KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The sites of several Ukrainian government agencies (including the Ministries of Foreign Affairs, Defense, and Internal Affairs, the Security Service, and the Cabinet of Ministers), and of the two largest state-owned banks are again targeted by Distributed Denial-of-Service (DDoS) attacks.
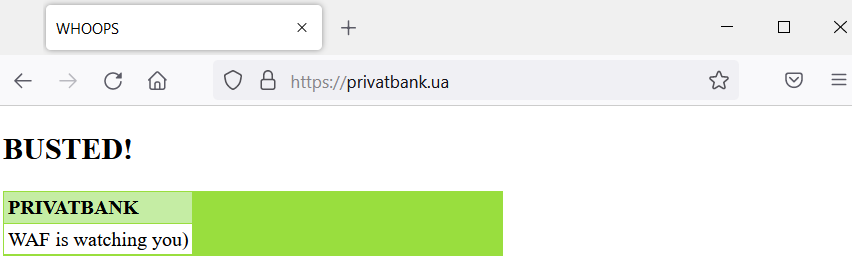
Internet watchdog NetBlocks also confirmed that the websites Privatbank (Ukraine’s largest bank) and Oschadbank (the State Savings Bank) were being hammered in the attacks and knocked down together with Ukrainian government sites.
“Today, websites of a number of government and banking institutions have undergone a massive DDoS attack again. Some of the attacked information systems are not available or work intermittently,” the State Service of Special Communication and Information Protection (SSCIP) of Ukraine said.
Also Read: The 7 Fundamental Guide on SOP for Social Media Marketing
Currently, the Ukrainian SSSCIP and other national cybersecurity agencies “are working on countering the attacks, collecting and analyzing information.”
These attacks follow another series of DDoS incidents that impacted Ukrainian government websites and banks last week, taking down the sites of the Ministry of Defense and the Armed Forces of Ukraine.
In a report published three days after last week’s incidents, the Computer Emergency Response Team of Ukraine (CERT-UA) said the attackers carried out the February 15th DDoS attacks using DDoS-as-a-Service platforms and multiple bot networks, including Mirai and Meris.
The same day, the White House linked the DDoS attacks to Russia’s Main Directorate of the General Staff of the Armed Forces (also known as GRU).
“We have technical information that links the Russian main intelligence directorate, or GRU, as known GRU infrastructure was seen transmitting high volumes of communication to Ukraine-based IP addresses and domains,” Deputy National Security Advisor for Cyber Anne Neuberger said.
Also Read: 7 Principles of Personal Data Processing
Neuberger added that, even though they had “limited impact,” the attacks can be seen as “laying groundwork” for more disruptive attacks that would come together with a potential invasion of Ukraine’s territory.
The UK government also pointed fingers at Russian GRU hackers being behind the DDoS attacks targeting online services belonging to the Ukrainian military and state-owned bank websites during the last week.
These attacks follow a press release from Ukraine’s Security Service (SSU)—whose website was also impacted—saying that the country is being targeted by a “massive wave of hybrid warfare.“
The SSU said earlier this month that it blocked over 120 cyberattacks targeting Ukrainian state agencies throughout January 2022.