KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Zoho has addressed a new critical severity vulnerability that affects the company’s Desktop Central and Desktop Central MSP unified endpoint management (UEM) solutions
ManageEngine Desktop Central is an endpoint management platform that allows admins to deploy patches and software over the network and troubleshoot them remotely.
Zoho has fixed the security flaw tracked as CVE-2021-44757 today and is now providing mitigation with the latest released Desktop Central and Desktop Central MSP versions (build Build: 10.1.2137.9).
“An authentication bypass vulnerability that can allow a remote user to perform unauthorized actions in the server,” Zoho’s ManageEngine Team explained in a notification published today.
Also Read: December 2021 PDPC Incidents and Undertaking: Lessons from the Cases
“If exploited, this vulnerability may allow an attacker to read unauthorized data or write an arbitrary zip file on the server.”
The company also advised customers to follow its security hardening guidelines for Desktop Central and Desktop Central MSP.
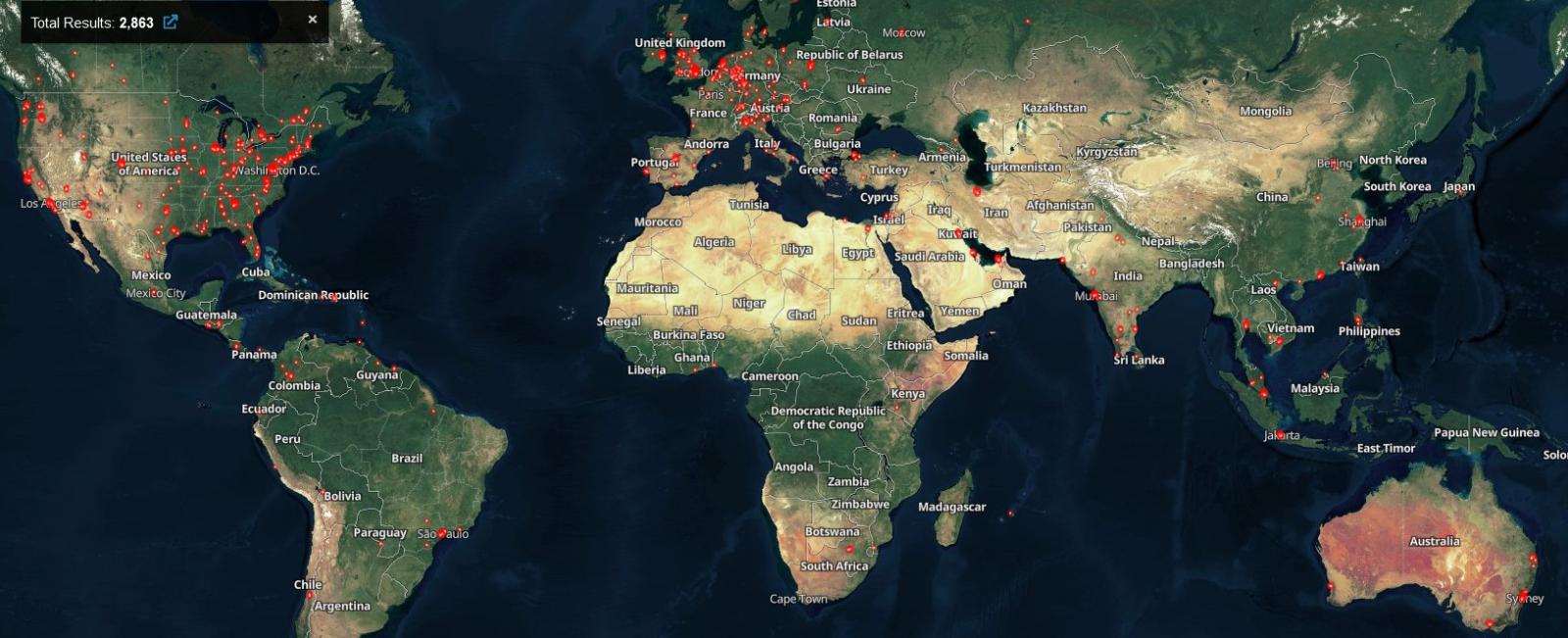
Today, a Shodan search revealed more than 2,800 ManageEngine Desktop Central instances exposed to attacks over the Internet if not patched.
In early December, Zoho patched another critical vulnerability (CVE-2021-44515) that could allow threat actors to bypass authentication and execute arbitrary code on unpatched ManageEngine Desktop Central servers.
The Indian business software provider also warned at the time that it found evidence in the wild exploitation and urged customers to update as soon as possible to block incoming attacks.
In late December, the FBI’s Cyber Division confirmed Zoho’s ongoing exploitation alert by warning that multiple APT groups have been exploiting the CVE-2021-44515 flaw since at least late October 2021.
This is not the first time Zoho ManageEngine servers have been targeted in attacks recently. Desktop Central instances, in particular, have been hacked before and access to compromised networks sold on hacking forums since at least July 2020.
Between August and October 2021, state hackers targeted Zoho ManageEngine products using tooling and tactics similar to ones observed in attacks coordinated by the APT27 Chinese-backed threat group.
Also Read: Digging deep: The Cybersecurity Act of Singapore
Their attacks focused on and led to the breach of networks belonging to critical infrastructure organizations worldwide in three different campaigns using:
Following these series of attacks, CISA and the FBI issued joint advisories (1, 2) warning of state-backed hacking groups exploiting ManageEngine vulnerabilities to drop web shells on critical infrastructure orgs’ networks from healthcare, financial services, electronics, and IT consulting industries.