KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







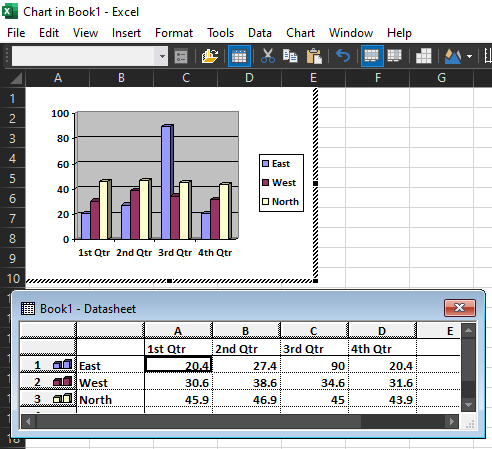
Microsoft today will release a patch for a vulnerability affecting the Microsoft Office MSGraph component, responsible for displaying graphics and charts, that could be exploited to execute code on a target machine.
Because the component can be embedded in most Office documents, an attacker can use it to deliver a malicious payload without the need for special functions.
Tracked as CVE-2021-31939, the security flaw is part of a larger set of security vulnerabilities that researchers at Check Point discovered in MSGraph and reported to Microsoft.
The reason the researchers focused on testing MSGraph for security flaws is that it contains code that is at least 17 years old and has an attack surface that is similar to Microsoft Equation Editor, where bugs fixed in 2017 continue to be heavily exploited to this day.
Also Read: Data Protection Officer Singapore | 10 FAQs
Details about the vulnerability are lacking at this point, as the bug received an identifier only recently. However, Check Point notes in a report today that CVE-2021-31939 is a use-after-free (UAF).
This type of flaw consists of incorrect use of dynamic memory during program operation and can lead to arbitrary code execution on the system.
According to the researchers, the issue is in a MSGraph file parsing function, which “is commonly used across multiple different Microsoft Office products, such as Excel (EXCEL.EXE), Office Online Server (EXCELCNV.EXE) and Excel for OSX.”
Check Point’s public disclosure today includes three other security flaws discovered in the Microsoft Office MSGraph component, all of them patched last month:
All the flaws were discovered through fuzzing, a testing technique where code is bombarded with various input to find errors and security vulnerabilities. The exceptions generated this way include crashes and memory leaks that could lead to exploitation.
The researchers say that all four vulnerabilities can be embedded in most Office documents, leaving room for multiple attack scenarios with the vulnerability being triggered once the victim opens a malicious Office file.
“If exploited, the vulnerabilities would grant an attacker the ability to execute malicious code on targets via specially crafted Office documents,” Check Point told BleepingComputer.
Also Read: The DNC Singapore: Looking At 2 Sides Better
“Since the entire Office suite has the ability to embed Excel objects, this broadens the attack vector, making it possible to execute such an attack on almost any Office software, including Word, Outlook and others” – Check Point
Check Point reported the vulnerabilities to Microsoft on February 28 and three of them were patched last month. CVE-2021-31939 received its tracking identifier at a later date and is scheduled to receive a patch today.