KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The Microsoft Threat Intelligence Center (MSTIC) has disrupted a hacking and social engineering operation linked to a Russian threat actor tracked as SEABORGIUM that targets people and organizations in NATO countries.
Microsoft says that SEABORGIUM, also known as ColdRiver by Google and TA446 by Proofpoint, primarily target NATO countries but have seen campaigns in the Baltics, Nordics, and Eastern Europe regions, including Ukraine.
Believed to be a Russian state-sponsored hacking group, the threat actors attempt to steal sensitive emails from organizations and people of interest to Russia
“Within the target countries, SEABORGIUM primarily focuses operations on defense and intelligence consulting companies, non-governmental organizations (NGOs) and intergovernmental organizations (IGOs), think tanks, and higher education,” explains Microsoft in a report released today.
Also Read: 4 easy guides to data breach assessment
“SEABORGIUM has been observed targeting former intelligence officials, experts in Russian affairs, and Russian citizens abroad.”
SEABORGIUM creates online personas through email, social media, and LinkedIn accounts that are used in social engineering campaigns against targeted individuals and organizations.
Using the fake personas, the threat actors contact individuals of interest to strike up a conversation and build a rapport, ultimately leading with sending a phishing attachment.
Microsoft says they have seen the threat actors distributing the attachments via emails with attached PDFs, links to file hosting services, or to OneDrive accounts hosting the PDF documents.
Regardless of how the threat actors distribute the PDF, once opened, the attachment will show the victim a message stating that the document could not be viewed and that they should click on a button to try again.
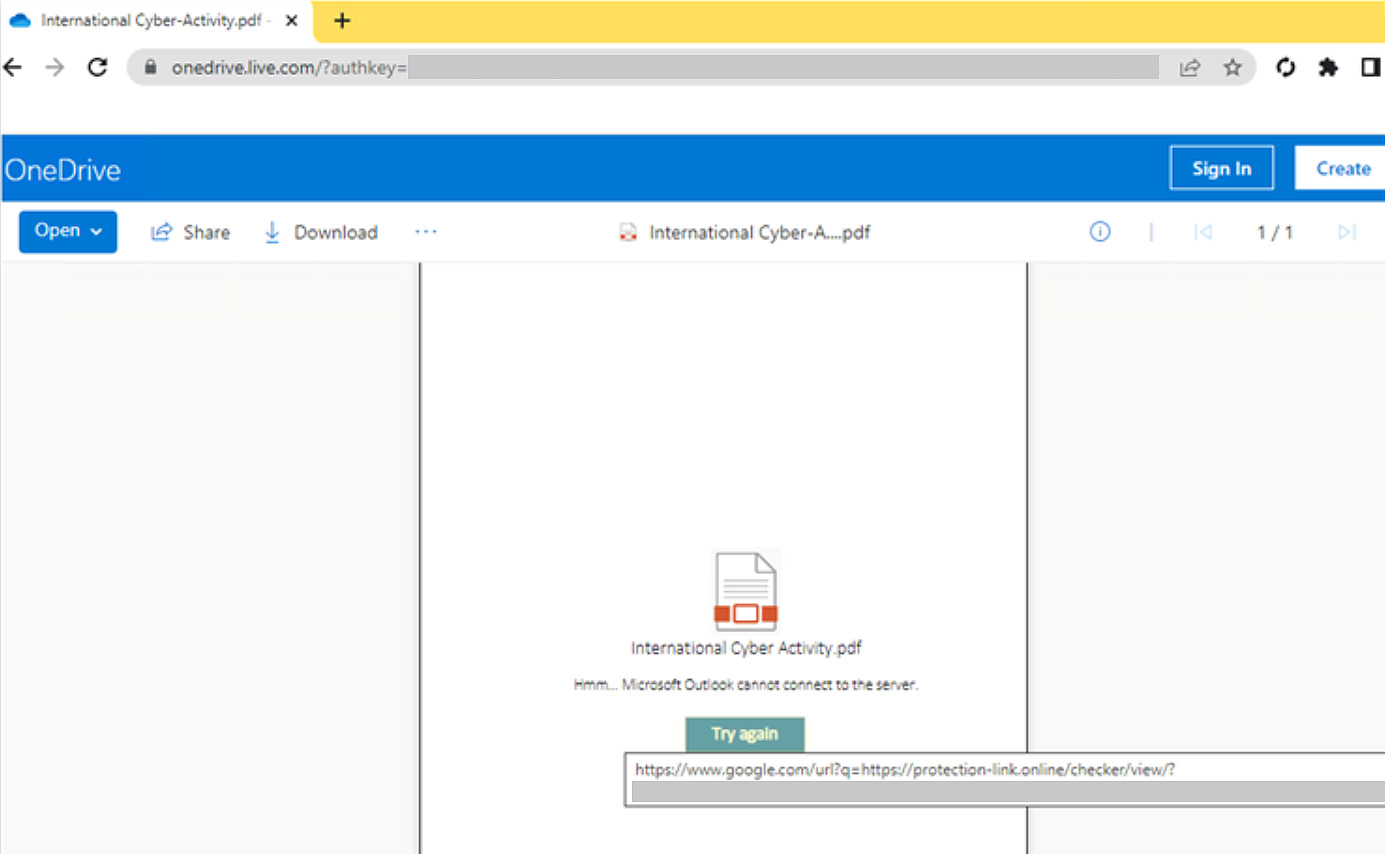
Clicking this button brings the victim to a landing page running phishing frameworks, such as EvilGinx, that to display a login form for the particular service.
Also Read: 7 Client Data Protection Tips to Keep Customers Safe
However, as EvilGinx acts as a proxy, the threat actors can steal the inputted credentials and authentication cookies/tokens generated after a user logs into their account.
These stolen authentication tokens allow the threat actors to log into a compromised user’s account even if 2FA is enabled.
Once the hackers gains access to the targeted email account, Microsoft says they either steal emails and attachments or set up forwarding rules to receive all new emails sent to the compromised account.
Microsoft has also seen the threat actors use the breached account to conduct conversations as the victim with other people of interest to gain access to sensitive information.
In May 2022, Google and Microsoft detected attacks conducted by the threat actors to steal documents from UK political organizations and activists.
In the campaign seen by Microsoft, SEABORGIUM stole documents from a UK political organization, which was then distributed on social media and a PDF sharing site.
In an attack disclosed by Reuters and Google, SEABORGIUM stole emails and documents from pro-Brexit activists, which were then leaked online.
Today, Microsoft says they have taken action to disrupt SEABORGIUM’s campaigns by disabling accounts used for surveillance, phishing, and email collection.
Microsoft also shared sixty-nine domains believed to be associated with the threat actor’s phishing campaigns used to steal credentials for Microsoft, ProtonMail, and Yandex accounts.
The complete list of domains can be found in Microsoft’s advisory, as well as safeguards that network defenders can use to prevent similar attacks.
Defenses include disabling email auto-forwarding in Microsoft 365, using the IOCs to investigate for potential compromise, requiring MFA on all accounts, and for more security, requiring FIDO security keys.
Microsoft has also released Azure Sentinel hunting queries [1, 2] that can be used to check for malicious activity.