KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Confidential documents are those which are unsuitable for the general public, or those not directly related to the case, to have access to. They may be personal information about a client your firm has represented, information about a person’s credit score or medical files. Depending on your line of work, you may have a variety of confidential documents on hand.
Thus, you must destroy confidential documents after a certain period of time. According to the Health Insurance Portability and Accountability Act of 1996,(HIPAA).
Confidential documents are any documentation that has information about a customer or client. It can include information about their case, their job, financial information or health information.
If you work in a healthcare field, you are required to remain patient confidentiality. This means that you cannot disclose information about them to anyone who is not authorized. If you work in another line of work, confidential documents must be kept so in order to protect not only the privacy but information pertaining to financial documents.
It is a wise idea to have a filing cabinet with a lock on it. Or, if you have a large number of confidential documents, your office itself should have a lock to ensure no one who is not authorized can grab them and read them. Make sure documents are kept away from potentially prying eyes, even before you take steps to destroy them.
In some cases, it is to prevent identity theft. It can also prevent the theft of confidential information from your business. In other cases it is mandated by law. If you work in an area where this is the case, you will be aware of this.

Gain access to a crosscut shredder. This protects you from would-be thieves of this information from reconstructing the complete pages from the strips. When shredding sensitive documents it is important to use a crosscut shredder, because it produces thinner strips of paper. Shred the documents. Once you have a satisfactory shredder, you must know how to destroy documents by begin sending all of your documents through the device’s mouth. Continue until all of your documents are done. If you have more documents than the machine can hold at one time, be sure to take the ribbons of paper out before continuing.
Separate the pieces into separate bags. Take a portion of each document and place them in separate bags. Beyond reducing them to unrecognizable small pieces, this is one further security measure. This way, any would be thieves cannot find matches within the same bag; they will have to sort through everything.
Dispose of them on the scheduled day. If garbage is picked up from your house/business on a Monday, don’t put this out on a Tuesday. You want to leave as little time as possible between when the garbage goes out and when it is collected. Ideally you will keep it inside until the day of collection, and bring it down just before the city employees arrive.
Place the documents in a large trashcan. You will want a container tall and wide enough to easily contain all of the documents and liquids you are pulping. Similarly, the material needs to be strong enough so that it won’t deteriorate or lose its form when in contact with bleach and water. Since you will be using roughly 22L of liquid to dissolve the documents, choose a trashcan that is greater than or equal to 30L. This will give you enough room to properly churn the documents. Plastic trashcans work well and can withstand the effects of diluted bleach.
Pour in ½ Gallon (2L) of bleach. Many stores sell brand name and generic bleach with a 8.25% concentration; this is perfect for your purpose. Bleach is going to help break down the paper. This will guarantee a more complete destruction of any secure information in your documents.
Add 5 Gallons (19L) of water. Although bleach is the more chemically harmful (and stronger) part of this mixture, simple water is doing a lot of the work. Once the paper is completely saturated, you’ll be able to reduce it to an unrecognizable pulp.
Push the documents down into the bleach water. All the documents need to be submerged so they are completely saturated and can be broken down. If you have more documents that liquids, then you can do one of two things: work in smaller batches, or work with a larger container. If you choose the latter, make sure you increase your proportions of water and bleach to match.
Let the documents sit for 24 hours. Sitting in the bleach-water solution for 24 hours will effectively break down the sensitive documents and make them easy to pulp. If this is an emergency situation, and/or the documents need to be destroyed more quickly, consider using other methods here.
Blend the documents with a paint turbine mixer. After waiting 24 hours, the documents should be soft and discolored. Using an electric mixer, blend the paper until it becomes a soft, uniform mash.
Lay out in sunlight to dry. Putting the pulp directly into bags may lead to leakage and could possibly be rejected by the garbage men. Instead, lay out a large plastic tarp and pour the pulp evenly over the surface. Allow the pulp to dry completely before disposing of it.
Dispose of the pulp. Place the dried remains in garbage bags and leave them out with the regular trash. Anyone who goes digging through your garbage – such as identity thieves – will be hard pressed to learn anything from your pulped documents. Pulp can also be composted.
Set up an outdoor fire pit. Standard fire pits on how to destroy documents are ideal for burning documents because they stand off the ground and have top covers. This allows for better airflow, which leads to a more complete burn of your documents. Also, it somewhat prevents the escape of document fragments from the fire.
Start a fire. You can even use the sensitive documents as fire starter. Once the kindling is lit, add progressively larger pieces of wood until you have a stable burn.
Place the sensitive documents in the fire. Don’t dump them all at once; this could cause small pieces of information to fall by the side. Burn individual pieces, holding them with metal tongs, to ensure they are completely burned. With a stable fire, you can place more of the documents in at once and allow them to burn, protected by the wood.
Check the ashes. Once you think everything is burned and the fire is out, shift through the ashes and look for any unburned paper. The easiest to spot will be paper that somehow still has a white sheen. However, also be on the lookout for pieces that have turned grey, but still have legible text. Even these must be burnt more completely.
Burn any remaining pieces. Gather all the sensitive debris and store it in a safe, closed compartment until you have the fire burning again. Using protective fire gloves, or long metal tongs, securely place the document fragments in the fire’s center.
Scatter the ashes. Wait for the fire to go out, and for the ashes to cool to a safe temperature. Using a shovel, gather them in a bag that will not rip. If you have a yard, scatter the ashes evenly throughout your yard.
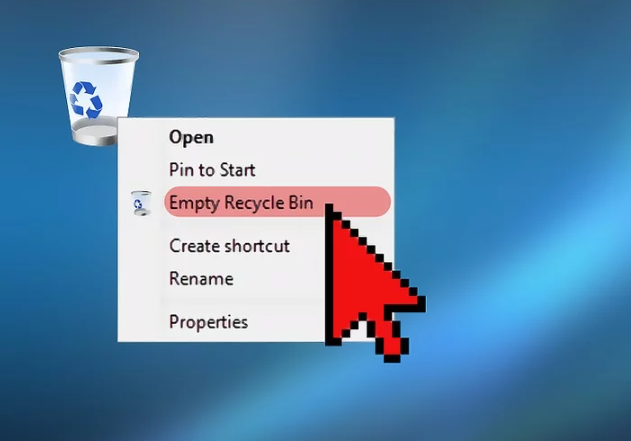
Delete the documents. Locate all the files on your hard drive containing sensitive data. Right click and send them to the trash. Empty your trash. If there is no risk that someone will use more advanced techniques to retrieve your data, this is an acceptable and simple method.
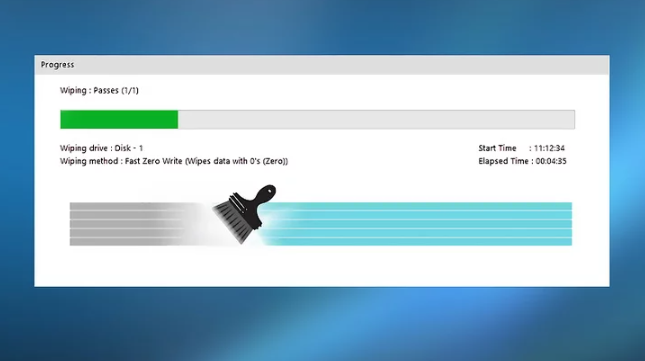
Overwrite the hard drive. All the information on your hard drive is represented in binary numbers: 1’s and 0’s. This is the computer’s language. Overwriting programs – available online – go through and replace all the information on your hard drive with random strings of 1’s and 0’s. If you decide to choose this method, be advised it is semi-permanent and it may be impossible to recover the data in question.
Degauss the hard drive. Degaussing refers to exposing magnet-based technology like hard drives to a powerful magnetic field that destroys the data. Ideally it will entirely get rid of the device’s magnetic charge and make it impossible to use. Purchasing your own degausser can cost up to $4000. However it is possible to rent one or pay for the professional services of IT companies.
Physically destroy the hard drive. The most complete method available is physical destruction. Hammering, high heat, and drilling are all acceptable methods. Whatever method you choose, first remove the hard drive from any outer framework. If hammering, apply extreme force directly on top of the hard drive. If drilling, ensure that you punch several holes directly through the drive.
Permanently delete emails. Select all the emails containing sensitive information and then select “delete” or “trash” depending on the program. Many online mail services – such as Gmail – will hold onto “deleted” files for 30 days before rendering them unrecoverable to users. Once you’ve deleted the emails, another way on how to destroy documents go directly to the “Deleted Messages” and “Trash” sections to see if there are any recoverable versions of your email. If so, delete these too.
Clear your browser history. It’s possible you want to prevent others from knowing what websites you’ve been visiting. Many browsers like Chrome, Firefox, and Internet Explorer have this option. Another tip on how to destroy documents is to go through the “menu” option to locate your history and delete any incriminating history.
The answer to the question of how to dispose of confidential documents is varied, depending on your company’s policies and the volume of the files. One solution on how to destroy documents is to hire an outside company to do it for you.
Some people may feel uncomfortable with hiring an external company. This is especially the case if their confidential information is extremely confidential or could have a last effect if leaked. However, there are many companies available that can help your business get rid of any documents necessary. An ethical company will destroy documents to the proper standard without leaking any information.