KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A ransomware operation has started to utilize a new tactic to extort their victims: DDoS a victim’s website until they return to the negotiation table.
A distributed denial of service (DDoS) attack is when a threat actor floods a website or a network connection with a large volume of requests to make a service inaccessible.
After negotiations stalled in a recent ransomware attack, a SunCrypt ransomware affiliate DDoSed a victim’s website.
When the victim logged back into the ransomware’s Tor payment site, they were greeted by a message stating that SunCrypt was responsible for the DDoS and will continue the attack if negotiations do not continue.
“At the moment your website is down due to the efforts of our tech. Please send us a message asap or further actions will be taken,” the SunCrypt ransomware operator warned a victim.
Also Read: How Bank Disclosure Of Customer Information Work For Security
When the victim asked why they were taking their website down, the ransomware operators stated that it was to force negotiations.
“We were in thr [sic] process on the negotiations and you didn’t show up so further actions were taken,” the threat actors stated.
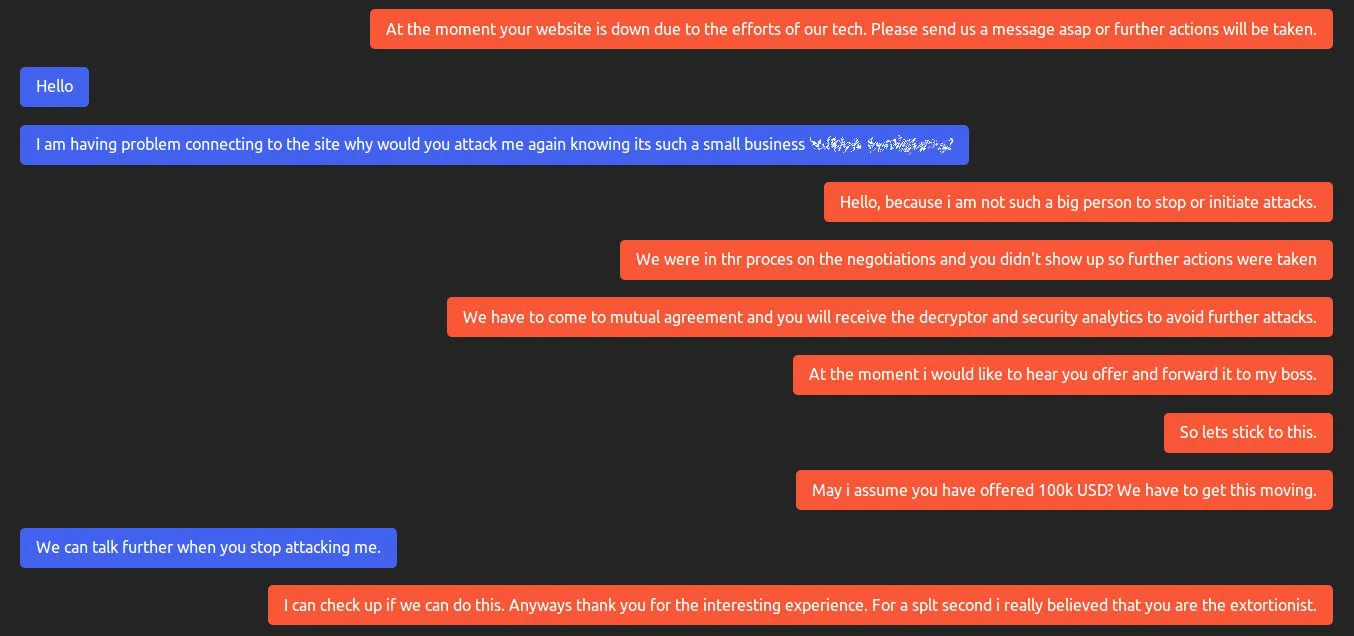
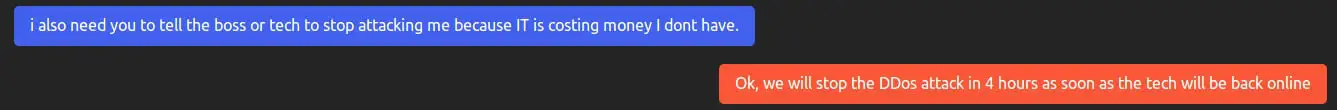
After the victim began ransom negotiations again, the ransomware operator agreed to have the “tech” turn off the DDoS attack.
MalwareHunterTeam, who shared the chat with BleepingComputer, told us that this tactic ultimately led to the victim paying the ransom.
This tactic was particularly effective against this victim as they were a smaller organization that was already greatly affected by the ransomware attack.
By combining data theft, the threat of a data breach, lack of access to encrypted files, and now a DDoS attack, a smaller victim could have their operation completely shut down.
This is another example of ransomware gangs updating their tactics to increase pressure on their victims so that they feel there is no choice but to pay the ransom.
Also Read: Data Protection Officer Duties And Responsibilities