KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Microsoft Defender for Endpoint has been tagging Google Chrome updates delivered via Google Update as suspicious activity due to a false positive issue.
According to Windows system admins reports [1, 2, 3, 4], the security solution (formerly known as Microsoft Defender ATP) began marking Chrome updates as suspicious starting last evening.
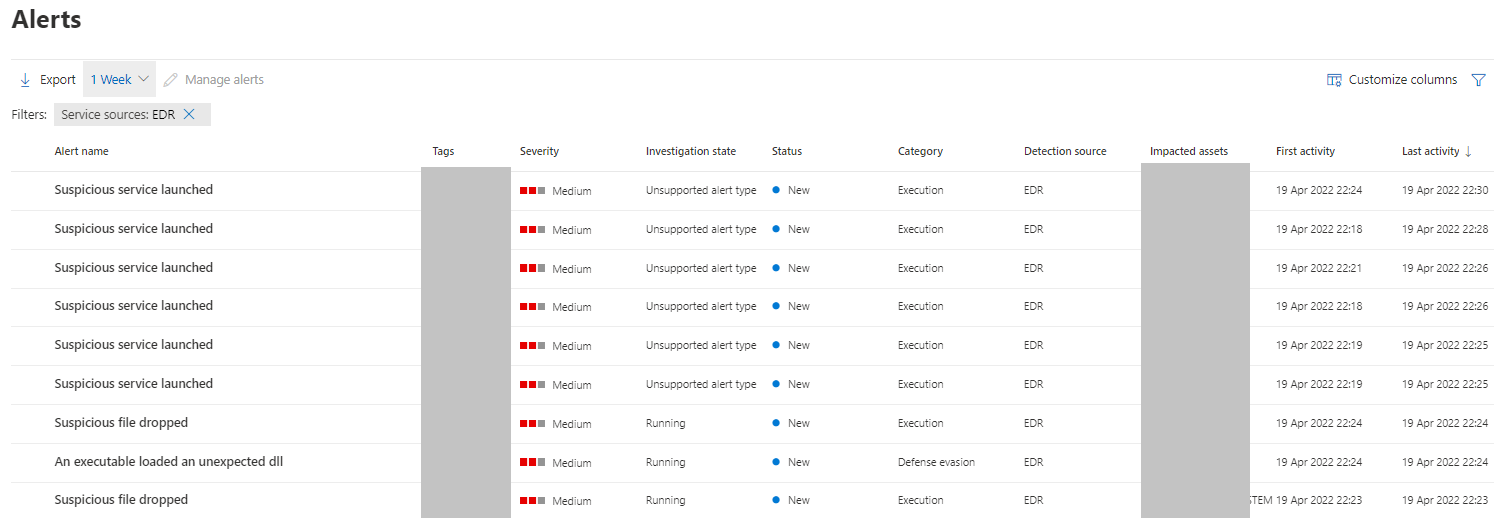
Those who encountered this issue reported seeing “Multi-stage incident involving Execution & Defense evasion” alerts on affected Windows endpoints monitored using Defender for Endpoint.
In a Microsoft 365 Defender service advisory issued after reports of these alarming alerts started showing up online, Microsoft revealed that they were erroneously triggered by a false positive and not due to malicious activity.
“Admins may receive a false positive alert for Google Update on Microsoft Defender for Endpoint monitored devices,” Microsoft said.
Also Read: 10 Tips For Drafting Key Terms In A Service Agreement
Roughly one and a half hours later, the advisory was updated, with Redmond saying the false positive issue was addressed and the service restored.
“We determined these are false positive results and we have updated the logic for this alert to resolve the issue some customers may have experienced,” a Microsoft spokesperson told BleepingComputer.
Windows admins have had to deal with multiple other Defender for Endpoint false positive issues during the last two years.
For instance, they were hit by a wave of Defender for Endpoint alerts where Office updates were tagged as malicious in warnings pointing to ransomware behavior detected on Windows endpoints.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
In November, Defender ATP blocked Office documents and some Office executables from opening or launching because of another false positive tagging the files Emotet malware payloads.
One month later, it mistakenly displayed “sensor tampering” alerts linked to the Microsoft 365 Defender scanner for Log4j processes.
Other similar Defender for Endpoint issues include alerts of network devices infected with Cobalt Strike and Chrome updates as PHP backdoors, both caused by false-positive detections.
Update: Added Microsoft statement.