KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Twitter is emailing developers stating that their API keys, access tokens, and access token secrets may have been exposed in a browser’s cache.
In an email seen by BleepingComputer, Twitter explains that a developer’s browser may have cached the sensitive data when visiting certain pages on developer.twitter.com.
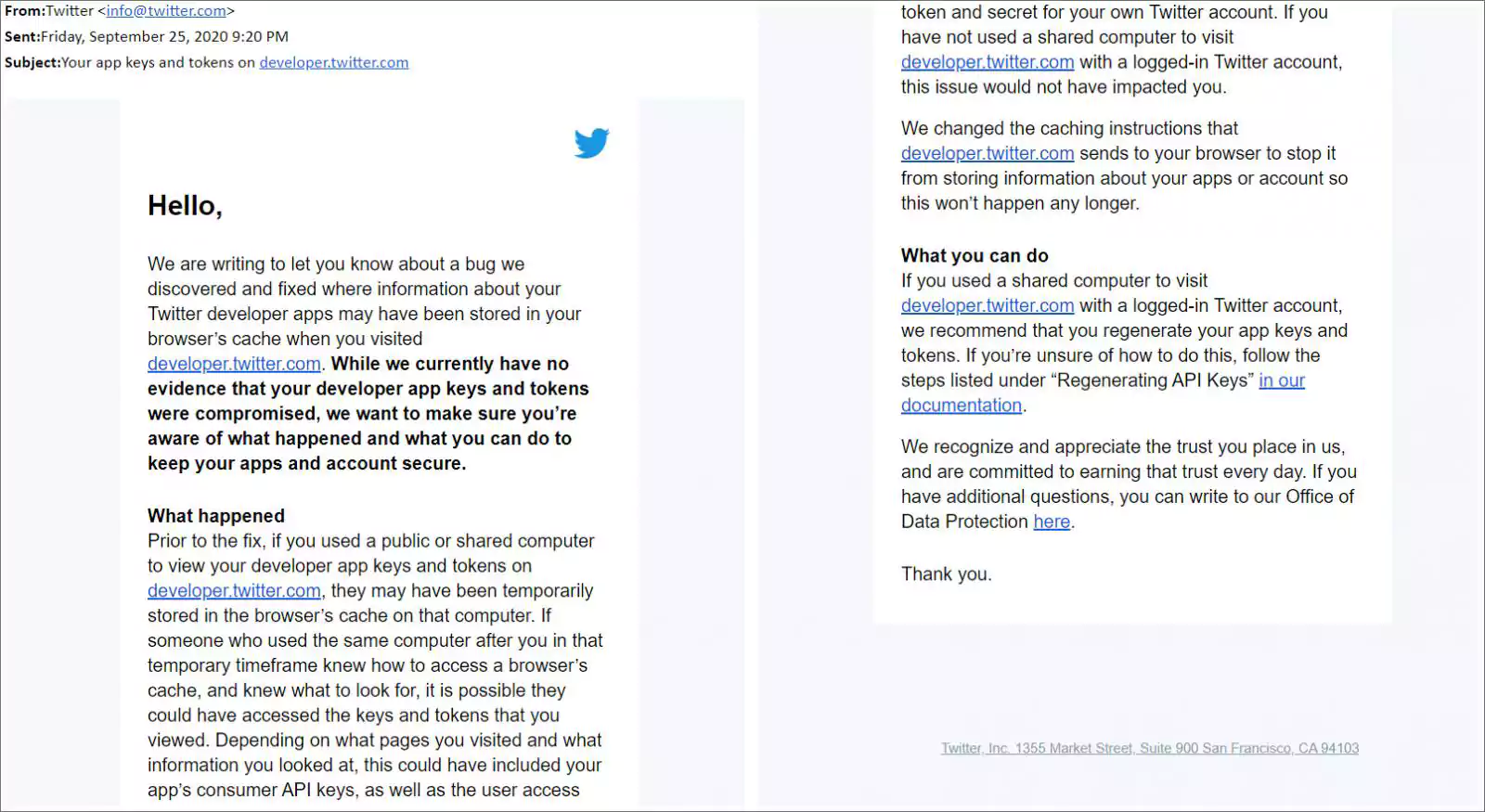
Twitter has resolved the issue by not allowing this data to be cached in your browser but warned that other users who used your computer in the past might have been able to access your security tokens and API keys.
“Prior to the fix, if you used a public or shared computer to view your developer app keys and tokens on developer.twitter.com, they may have been temporarily stored in the browser’s cache on that computer. If someone who used the same computer after you in that temporary timeframe knew how to access a browser’s cache, and knew what to look for, it is possible they could have accessed the keys and tokens that you viewed.”
Also Read: Computer Misuse Act Singapore: The Truth And Its Offenses
“Depending on what pages you visited and what information you looked at, this could have included your app’s consumer API keys, as well as the user access token and secret for your own Twitter account,” Twitter stated in an email.
Security tokens and API keys allow an app to access various permissions and data for a particular Twitter account.
If an unauthorized user can access the API key or security tokens, they will also gain full access to the same permissions and data as the app.
Due to this, security tokens and API keys are to be guarded as secretly as you would a password to your account.
While Twitter has stated there is no “evidence that your developer app keys and tokens were compromised,” it may be safer to regenerate API keys and access tokens to be safe.
This can be done by going into the app on developer.twitter.com, selecting details, and then ‘Keys and tokens.’
Twitter had previously warned of data leaks on their platform in April 2020 but indicated that this was an issue with how Firefox cached data.
Also Read: 10 Practical Benefits of Managed IT Services