KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







US defense contractor Electronic Warfare Associates (EWA) has disclosed a data breach after threat actors hacked their email system and stole files containing personal information.
The company claims the breach’s impact was limited but confirmed that the threat actor managed to exfiltrate files containing sensitive information.
As detailed in a notice to the Montana Attorney General’s office, EWA discovered that a threat actor took over one of their email accounts on August 2, 2021.
The firm noticed the infiltration when the hacker attempted wire fraud, which appears to be the primary goal of the actor.
Also Read: Data Storage Security Standards: What Storage Professionals Need to Know
“Based on our investigation, we determined that a threat actor infiltrated EWA email on August 2, 2021. We were made aware of the situation when the threat actor attempted wire fraud,” reads EWA’s data incident notification.
“We have no reason to believe the purpose of the infiltration was to obtain personal information. Nevertheless, the threat actor’s activities did result in the exfiltration of files with certain personal information (as described below).”
Based on the investigation that followed, it was discovered that names, social security numbers (SSNs), and the driver’s license of the notice recipients were also stolen.
As such, the wire fraud attempt may have been a distraction, which is entirely plausible for sophisticated actors who are interested in targeting highly-sensitive firms of this type.
It is unclear if the stolen information affects only the company’s employees and whether or not technical documents have also been stolen during the incident.
In response to the security lapse, the company is now offering a two-year subscription to identity theft protection services through Equifax.
Moreover, the notice urges recipients to monitor their credit reports and financial account statements closely.
EWA is a specialist in high-tech defense hardware and software solutions for communication, access control, simulation, training, management, testing, and monitoring systems (radars).
Also Read: IT Governance Framework PDF Best Practices And Guidelines
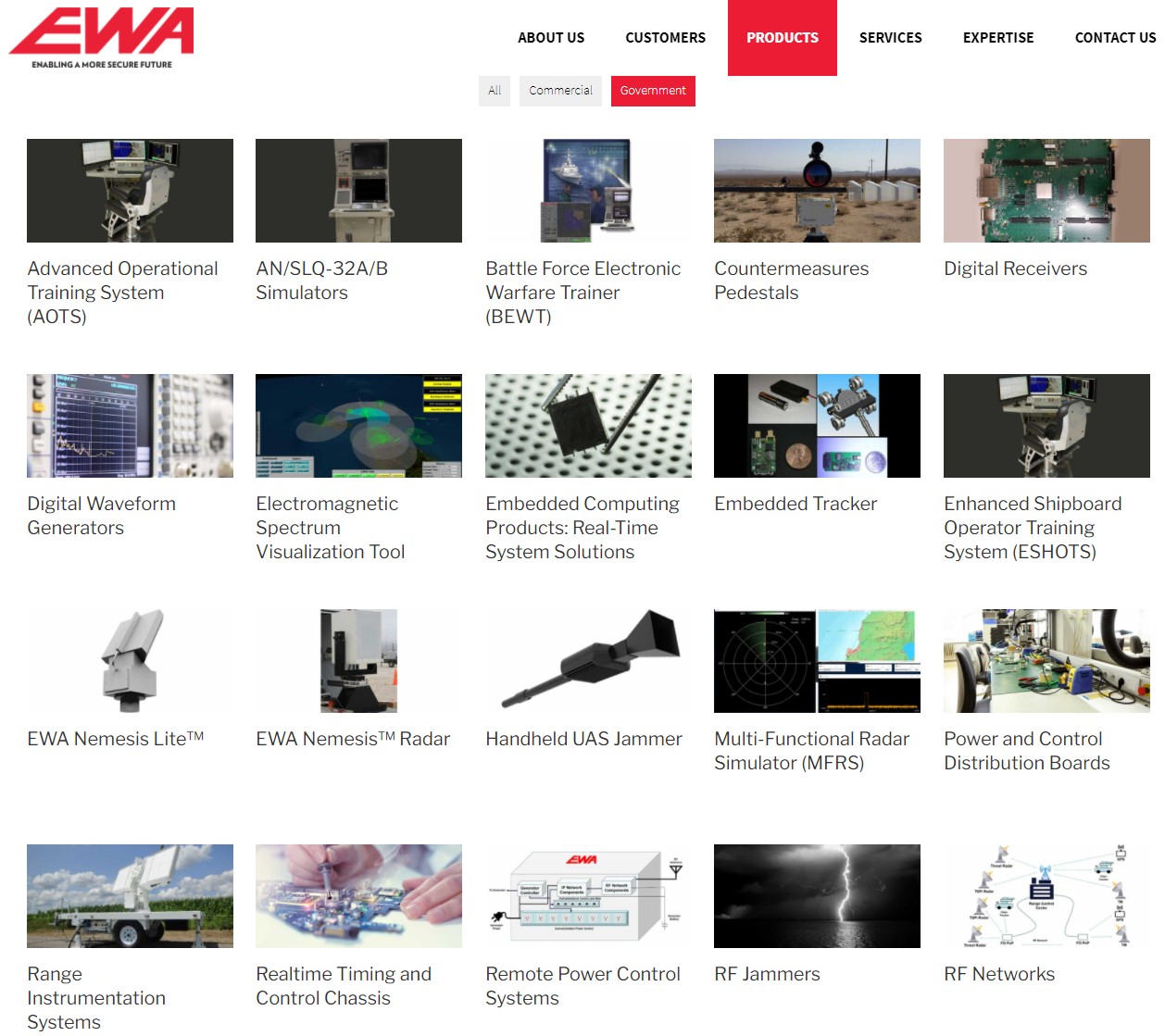
Many of these products are made for highly sensitive customers, including the U.S. Department of Defense (Army, Navy, Air Force, DARPA, OSD), the Department of Justice, and Homeland Security (DHS).
A data breach on the firm’s email systems may have also compromised military technology secrets as EWA develops and designs these products internally.
EWA also develops commercial products through subsidiary brands like Corelis (electronic testing and analysis) and Blackhawk (debugging tools).
We have reached out to EWA asking for more details about the hacking incident and the exact impact it has on them, and we will update this post if we receive a response.