KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new phishing campaign has been targeting U.S. organizations in the military, security software, manufacturing supply chain, healthcare and pharmaceutical sectors to steal Microsoft Office 365 and Outlook credentials.
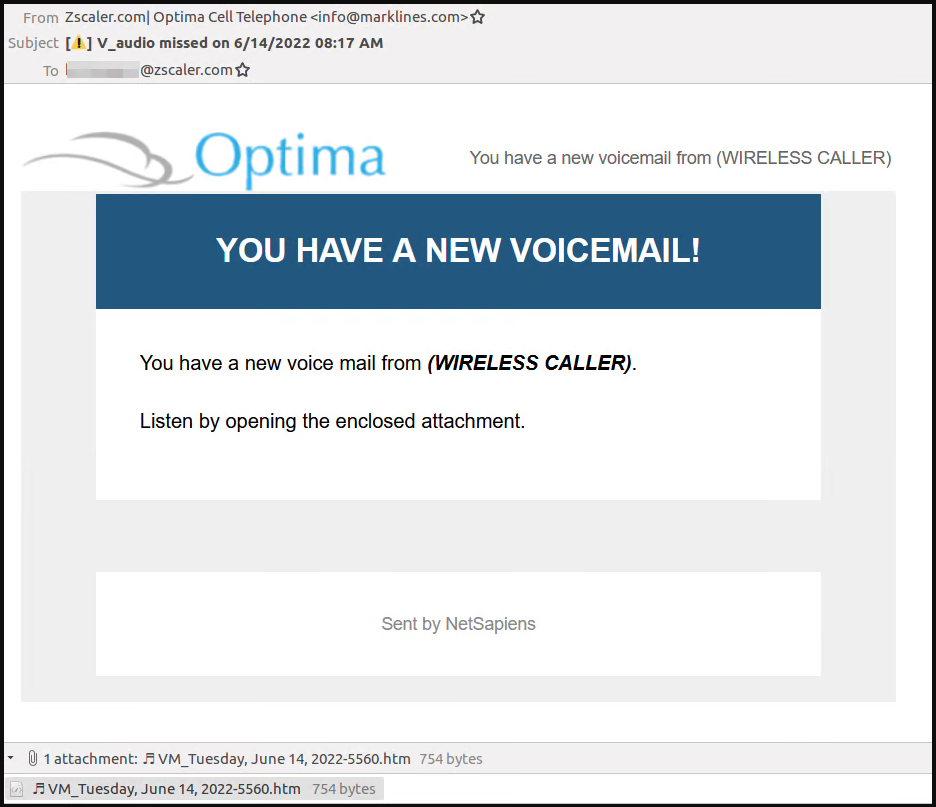
The operation is ongoing and the threat actor behind it uses fake voicemail notifications to lure victims into opening a malicious HTML attachment.
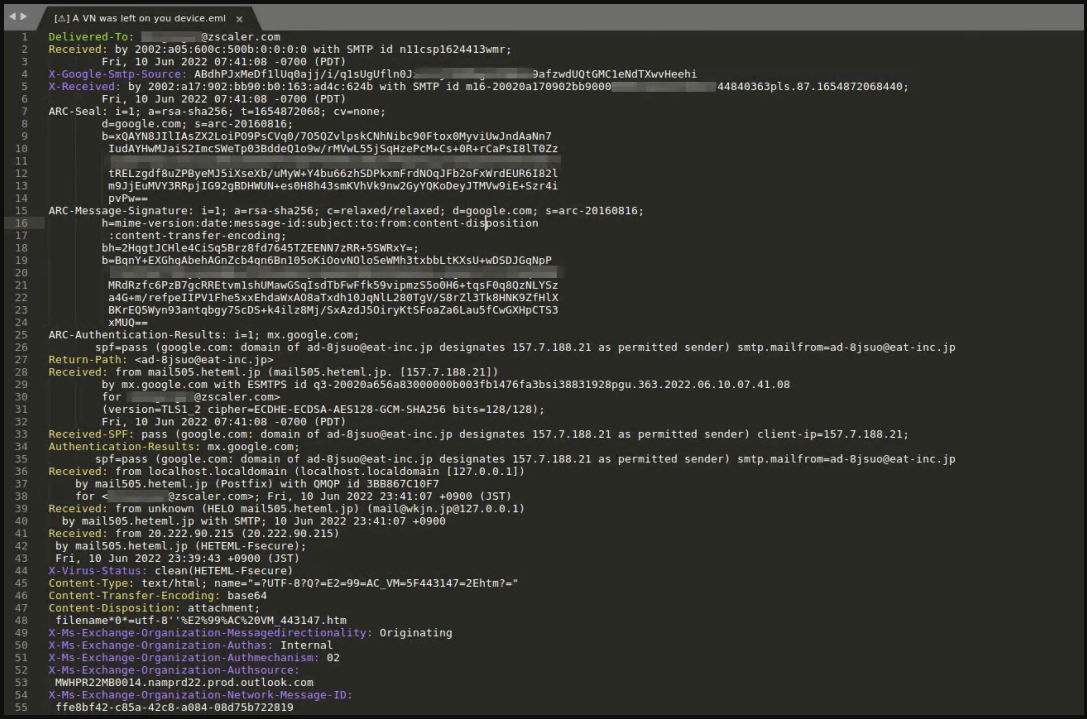
According to researchers at cloud security company ZScaler, the recently discovered campaign shares tactics, techniques, and procedures (TTPs) with another operation analyzed in mid-2020.
Also Read: A beginner’s guide to the Singapore PDPA
The threat actors leverage email services in Japan to route their messages and spoof the sender’s address, making it look like the emails come from an address belonging to the targeted organization.
The email has an HTML attachment that uses a music note character in the naming to make it appear as if the file is a sound clip. In reality, the file contains obfuscated JavaScript code that takes the victim to a phishing site.
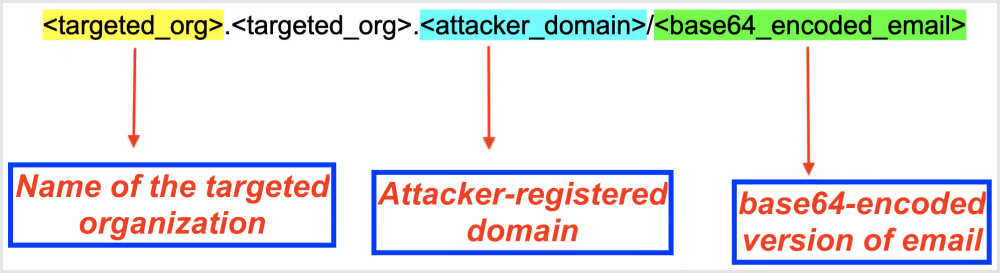
The URL format follows an assembly system that considers the targeted organization’s domain to make it appear as if the site is a legitimate subdomain.
The redirection process first takes the victim to a CAPTCHA check, which is designed to evade anti-phishing tools and increases the illusion of legitimacy for the victims.
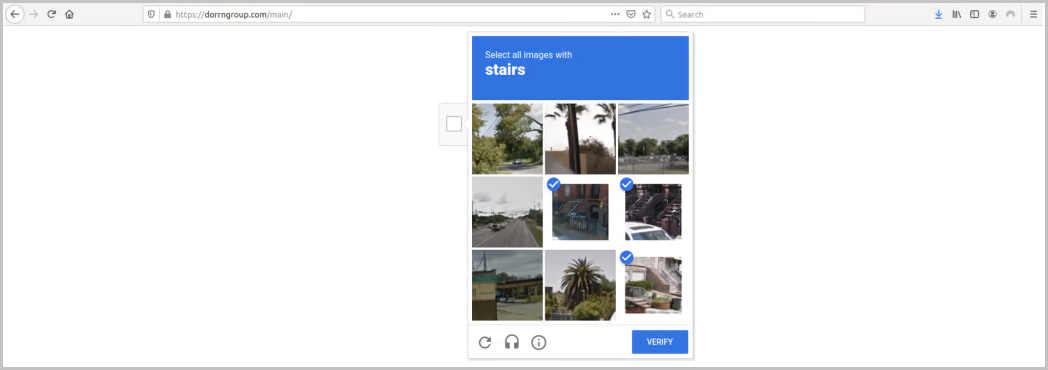
The CAPTCHA check was also used in a 2020 campaign that ZScaler’s ThreatLabZ researchers analyzed and it continues to be an effective middle step that helps increase the phishing success rate.
Also Read: Transfer Limitation Obligation: What every organization should know
Once the users pass this step, they are redirected to a genuine-looking phishing page that steals Microsoft Office 365 accounts.
.png)
Those careful enough would notice that the domain of the login page doesn’t belong to Microsoft or their organization and is one of the following:
This is why before submitting, or even before starting to type their username and password, users should always check and confirm they are on a real login portal and not a fake one.
Typically, recipients are logged into the account, which should make suspicious a request to log in once more to listen to the voicemail.
Voicemail-themed phishing using HTML attachments has been used since at least 2019, but it is still effective, especially with careless employees.