KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A 16-year-old security vulnerability found in an HP, Xerox, and Samsung printers driver allows attackers to gain admin rights on systems using the vulnerable driver software.
“This high severity vulnerability, which has been present in HP, Samsung, and Xerox printer software since 2005, affects hundreds of millions of devices and millions of users worldwide,” according to a SentinelOne report published today and shared with BleepingComputer in advance.
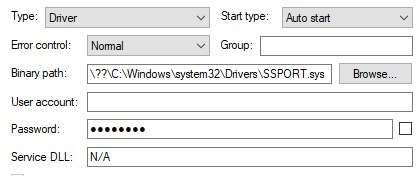
The security flaw tracked as CVE-2021-3438 is a buffer overflow in the SSPORT.SYS driver for specific printer models that could lead to a local escalation of user privileges.
Also Read: Data Protection Policy: 8 GDPR Compliance Tips
As the researchers discovered, the buggy driver automatically gets installed with the printer software and will be loaded by Windows after each system reboot.
This makes it the perfect target for attackers who need an easy way to escalate privileges, since the bug can be abused even when the printer is not connected to the targeted device.
Successful exploitation requires local user access which means that threat actors will need to first get a foothold on the targeted devices.
Once this is achieved, they can abuse the security bug to escalate privileges in low complexity attacks without requiring user interaction.
The result is that attackers with basic user privileges can elevate their privileges to SYSTEM and run code in kernel mode, potentially bypassing security products that would block their attacks or the delivery of additional malicious payloads.
“Successfully exploiting a driver vulnerability might allow attackers to potentially install programs, view, change, encrypt or delete data, or create new accounts with full user rights,” SentinelOne explains.
“While we haven’t seen any indicators that this vulnerability has been exploited in the wild up till now, with hundreds of millions of enterprises and users currently vulnerable, it is inevitable that attackers will seek out those that do not take the appropriate action.”
A list of affected printer models using the vulnerable driver can be found in HP’s security advisory and this Xerox security mini bulletin.
HP, Xerox, and Samsung enterprise and home customers are urged to apply the patches provided by the two vendors as soon as possible.
“Some Windows machines may already have this driver without even running a dedicated installation file, since this driver comes with Microsoft Windows via Windows Update,” the researchers added.
Earlier this year, SentinelOne researchers found a 12-year-old privilege escalation bug in Microsoft Defender Antivirus (formerly Windows Defender) that can let attackers gain admin rights on unpatched Windows systems.
Microsoft Defender Antivirus is the default anti-malware solution on more than 1 billion systems running Windows 10 per Microsoft’s stats.
Also Read: Vulnerability Assessment vs Penetration Testing: And Why You Need Both