KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Google has released Chrome 94.0.4606.71 for Windows, Mac, and Linux, to fix two zero-day vulnerabilities that have been exploited by attackers.
“Google is aware the exploits for CVE-2021-37975 and CVE-2021-37976 exist in the wild,” Google disclosed in the list of security fixes fixed in today’s Google Chrome release.
Google has started rolling out Chrome 94.0.4606.71 to users worldwide in the Stable Desktop channel and should be available to all users within the coming days.
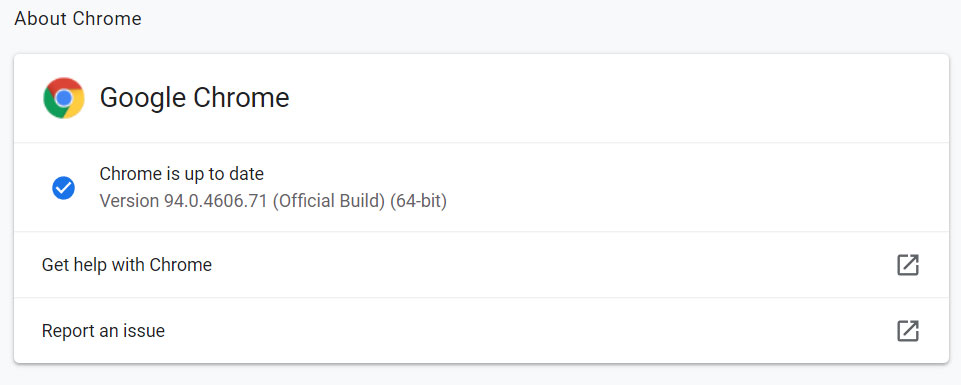
To install the update immediately, Google Chrome users can go to Chrome menu > Help > About Google Chrome, and the browser will begin performing the update.
Also Read: Cross Border Data Privacy- A Guide for Singapore Businesses
In our tests, the new version of the browser was installed immediately using the above steps.
Google Chrome will also check for available updates and install them the next time you launch the web browser.
While this Chrome release includes fixes for four security vulnerabilities, the two zero-days are concerning as they are known to have been exploited in the wild.
The first zero-day, tracked as CVE-2021-37976, is described as an “Information leak in core” and was assigned a Medium severity level. This vulnerability was discovered by Clément Lecigne from Google TAG, with technical assistance from Sergei Glazunov and Mark Brand from Google Project Zero, on September 21st, 2021.
The second zero-day, tracked as CVE-2021-37975, is a High severity user after free bug in the Chrome V8 JavaScript engine. The researcher disclosed this vulnerability on September 24th and wished to remain anonymous.
Use after free bugs are commonly used to perform remote code execution or escape the browser’s security sandbox.
Also Read: How to Register Data Protection Officer (DPO) in ACRA Bizfile+
At this time, there are no other details regarding how these zero-day vulnerabilities were used in attacks but may be released in future reports by Google TAG or Project Zero.
2 more in-the-wild 0days fixed by Chrome:
* CVE-2021-37975 use-after-free in V8 by anonymous
* CVE-2021-37976 info leak in core by @_clem1 #itw0days
The release cycle that Chrome is making happen in order to get these patches out is pretty impressivehttps://t.co/j1xPY4zjlP— Maddie Stone (@maddiestone) September 30, 2021
Chrome users should perform a manual upgrade or restart their browser to install the latest version and prevent exploitation attempts.
With these two fixes, Google has patched 13 zero-day vulnerabilities in the Chrome web browser since the start of 2021.
The other Chrome zero-day bugs Google fixed this year are:
As Google is rushing out Chrome updates to fix zero-days as they are reported, it is always critical to install new browser updates as soon as they become available.