KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Fraudsters bypassed Google’s protections for the official Play Android store and published more than 20 fake modpacks for the popular game Minecraft.
The apps are just empty shells designed to lure kids and teenagers that want to modify their gameplay. They do not deliver any malware but once installed, they make normal use of the phone almost impossible.
Once installed, the bogus modpacks started to display full-screen advertisements aggressively. In at least one case, the sample would open a browser window with ads every two minutes.
Depending on the commands received from the server, the apps could also open Google Play, Facebook, or play YouTube videos, putting more money into the operator’s pockets with each display.
Also Read: Key PDPA Amendments 2019/2020 You Should Know
Security researchers at Kaspersky detected this operation in July and found that the most successful of the fake modpacks had more than one million installations.
The fraudsters tried to keep their operation under the radar by publishing the apps under different developer names and attempted to boost their ranking by using bots that left top-star reviews.
When real users started installing them, though, one-star reviews starting pouring in because the apps did absolutely nothing. It is difficult to label this discrepancy anything but suspicious.
In a report today, Igor Golovin from Kaspersky says in some instances the same description was used, “down to the typos,” a mistake that helped the researcher in his investigation.
Golovin says that when closing one of these fake Minecraft modpacks caused its icon to disappear from the phone screen. Many users complained about this behavior in their reviews.
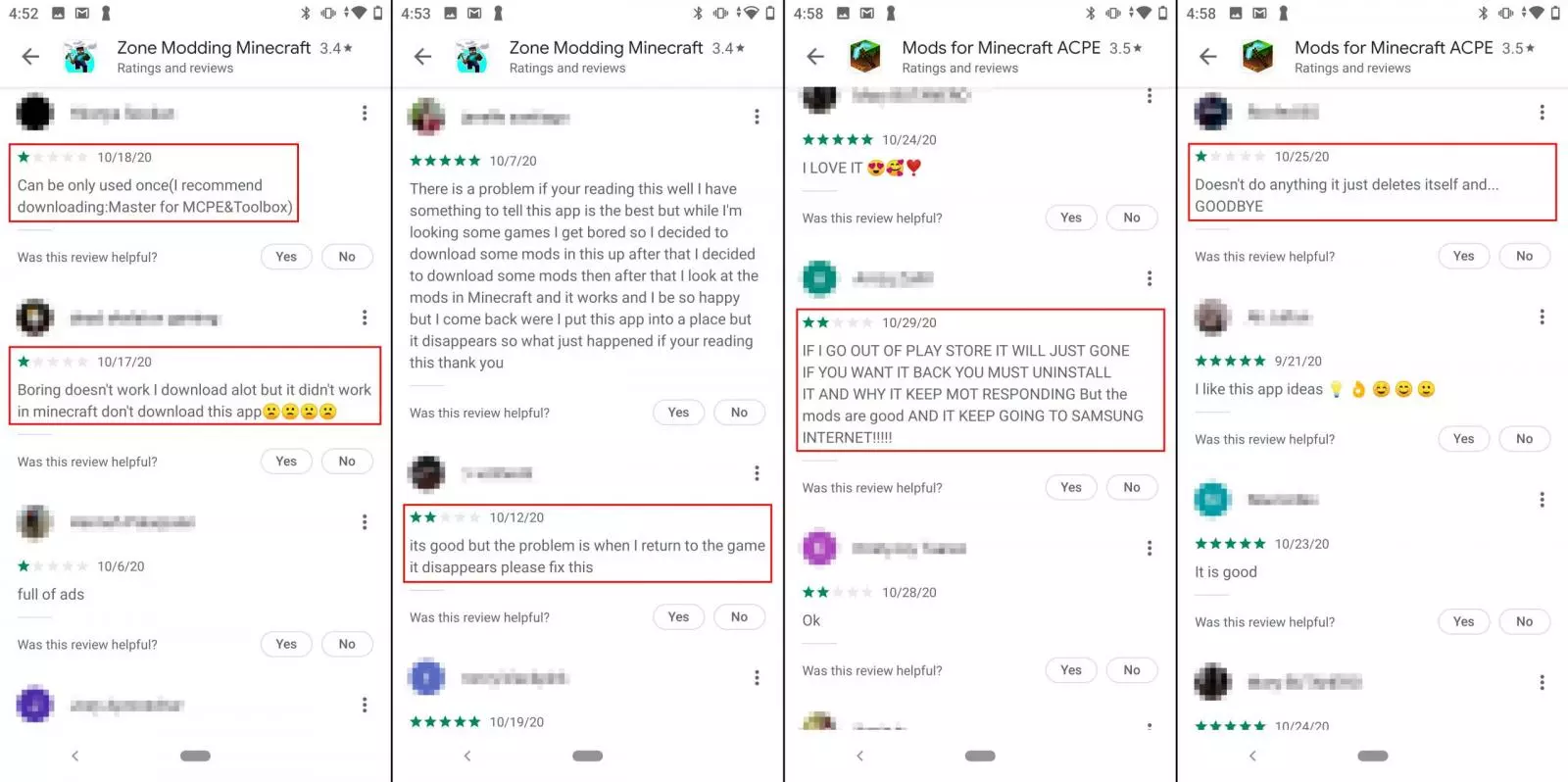
Not realizing the scam and believing that the app removed itself from the device, some users asked the developer for a fix. Obviously, they kept seeing the fraudulent ads.
“Because the “modpack” seemed glitchy from the start, most users, especially kids and teens, won’t waste time looking for it. They may even forget it and not bother trying to remove it”
– Igor Golovin
The right way to get rid of the malicious apps is to remove them from the Apps menu under device Settings. Luckily, these bogus modpacks are not too advanced and do not try to restore themselves.
The fraudulent apps are no longer in Google Play but this does not stop them from delivering ads on devices that still have them.
Minecraft players should be careful about installing modifications packages for the game from unofficial stores, even if they are widely regarded as safe, where these fraudulent apps are still available.
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
Below are the last five that Google removed from the official Android store, which are still present in other Android markets:

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
