KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






HP has published security advisories for three critical-severity vulnerabilities affecting hundreds of its LaserJet Pro, Pagewide Pro, OfficeJet, Enterprise, Large Format, and DeskJet printer models.
The first security bulletin warns about about a buffer overflow flaw that could lead to remote code execution on the affected machine. Tracked as CVE-2022-3942, the security issue was reported by Trend Micro’s Zero Day Initiative team.
Although it comes with a severity score of 8.4 (high), as calculated with the Common Vulnerability Scoring System (CVSS), HP lists the bug’s severity as critical.
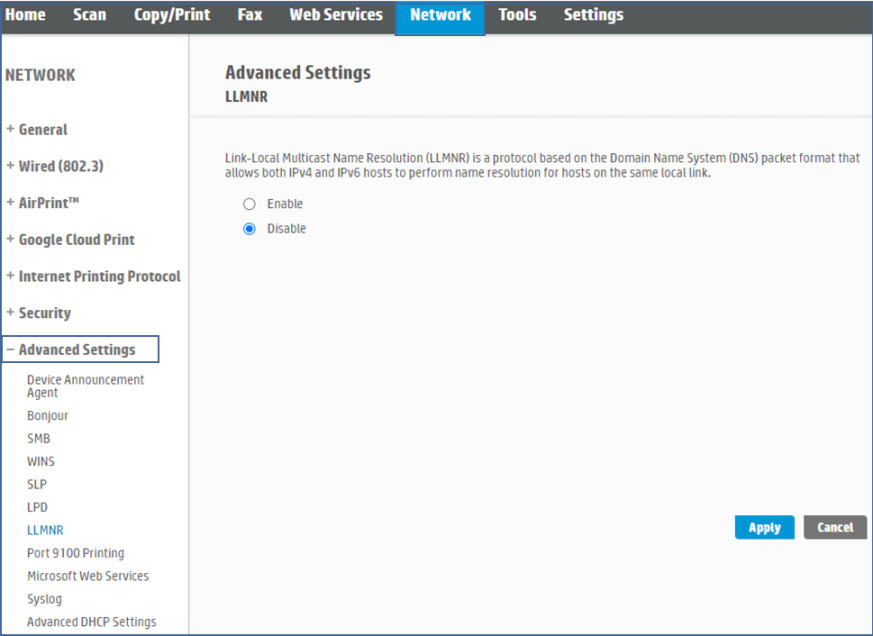
“Certain HP Print products and Digital Sending products may be vulnerable to potential remote code execution and buffer overflow with the use of Link-Local Multicast Name Resolution or LLMNR.” reads the advisory.
Also Read: What is cybersecurity? 5 best cybersecurity practices to follow
HP has released firmware security updates for most of the affected products. For the models without a patch, the company provides mitigation instructions that revolve mainly around disabling LLMNR (Link-Local Multicast Name Resolution) in network settings.
The steps for disabling unused network protocols using the embedded web server (EWS) for LaserJet Pro are available here. Other product categories may follow the guide published here.
A second security bulletin from HP warns about two critical and one high-severity vulnerability that could be exploited for information disclosure, remote code execution, and denial of service.
The three vulnerabilities are tracked as CVE-2022-24291 (high severity score: 7.5), CVE-2022-24292 (critical severity score: 9.8), and CVE-2022-24293 (critical severity score: 9.8). Credit for reporting them also go to the Zero Day Initiative team.
In this case too, the official recommendation is to update your printer firmware to the designated versions, but this isn’t available for all impacted models.
Also Read: What is ransomware and how ready is your business from it?
There’s no mitigation advice to remediate the problem for one of the listed LaserJet Pro models, but it has been marked as pending, so the security updates for that one should become available soon.
Admins of all other models may visit HP’s official software and driver download portal, navigate to select their device model, and install the latest available firmware version.
While not many details have been published about these vulnerabilities, the repercussions of remote code execution and information disclosure are generally far-reaching and potentially dire.
As such, it is recommended to apply the security updates as soon as possible, place the devices behind a network firewall, and impose remote access restriction policies.