KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





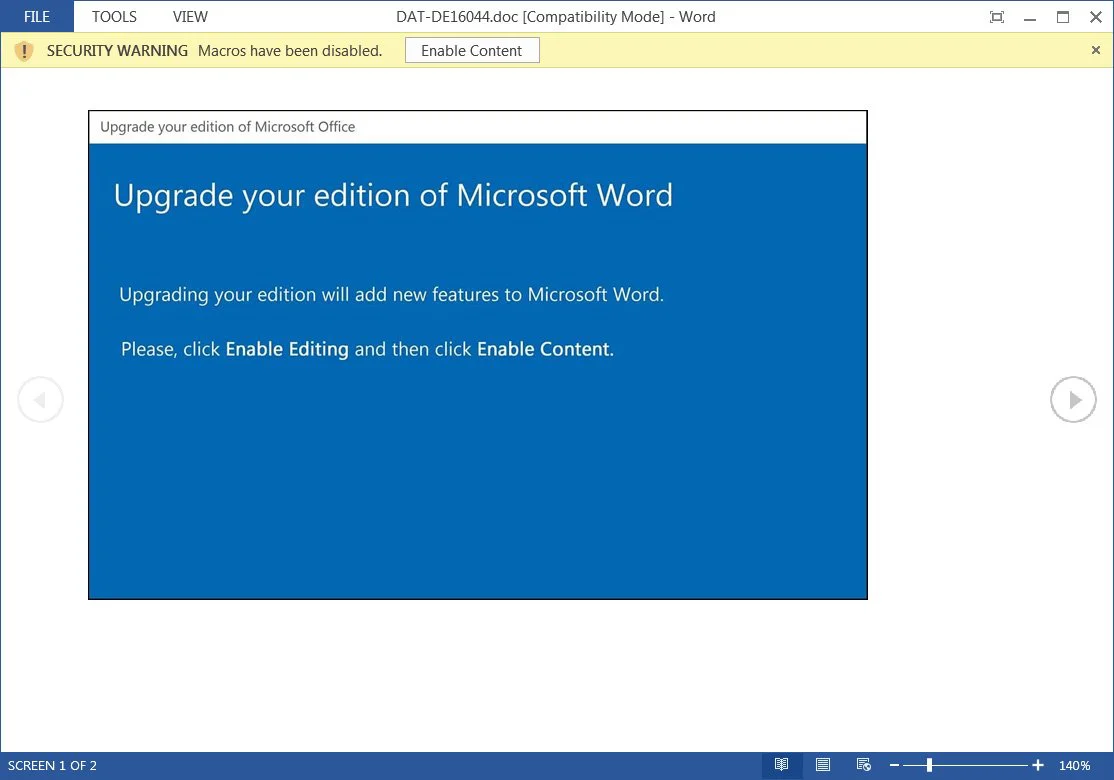
Emotet switched to a new template this week that pretends to be a Microsoft Office message stating that Microsoft Word needs to be updated to add a new feature.
Emotet is a malware infection that spreads through emails containing Word documents with malicious macros. When opening these documents, their contents will try to trick the user into enabling macros so that the Emotet malware will be downloaded and installed on the computer.
Once the malware is installed, Emotet will use the computer to send spam emails and ultimately install other malware that could lead to a ransomware attack on the victim’s network.
Emotet spam campaigns use a variety of lures to trick recipients into open an attachment, such as pretending to be invoices, shipping notices, resumes, or purchase orders, or even COVID-19 information, as shown below.
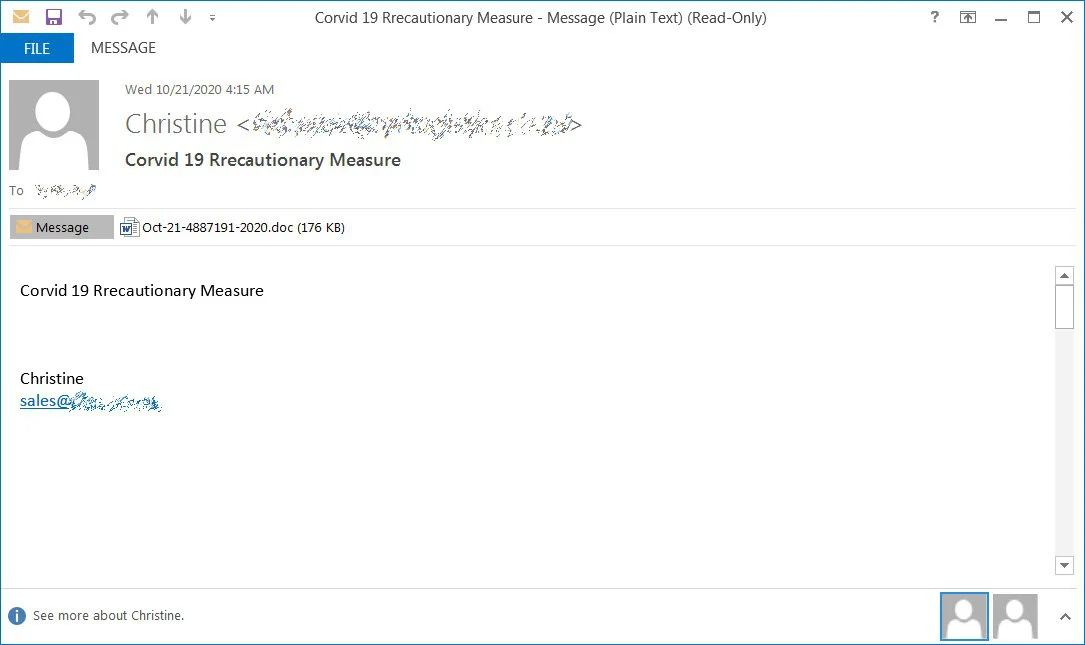
Attached to these spam emails are malicious Word (.doc) attachments or links to download one.
When opened, these attachments will prompt a user to ‘Enable Content’ so that malicious macros will run to install the Emotet malware on a victim’s computer.
Also Read: Computer Misuse Act Singapore: The Truth And Its Offenses
To trick users into enabling the macros, Emotet uses various designs, or document templates, that displays a warning to the user.
Emotet switched to a new template this week that pretends to be a Microsoft Office message stating that Microsoft Word needs to be updated to add a new feature.
To upgrade Microsoft Word, the document tells the user to click on the Enable Editing and then the Enable Content button, which will cause cause the malicious macros to execute.
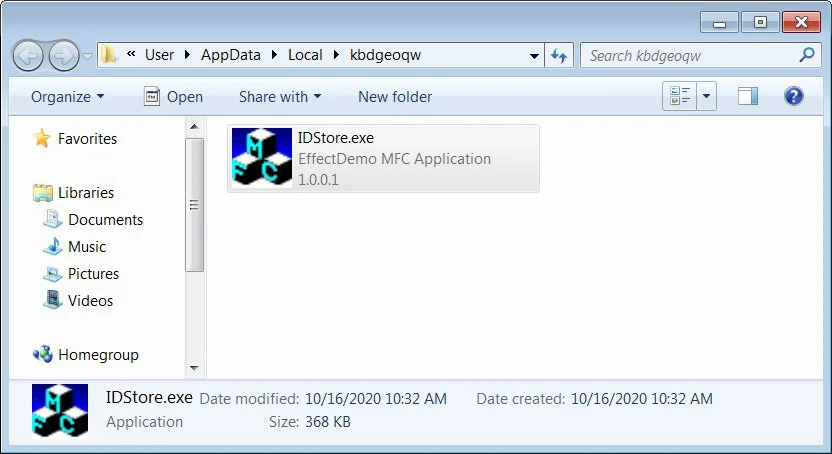
These malicious macros will download and install the Emotet malware into the victim’s %LocalAppData% folder, as shown below.
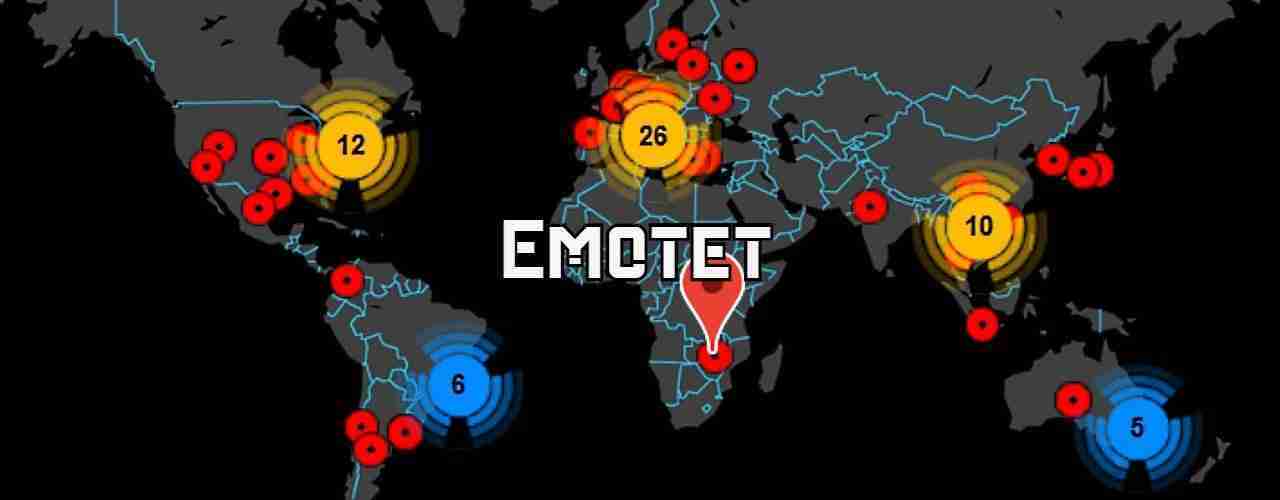
Emotet is considered the most widely spread malware targeting users today. It is particularly dangerous as it installs other infections such as the Trickbot and QBot malware onto a victim’s computer.
Also Read: PDPA For Companies: Compliance Guide For Singapore Business
When installed, TrickBot and QBot will attempt to steal stored passwords, bank information, and assorted other information, but also commonly lead to Conti (TrickBot) or ProLock (QBot) ransomware attacks.
Due to this, it is important that all email users recognize malicious document templates used by Emotet so that you do not accidentally become infected.