KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A massive fraudulent advertising business disrupted recently perpetrated through more than 240 apps in Google Play generated profits that could amount to more than $150,000 per day.
For months, the army of deceptive apps, mostly low-quality games or stolen Nintendo Entertainment System (NES) emulators, was present in the official Android store, raking over 14 million installations.
While their behavior was not malicious, they disrupted the user experience by displaying out of context (OOC) ads, which appear to come from legitimate apps on the phone.
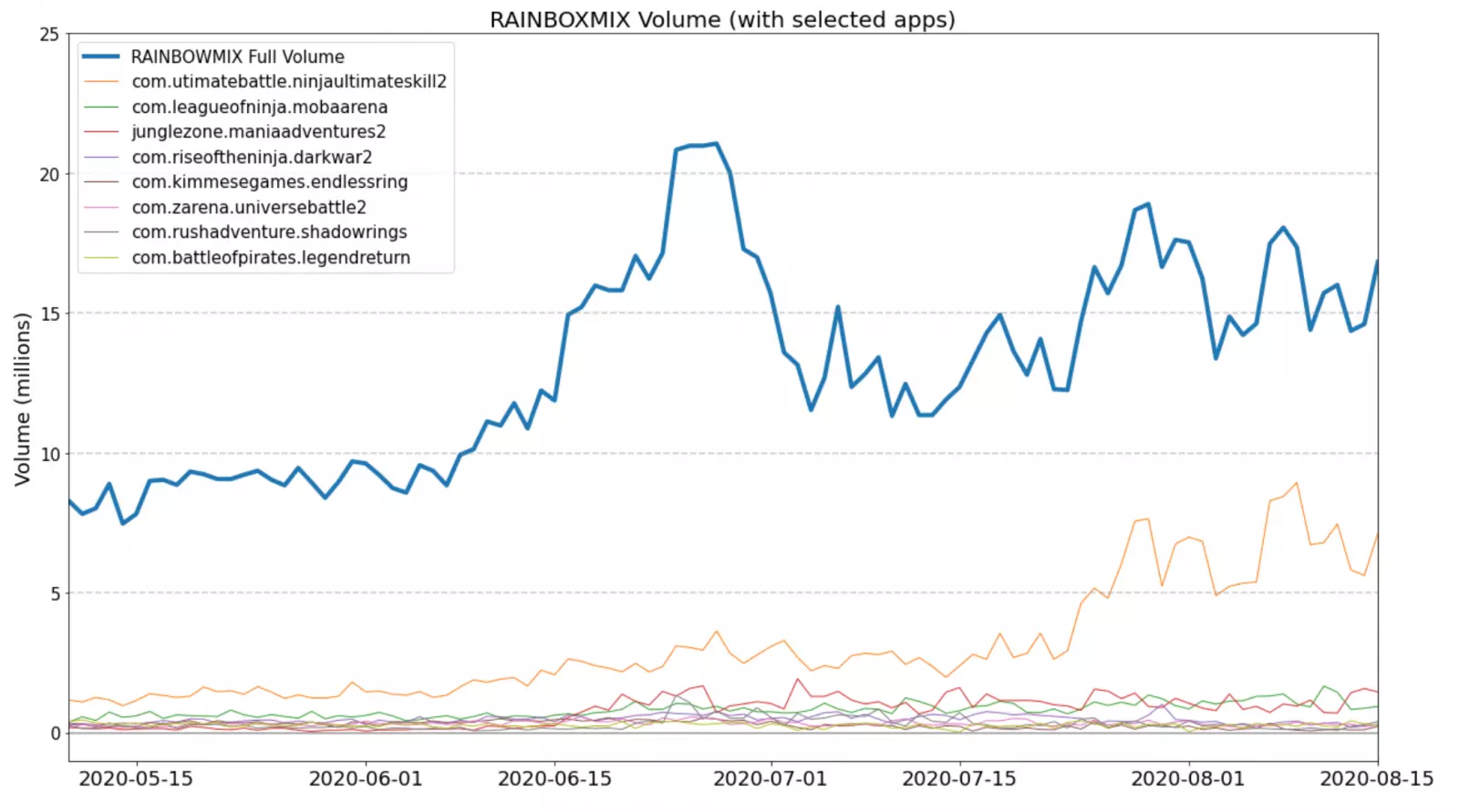
Security researchers at bot mitigation and fraud prevention company White Ops named this assortment of apps RainbowMix, due to the 8-16 bit games distributing the invasive ads.
OOC ads are not new but have become widespread this year and appear on the screen when the user is not active in the app that generates them.
In the case of RainbowMix, the apps pretend to be from popular apps and social media platforms like YouTube and Chrome.
Also Read: What Legislation Exists in Singapore Regarding Data Protection and Security?
An example is below, courtesy of White Ops, where the ad pretends to be from YouTube and takes over the entire phone screen:
Gabriel Cirlig, the lead researcher on RainbowMix, says that at its peak, this operation garnered more than 15 million ad impressions per day. After August 21, White Ops saw this many daily ad impressions consistently, from the RainbowMix app collective.
Although it is difficult to translate this into profit, even if the fraudsters received one cent per view, they would make at least $150,000 on the best days.
In a paper today, the researcher says that the code for the OOC ads was present in packages from legitimate Android and Unity software development kits (SDKs).
This helped them keep mostly undetected when inspected by researchers or static analysis engines. However, what contributed to a low detection rate was the use of the Tencent Legu packer.
“All RAINBOWMIX apps are packed with various versions of the Tencent Legu packer. While some of the apps are detected as malicious on multi-scanning platforms, these detections are often vague and only relate to the use of the specific packer, and not their behavior when unpacked” – White Ops
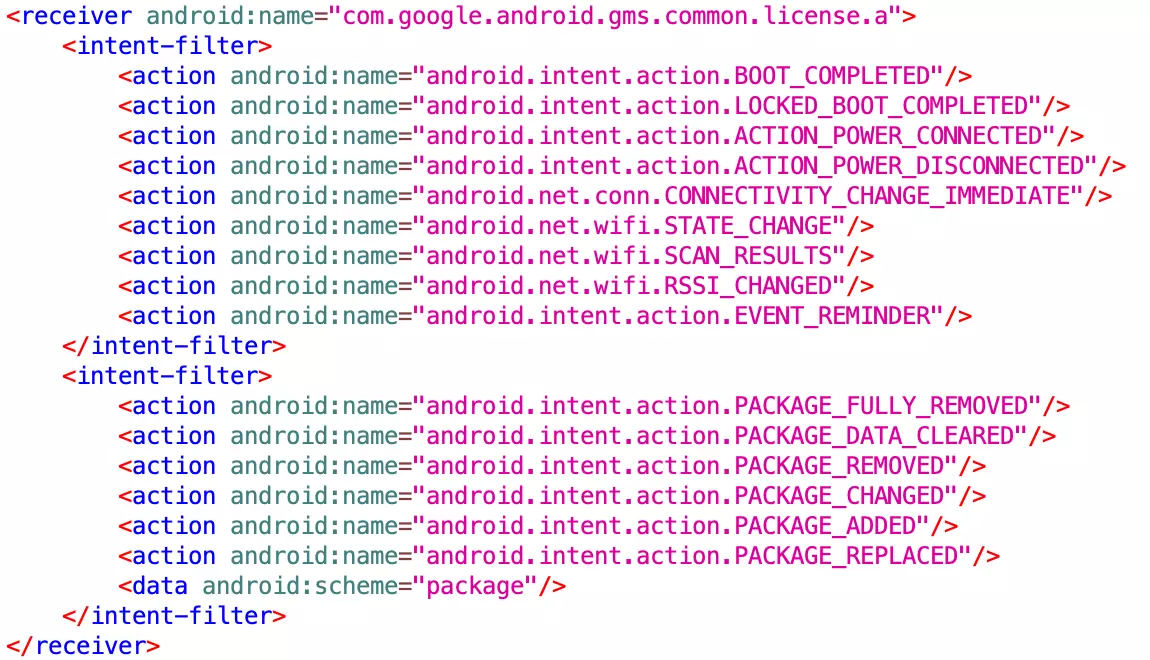
Taking a closer look at the apps, Cirlig noticed in their manifest (a document with build details about the app) that services and receivers responded to more triggers than normal:
system boot connection changes charging cable plug in/outs app installations
The researcher says that the code responsible for this resided in familiar packages but had no purpose in the apps. He believes that it was an obfuscation layer designed to create confusion during analysis.
The RainbowMix apps had code that tracked the current state of the screen (on/off). This way, the delivery of the ads occurred at the right time, and the impressions were valid, increasing the revenue.
Also Read: The Importance Of Knowing Personal Data Protection Regulations
The command and control (C2) server instructing the RainbowMix app to display the OOC ad was a hacked domain (pythonexample[.]com) that no longer serves content but is active until February 27, 2021.
Cirlig found that a JSON payload was downloaded from the C2 server immediately after installing a RainbowMix app. The file determined the ad network and the display frequency on the phone (every 10 minutes).
The RainbowMix apps were present in the Android Play store for up to a year and Google promptly removed all of them at the end of August following White Ops’ responsible reporting.