KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A critical stack-based Buffer Overflow vulnerability has been discovered in SonicWall VPNs.
When exploited, it allows unauthenticated remote attackers to execute arbitrary code on the impacted devices.
Tracked as CVE-2020-5135, the vulnerability impacts multiple versions of SonicOS ran by hundreds of thousands of active VPNs.
Craig Young of Tripwire Vulnerability and Exposure Research Team (VERT) and Nikita Abramov of Positive Technologies have been credited with discovering and reporting the vulnerability.
Given an increase in employees working remotely and the reliance on corporate VPNs, easily exploitable flaws like these are concerning when it comes to security.
Also Read: The Importance Of DPIA And Its 3 Types Of Processing
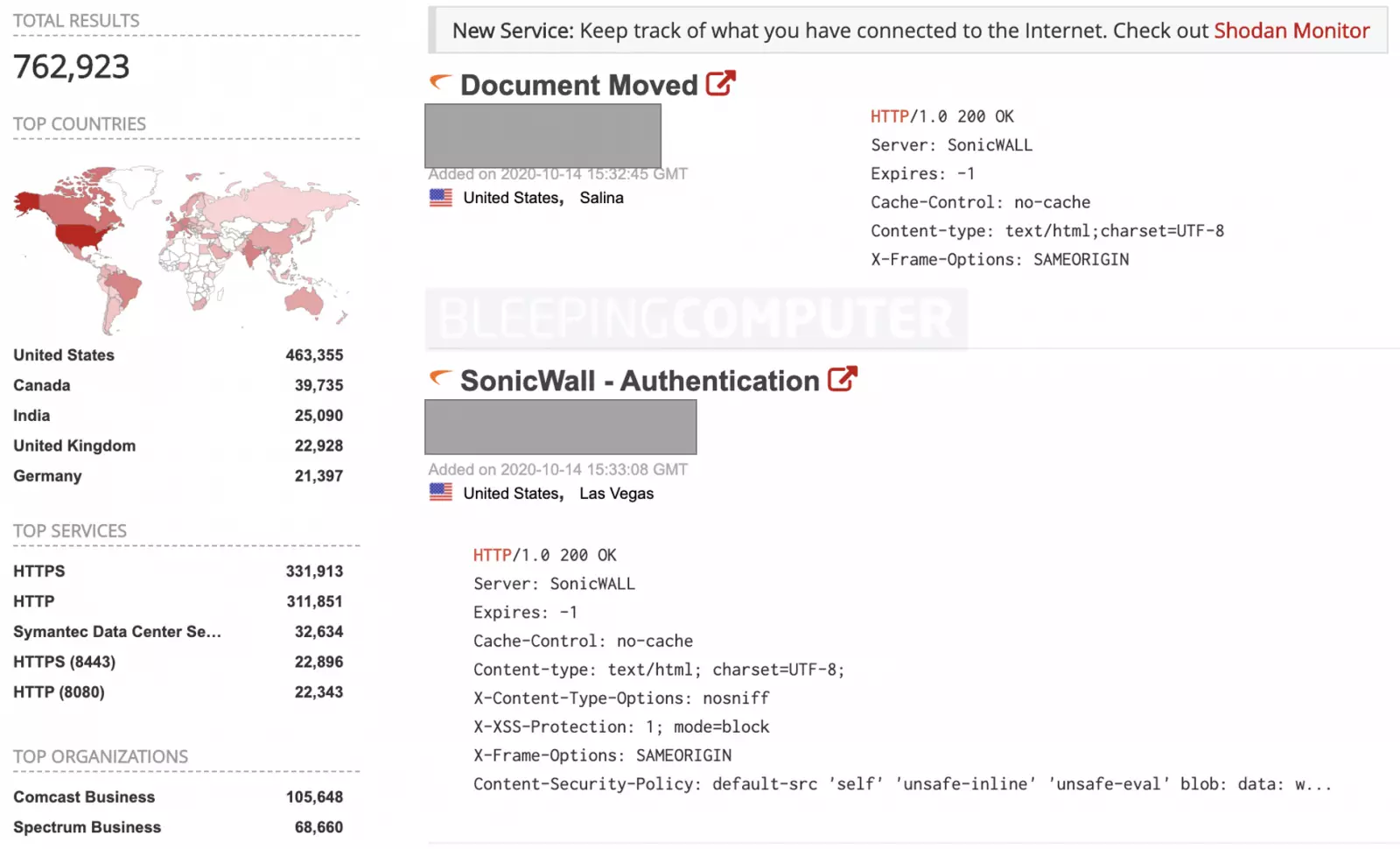
As confirmed by Tenable researchers and observed by BleepingComputer, as of today, Shodan shows over 800,000 VPN devices running vulnerable SonicOS software versions, depending on the search term used.
Although a Proof-of-Concept (POC) exploit is not yet available in the wild, the vast attack surface available to adversaries means companies should upgrade their devices immediately.
The following SonicWall VPN devices are impacted by CVE-2020-5135:
“SonicWall has released updates to remediate this flaw. SSL VPN portals may be disconnected from the Internet as a temporary mitigation before the patch is applied,” stated Tripwire VERT’s advisory.
Also Read: Data Storage Security Standards: What Storage Professionals Need To Know
The following versions are available to upgrade to for safeguarding against this vulnerability:
Provided the vast number of devices that are still running the outdated SonicOS versions and the critical nature of this vulnerability, complete research findings on CVE-2020-5135 are expected to be released once enough users have patched their systems.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
