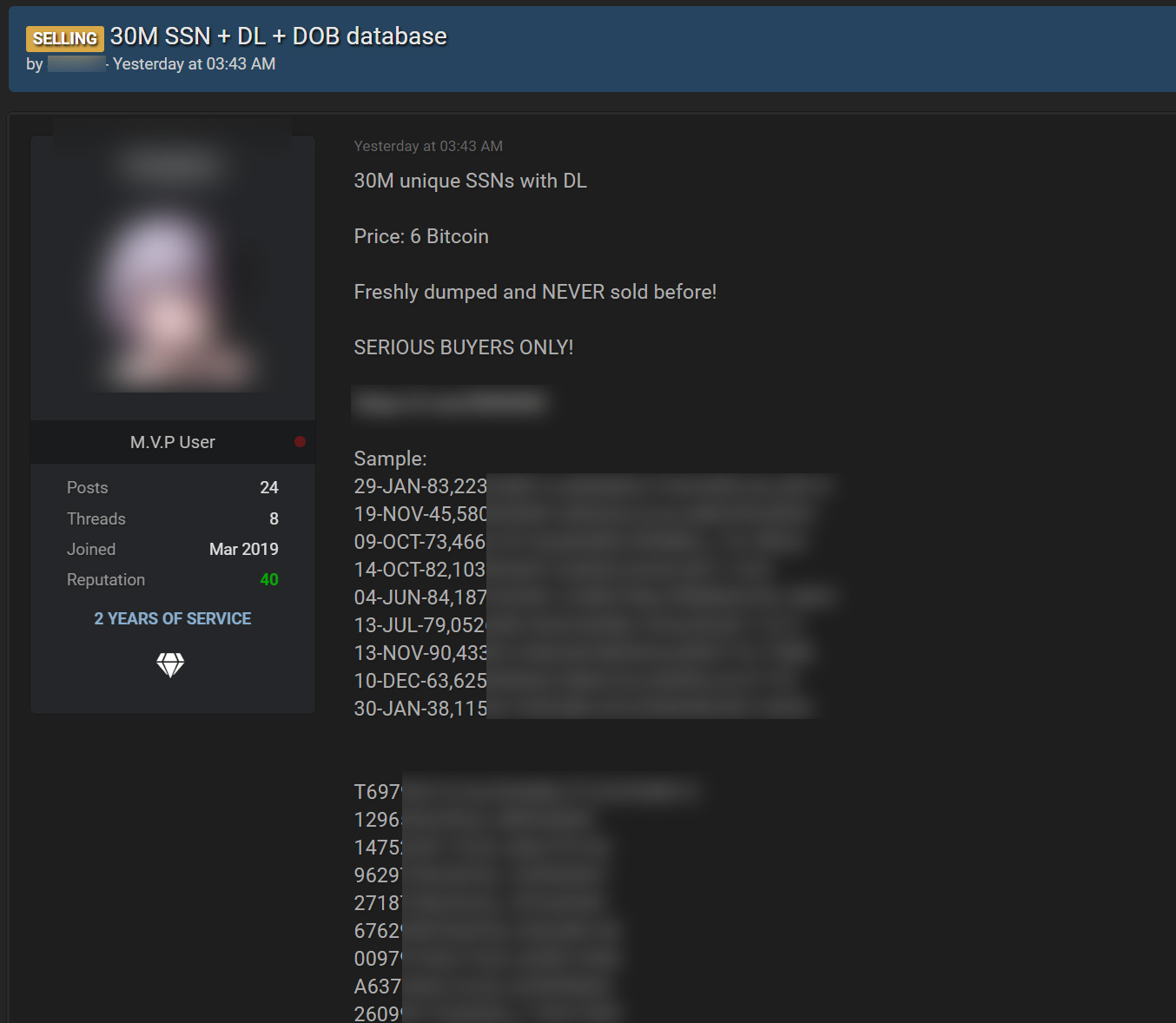
Last weekend, a threat actor began selling the personal information of 100 million T-Mobile customers on a hacking forum for six bitcoin (~$280K).
Also Read: Protecting Data Online in The New Normal
The hacker said that the stolen database contains the data for approximately 100 million T-Mobile customers. The exposed data can include customers’ IMSI, IMEI, phone numbers, customer names, security PINs, Social Security numbers, driver’s license numbers, and date of birth.
The hackers said the database was stolen approximately two weeks ago and contains customer data from as far back as 2004.
“Their entire IMEI history database going back to 2004 was stolen,” the hacker told BleepingComputer.
T-Mobile later confirmed that some of its servers were hacked and began investigating what customer data was exposed.
On August 17th, T-Mobile first disclosed a summary of their investigation into their hacked servers and said that the personal information of 48.6 million individuals was exposed during the attack.
Today, T-Mobile has updated its advisory to include an additional 6 million customers or prospective customers affected by the attack.
Furthermore, T-Mobile has confirmed our original reporting on this attack that the attackers also stole IMSI and IMEI numbers.
As it stands today, the attack affected 54.6 million individuals, which is broken down below.
T-Mobile continues to see no sign of payment information or financial information exposed during the attack.
We will likely continue to see the number of exposed customers increase in the coming weeks.
It is advised that all T-Mobile customers assume that their data was exposed and be on the lookout for targeted phishing emails and SMS texts.
Also Read: The Top 4W’s of Ethical Hacking
If any are received, do not click any links embedded in the messages as threat actors could use them to harvest credentials from unsuspecting T-Mobile customers.