KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft says that some of the Exchange Server flaws addressed as part of the August 2022 Patch Tuesday also require admins to manually enable Extended Protection on affected servers to fully block attacks.
The company patched 121 flaws today, including the DogWalk Windows zero-day exploited in the wild and several Exchange vulnerabilities (CVE-2022-21980, CVE-2022-24477, and CVE-2022-24516) rated as critical severity and allowing for privilege escalation.
Remote attackers can exploit these Exchange bugs to escalate privileges in low-complexity attacks after tricking targets into visiting a malicious server using phishing emails or chat messages.
“Although we are not aware of any active exploits in the wild, our recommendation is to immediately install these updates to protect your environment,” the Exchange Server Team warned.
Also Read: NDA Data Protection: The Importance, Its Meaning And Laws
However, Microsoft says that admins also need to enable Extended Protection (EP) after applying today’s security updates to make sure that threat actors won’t be able to breach vulnerable servers.
EP is a feature that enhances Windows Server auth functionality to mitigate authentication relay or “man in the middle” attacks.
“Customers vulnerable to this issue would need to enable Extended Protection in order to prevent this attack,” Redmond said in advisories published Tuesday.
“Please note that enabling Extended Protection (EP) is only supported on specific versions of Exchange (please see documentation for a full list of prerequisites).”
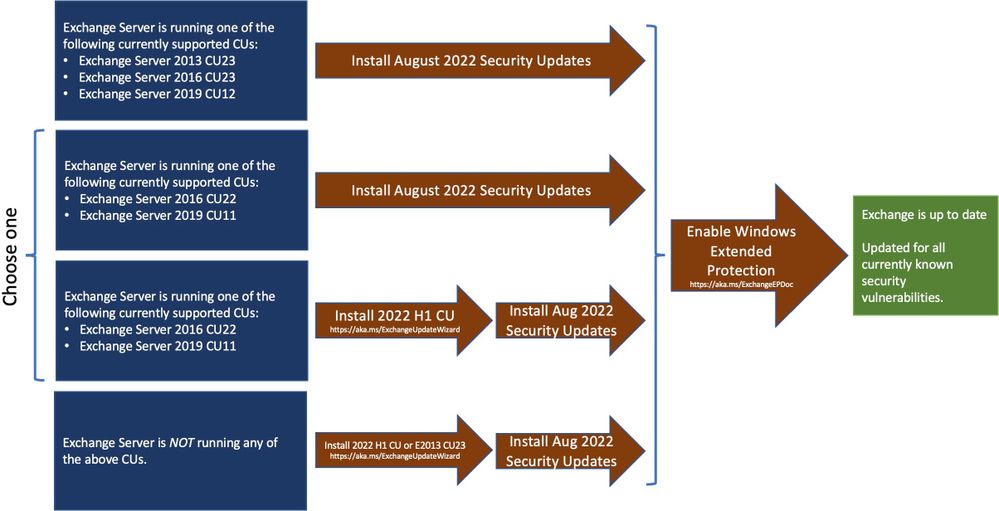
A script provided by Microsoft is available to enable this feature, but admins are advised to “carefully” evaluate their environments and review the issues mentioned in the script documentation before toggling it on their Exchange servers.
Also Read: Invasion of privacy elements and its legal laws to comply
Microsoft has issued security updates for multiple Exchange Server builds:
Since Redmond has also tagged all three Exchange vulnerabilities as “Exploitation More Likely,” admins should patch these flaws as soon as possible.
“Microsoft analysis has shown that exploit code could be created in such a way that an attacker could consistently exploit this vulnerability. Moreover, Microsoft is aware of past instances of this type of vulnerability being exploited,” the company says.
“This would make it an attractive target for attackers, and therefore more likely that exploits could be created. As such, customers who have reviewed the security update and determined its applicability within their environment should treat this with a higher priority.”