KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A large-scale campaign involving over 200 phishing and scam sites has tricked users into giving their personal data to fake investments schemes impersonating genuine brands.
The fraudulent operation relies upon the abuse of Google Ads and SEO to draw victims to hundreds of fake websites targeting the Indian audience.
The campaign was uncovered by Singaporean security firm CloudSEK, which has shared its report exclusively with Bleeping Computer.
According to analysts Ankit Dobhal and Aryan Singh, the campaign has caused financial damages of up to $1,000,000, coming from tens of thousands of victims.
Also Read: Managing employee data under Singapore’s PDPA
The government in India has recently introduced favorable policies to boost the growth of the country’s EV (electric vehicle) sector.
These policies are forecasted to bring a growth of 90% (CAGR) for the Indian EV market before the end of the decade, making it a $200 billion sector.
Over 400 EV startups have already launched in the country, while existing automotive companies are also aggressively extending their operations in the emerging field.
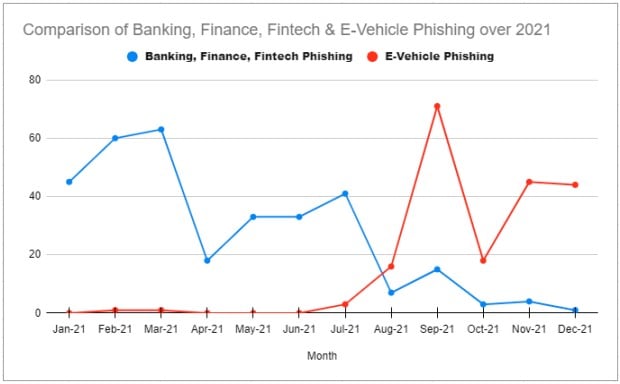
Scammers have identified these conditions as a fertile ground for trickery, with an explosion of websites attempting to exploit this sudden boom spiking since August 2021 and remaining in large volumes today.
Moreover, CloudSEK reports having identified a shift in the focus of phishing actors during that period, abandoning banking and finance lures in favor of EV themes.
The threat actors ensure a steady influx of potential victims by abusing Google Ads, stuffing their phony sites with keywords, and mimicking well-known brands such as Revolt and Ather.
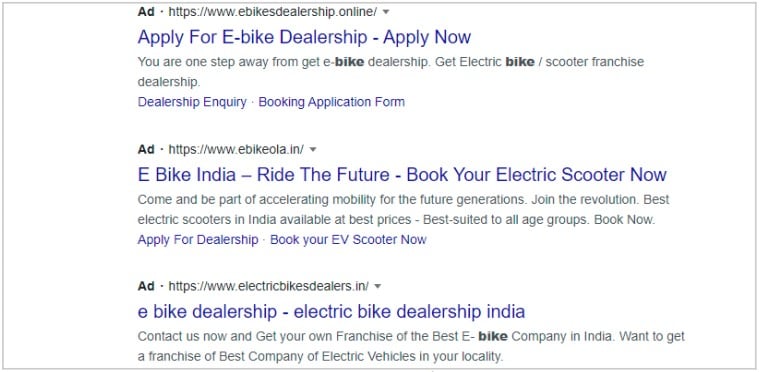
In many cases, the malicious actors simply copy the content, style, layout, and all images of the legitimate site and create clones.
In other cases, the scammers are building entirely fictional marketplaces using generic words like “ebike,” to supposedly offer products from multiple brands.
Also Read: Race against time: How CSA dissect cyberattacks using sophisticated gadgets
.jpg)
Visitors of these websites are instructed to enter their full names, contact numbers, email addresses, and physical address to register on the platforms.
Once they have completed the registration, the scammers ask them to pay the fee required to become an EV dealer or purchase a product on the site.
Unfortunately, the victims are also giving away their banking/payment details to the crooks at this step.
Although the threat analysts discovered 200 active phishing domains, they warn that the swarm is constantly being refreshed, with new sites taking the place of those reported and taken down.
“They (scammers) register a large number of domains and keep some of them parked for use in the future,” explains the CloudSEK report.
“Hence, if active domains are reported or taken down, they can use the parked domains to continue running the campaign.”

In terms of the impact, the researchers observed between 100 and 200 users registering on these sites per day and estimated the total financial losses to be INR40-80 million ($500,000 – $1,000,000).
A list of scam 100 domains can be seen here, while the remainder 100 has not been disclosed at the request of the affected EV dealer, who is mimicked by all of them.
CloudSEK has told Bleeping Computer they have shared the entire phishing domains list with Google to help stop the Ads abuse.
The size of the operation and the scale of the Google Ads abuse is such that spotting the fraudulent sites may be challenging.
Consumers can ensure they’re on the official EV dealer portal by using India’s e-AMRIT database and confirming the relation between URLs and legitimately registered marketplaces.
As for affected businesses, reporting the phishing sites won’t cause much of a disruption for the threat actors. Instead, report them to your state government’s office Cyber Crime Cell to help identify and track down its operators.
Additionally, run awareness-raising campaigns to help your customers understand the risks of phishing, promote official domains, and highlight signs of fraud.