KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Many well-known and heavily used web sites are using a fraud protection script that port scans your local computer for remote access programs.
Last weekend, news heavily circulated that eBay.com was port scanning visitors’ computers when they browsed their site.
This port scanning was conducted by the LexisNexis’ ThreatMetrix fraud protection script used to detect potentially hacked computers making fraudulent purchases.
When executed, a feature of this product uses WebSockets to scan 14 different TCP ports on a visitor’s computer.
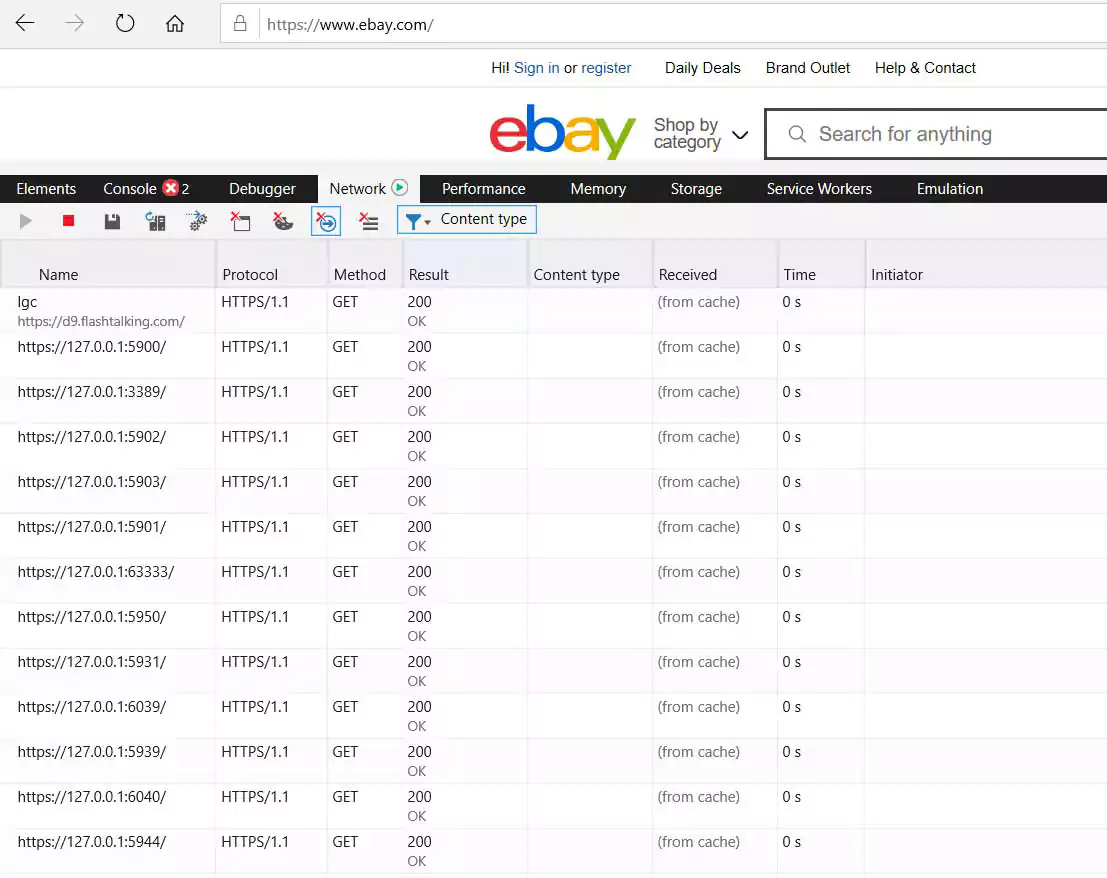
All of these ports are for remote access programs commonly used for legitimate reasons but are also known to be used for malicious purposes. These ports, their identifiers, and associated applications are listed below.
| Program | Ebay Name | Port |
|---|---|---|
| Unknown | REF | 63333 |
| VNC | VNC | 5900 |
| VNC | VNC | 5901 |
| VNC | VNC | 5902 |
| VNC | VNC | 5903 |
| Remote Desktop Protocol | RDP | 3389 |
| Aeroadmin | ARO | 5950 |
| Ammyy Admin | AMY | 5931 |
| TeamViewer | TV0 | 5939 |
| TeamViewer | TV1 | 6039 |
| TeamViewer | TV2 | 5944 |
| TeamViewer | TV2 | 6040 |
| Anyplace Control | APC | 5279 |
| AnyDesk | ANY | 7070 |
BleepingComputer has still not been able to identify the targeted program on port 63333. Based on the name ‘REF,’ we believe this is a reference port for tests.
While every e-commerce site should use methods to detect fraud, many found that it was too intrusive to port scan a visitor’s computer for programs without permission.
To see what other sites may be using this script, BleepingComputer reached out to DomainTools, a cybersecurity company specializing in web domain and DNS threat intelligence.
When web sites load ThreatMetrix’s anti-fraud scripts, they load the script via a customer-named online-metrix.net hostname.
For example, eBay’s site loads the ThreatMetrix script from src.ebay-us.com, a CNAME DNS record for h-ebay.online-metrix.net.
DomainTools was able to provide BleepingComputer with a list of 387 unique online-metrix.net hostnames that are named similarly.
Using this list, BleepingComputer visited the sites for many of the larger companies and checked if they were port scanning our computers when visiting.
While none are as large as eBay in terms of visitors, many of the sites using ThreatMetrix’s anti-fraud scripts are well-known brands.
Of the sites we tested, we saw Citibank, TD Bank, Ameriprise, Chick-fil-A, Lendup, BeachBody, Equifax IQ connect, TIAA-CREF, Sky, GumTree, and WePay port scanning our computers.
 |  |
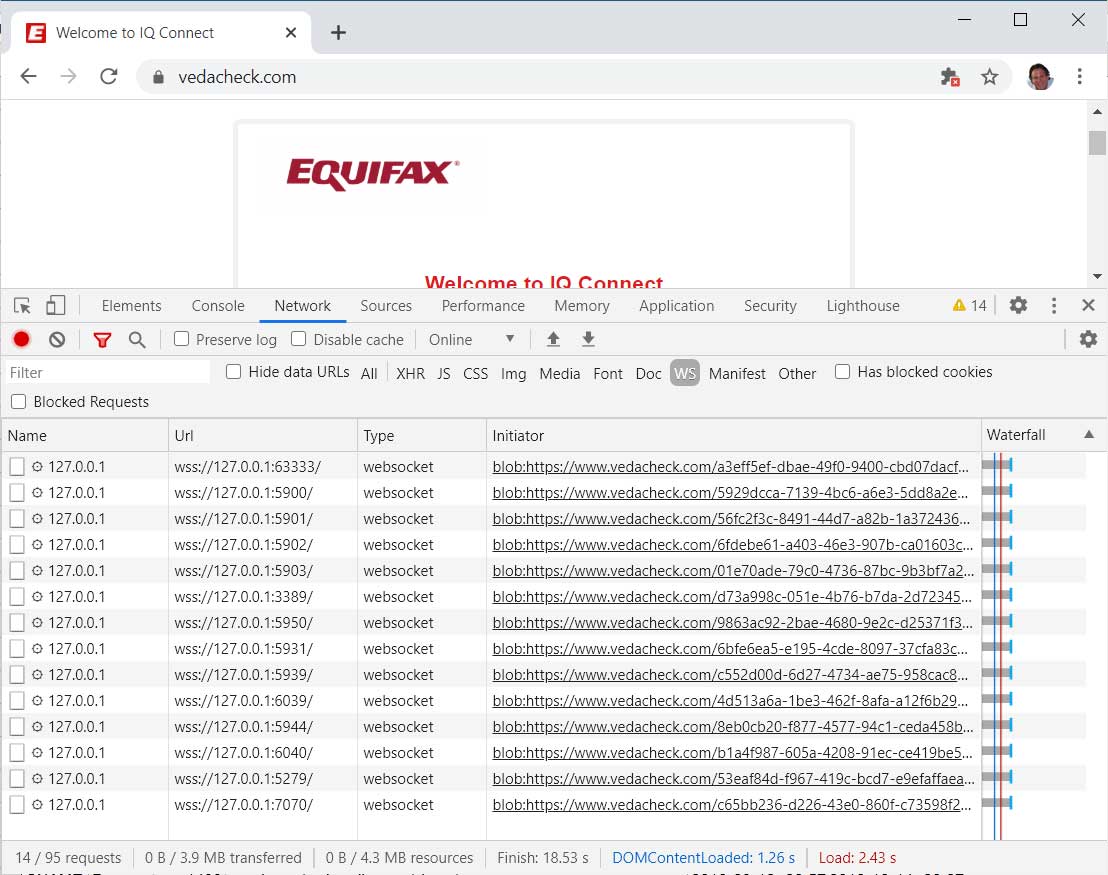 | 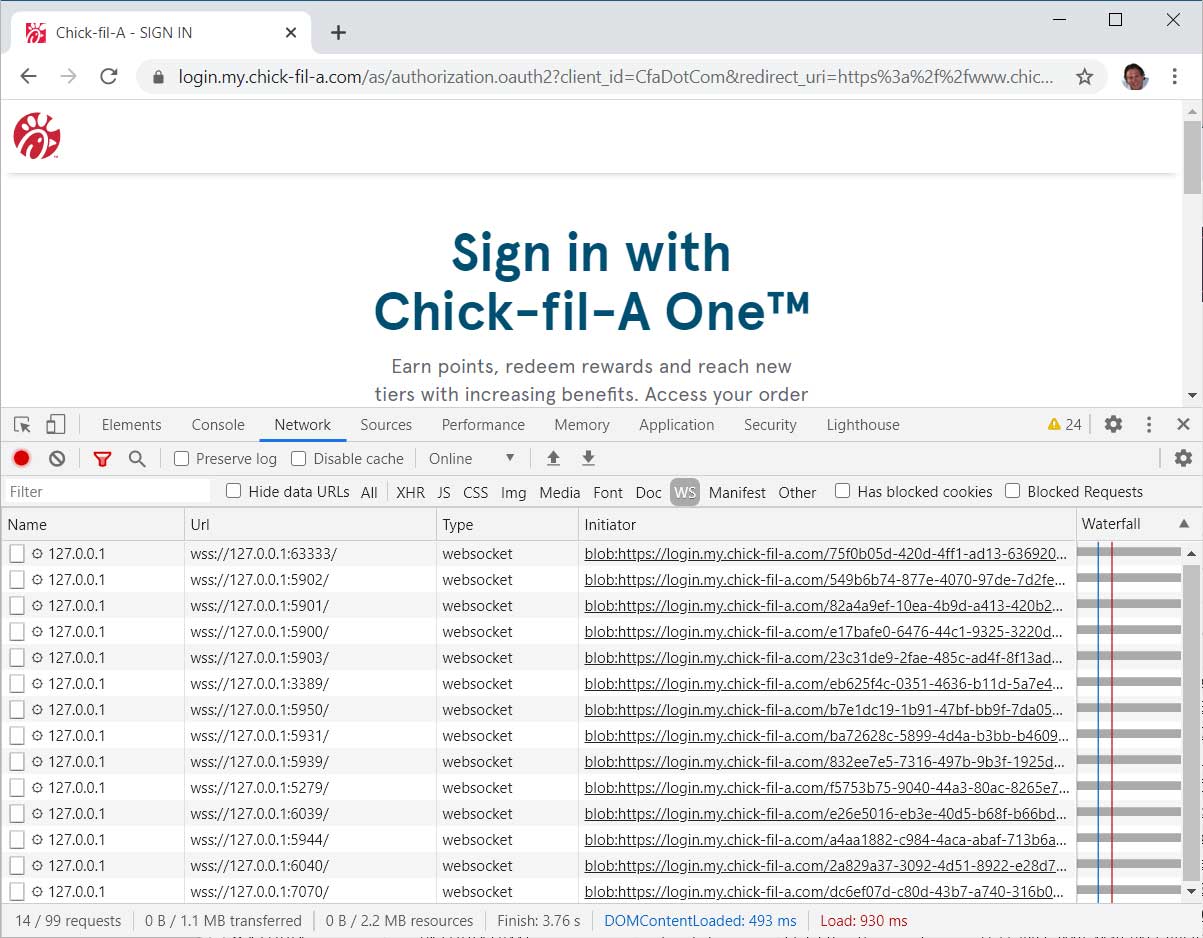 |
| Sites port scanning our computers. Click to enlarge |
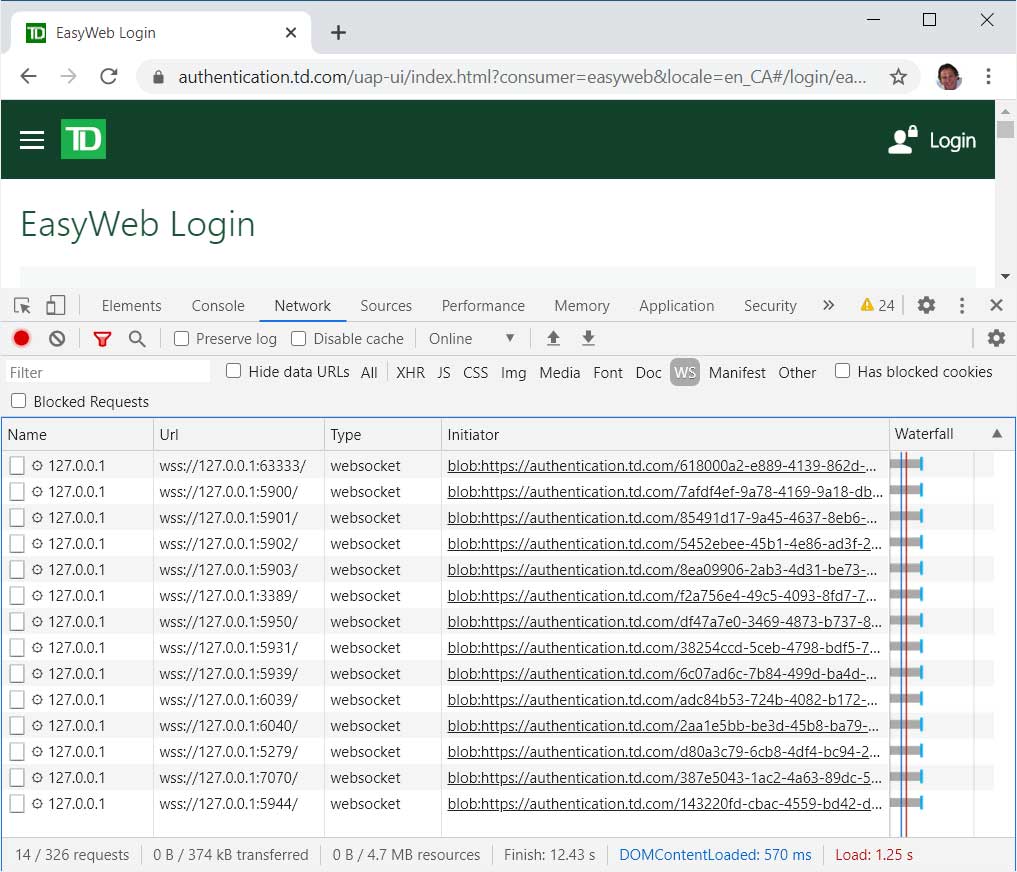
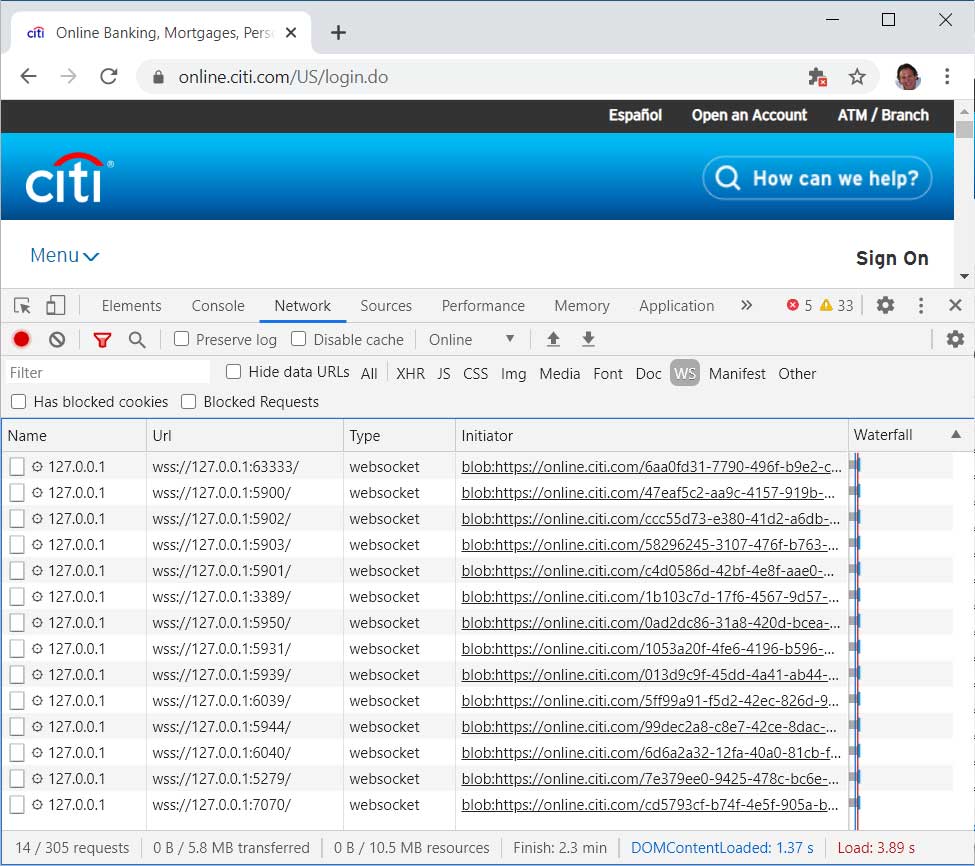
When using the port scanning script, it was done differently depending on the site.
For example, Citibank, Ameriprise, and TIAA-CREF immediately port scanned our computers when visiting the main page of the site.
TD Bank, Chick-fil-A, Lendup, Equifax IQ connect, Sky, GumTree, and WePay only port scanned visitors who tried to log in.
For BeachBody.com, they only port scanned when checking out.
Based on the list of domains we received, other well-known companies are using the ThreatMetrix script.
This list includes Netflix, Target, Walmart, ESPN, Lloyd Bank, HSN, Telecharge, Ticketmaster, TripAdvisor, PaySafeCard, and possibly even Microsoft.
We could not get the port scan feature to trigger on these sites, but it may have been used on a page we did not visit.
The list of the unique hostnames shared with us by DomainTools can be found in this Google sheet.
While we have a good feeling that these port scans are being used to detect potentially hacked computers, we reached out to NexisLexis and to some of the companies listed above to confirm.
Unfortunately, we did not hear back from any of them at the time of this publishing.
If you find these port scans to be intrusive and a privacy risk, you can utilize the uBlock Origin adblocker in Firefox to block them.
In our tests, uBlock is unable to block the port scans in the new Microsoft Edge or Google Chrome as the extension does not have adequate permissions to uncloak the DNS CNAME records.
We also tested the Brave Browser, and the port scans were allowed through, as seen below.
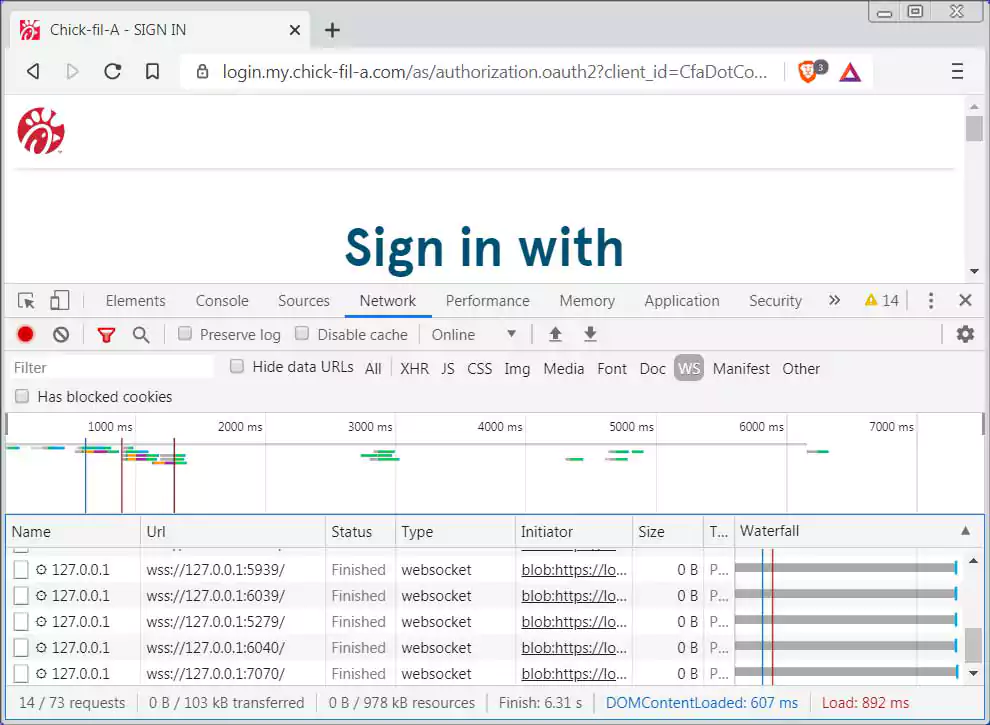
If you have a different experience with these browsers, please let us know.
Update 5/30/20 12:37 PM EST: Added a link to a Google Sheets containing the list of hostnames provided by DomainTools