KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







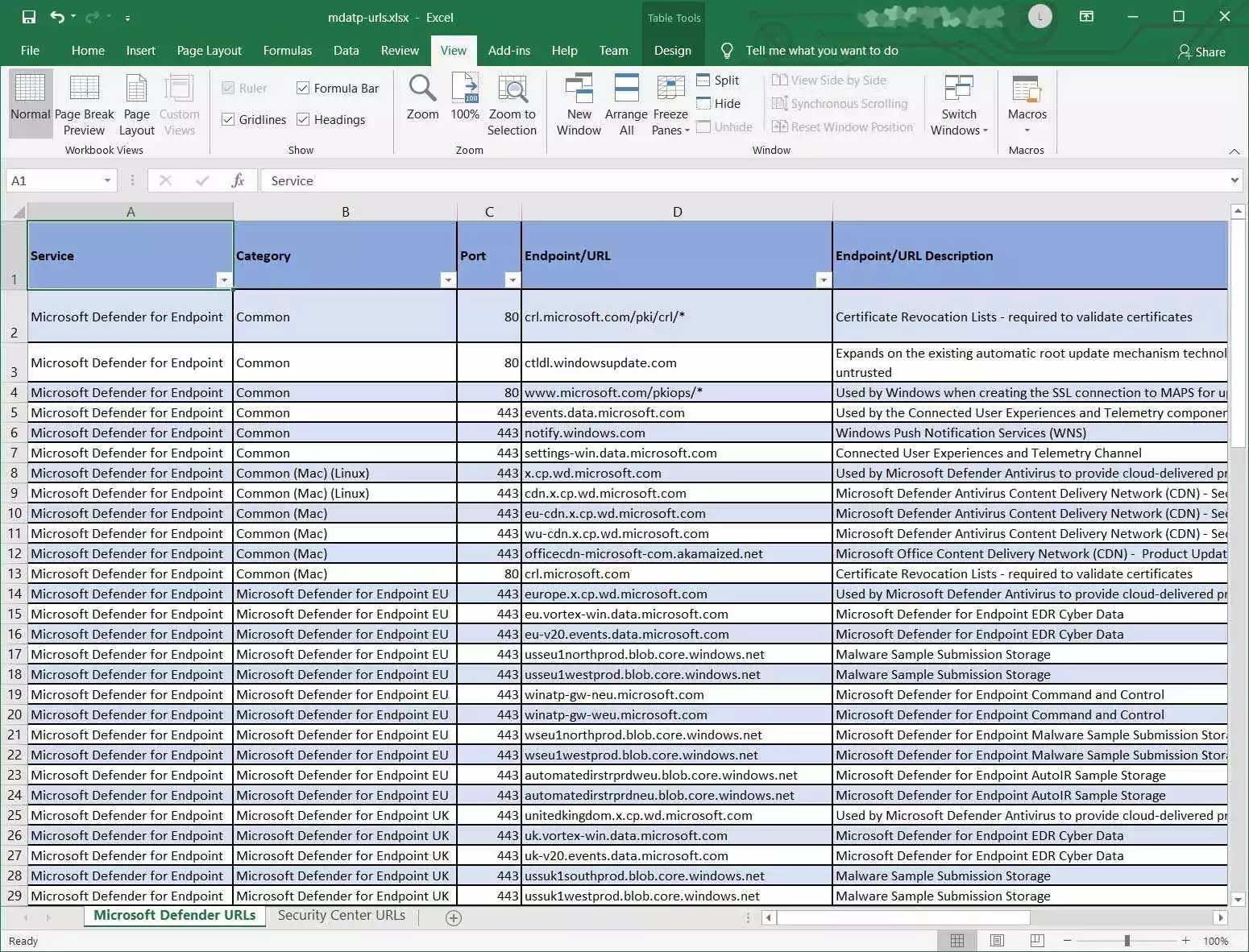
Microsoft has released a spreadsheet containing the full list of URLs that Microsoft Defender ATP must reach to function correctly.
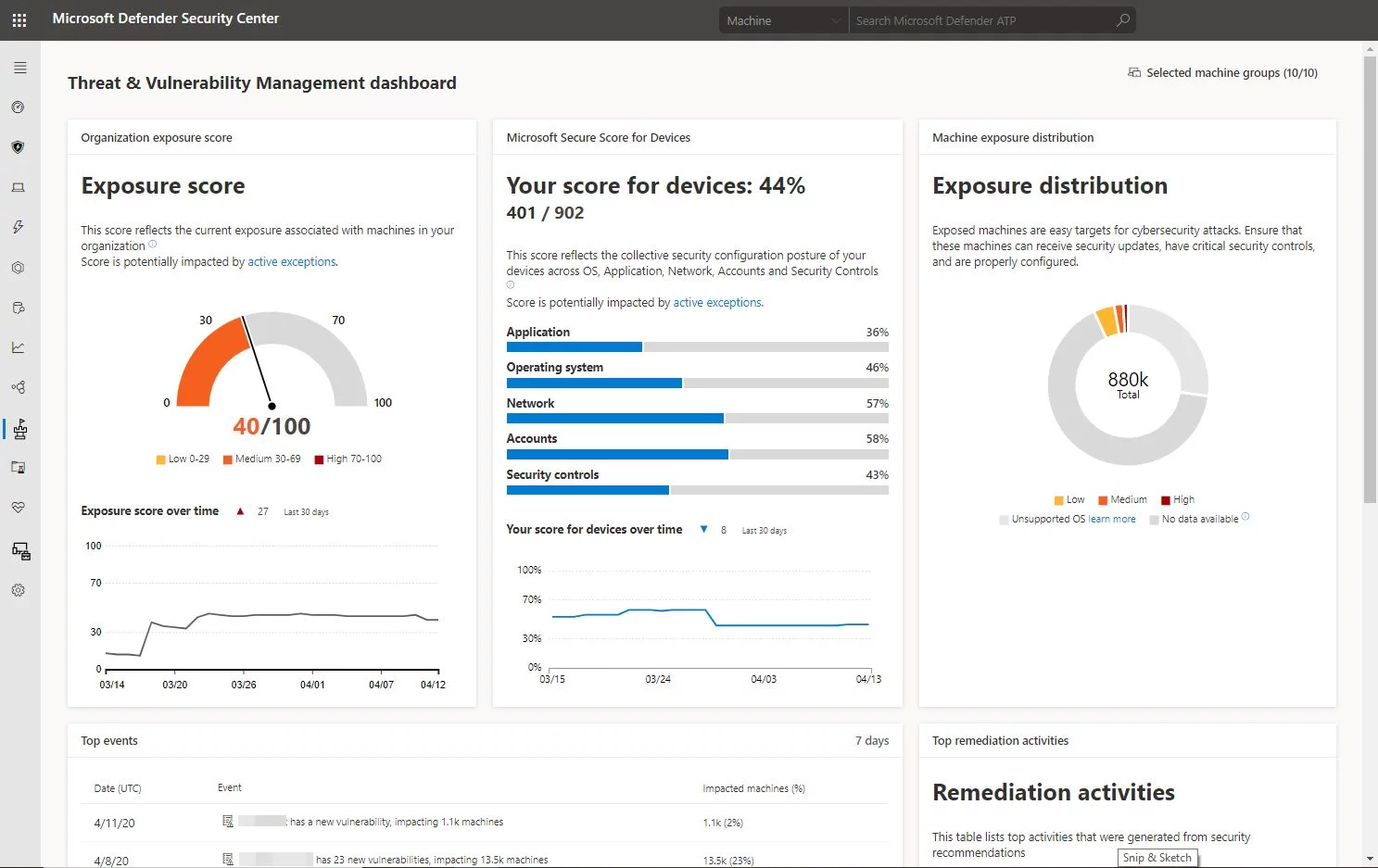
When Microsoft Defender ATP is installed on endpoints, its sensor will detect malicious threats and behaviors and send them via HTTP to the Microsoft Defender ATP cloud service.
This data is then aggregated in the Microsoft Defender Security Center portal, which provides enterprise admins an overview of malicious activity detected on their network.
Also Read: 10 Practical Benefits of Managed IT Services
For Microsoft Defender ATP to properly send collected data to Microsoft’s cloud-based services, there is ta list of URLs that must not be blocked.
“If a proxy or firewall is blocking all traffic by default and allowing only specific domains through, add the domains listed in the downloadable sheet to the allowed domains list.”
The following downloadable spreadsheet lists the services and their associated URLs that your network must be able to connect to. You should ensure that there are no firewall or network filtering rules that would deny access to these URLs, or you may need to create an allow rule specifically for them,” Microsoft explained in a support document for Microsoft Defender ATP.
Yesterday, Microsoft released an Excel spreadsheet containing 84 URL patterns required for Microsoft Defender ATP to function correctly.
Also Read: What is Pentest Report? Here’s A Walk-Through
If you use Microsoft Defender ATP in your organization, you must make sure your firewall or proxy server does not block these URLs or Microsoft Defender ATP will be unable to send sensor data to Microsoft.
To test if your implementation can connect to Microsoft Defender ATP servicing URLs, you can use the MDATP Client Analyzer tool.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
