KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Microsoft says tamper protection will soon be turned on by default for all enterprise customers in Microsoft Defender for Endpoint (MDE) for better defense against ransomware attacks.
The company added this feature to its enterprise endpoint security platform in March 2019 to block changes to key security features and prevent attackers or malicious tools from disabling the antimalware solution or deleting security updates.
Once toggled on, it locks Microsoft Defender Antivirus to secure default values and will prevent any security settings changes.
To do that, it blocks other apps from changing the settings for real-time and cloud-delivered protection, behavior monitoring, and Defender components like IOfficeAntivirus (IOAV) which handles the detection of suspicious files downloaded from the Internet.
Until now, tamper protection was turned on by default in Microsoft Defender after installing Windows home users.
Also Read: 5 Ransomware Singapore facts: What your organisation should know
However, it was only available as an optional MDE feature for enterprise customers that could only be enabled using the Intune management console (local administrators were blocked from toggling it on).
“Starting last year, to better protect our customers from ransomware attacks we turned on tamper protection by default for all new customers with Defender for Endpoint Plan 2 or Microsoft 365 E5 licenses,” said Josh Bregman, a Principal Product Manager at Microsoft.
“To further protect our customers, we are announcing that tamper protection will be turned on for all existing customers, unless it has been explicitly turned off in the Microsoft 365 Defender portal.”
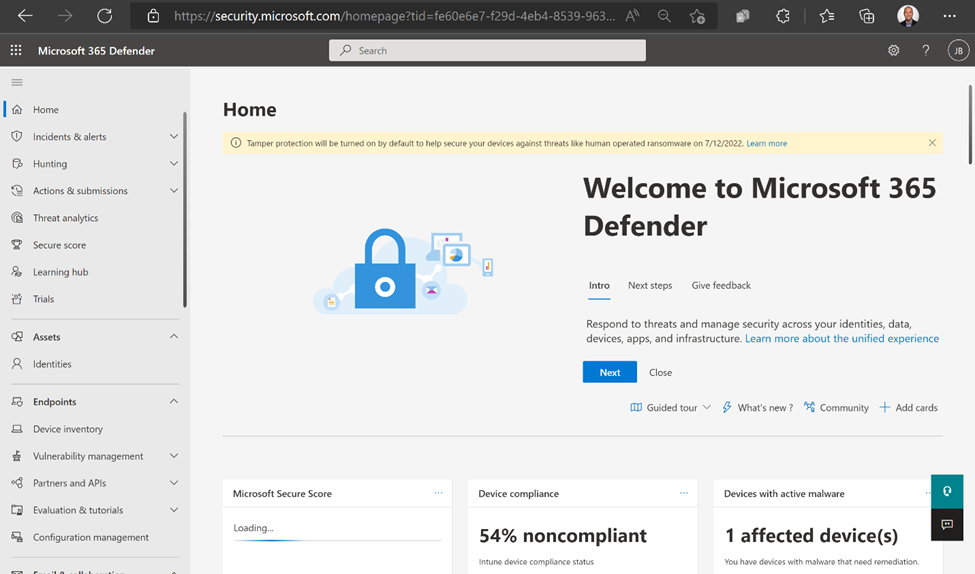
Customers who haven’t yet configured tamper protection in their environments will soon receive notifications alerting them that the feature will be turned on in 30 days.
Also Read: How GDPR Singapore impacts businesses and its compliance
For instance, public preview customers will receive an alert on September 21, 2022, saying that tamper protection will be toggled one month later, on October 24, 2022.
“We recommend that you turn tamper protection on and keep it enabled across your organization,” Bregman said.
However, he added, “if you prefer that tamper protection not be turned on automatically for your tenant, you can explicitly opt out.”
The steps needed to toggle off tamper protection manually require you to:
Admins can also exclude some devices from tamper protection if there’s an application compatibility concern by creating a profile in Microsoft Endpoint Manager or using Security Management for Defender for Endpoint.