KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A student’s attempt to pirate an expensive data visualization software led to a full-blown Ryuk ransomware attack at a European biomolecular research institute.
BleepingComputer has long warned against software cracks, not only because they are illegal but because they are a common source of malware infections.
Threat actors commonly create fake software crack download sites, YouTube videos, and torrents to distribute malware, as shown below.

In the past, we have seen crack sites distribute ransomware, such as STOP and the Exorcist ransomware, cryptocurrency miners, and information-stealing trojans.
Also Read: 4 Best Practices On How To Use SkillsFuture Credit
After the research institute suffered a Ryuk ransomware attack, Sophos’ Rapid Response team responded and neutralized the cyberattack.
This attack lost the institute a week’s worth of research data and a week-long network outage as servers were rebuilt from scratch and data restored from backups.
After performing forensics on the attack, Sophos determined that the initial point-of-entry for the threat actors was an RDP session using a student’s credentials.
The institute works with university students who assist in research and other tasks. As part of this cooperation, the institute provides the students with login credentials to log into their network remotely.
After gaining access to the student’s laptop and analyzing the browser history, they learned that the student had searched for an expensive data visualization software tool that they used at work and wanted to install on their home computer.
Instead of buying the license for a few hundred dollars, the student searched for a cracked version and downloaded it from a warez site.
However, instead of receiving the expected software, they were infected with an information-stealing trojan that logged keystrokes, stole the Windows clipboard history, and stole passwords, including the same credentials used by the Ryuk threat actors to log into the institute.
“It is unlikely that the operators behind the ‘pirated software’ malware are the same as the ones who launched the Ryuk attack,” said Peter Mackenzie, manager of Rapid Response at Sophos. “The underground market for previously compromised networks offering attackers easy initial access is thriving, so we believe that the malware operators sold their access on to another attacker. The RDP connection could have been the access brokers testing their access.”
Marketplaces devoted to the selling of remote access credentials have been flourishing over the last couple of years and have become a common source of accounts used by ransomware gangs to gain access to corporate networks.
Many of these stolen credentials are gathered using information-stealing trojans and then sold one by one on these marketplaces for as little as $3.
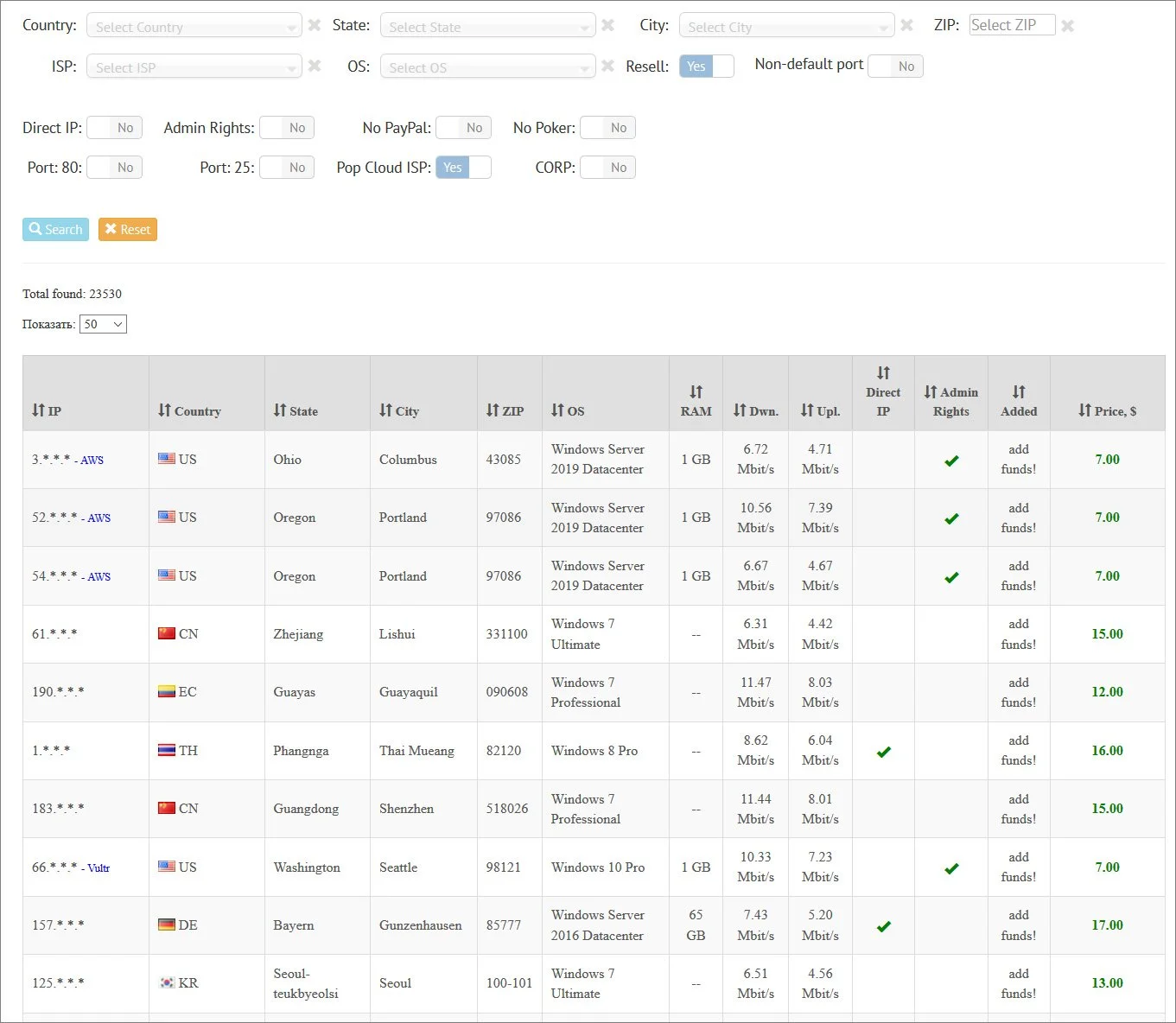
Just recently, BleepingComputer was provided access to the leaked data for UAS, one of the largest Windows Remote Desktop credentials marketplaces.
This data showed that over the past three years, 1.3 million accounts were put up for sale on the UAS marketplace, providing a massive pool of victims for threat actors to target.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
Unfortunately, there will always be the potential for human error. Users will continue to open phishing emails and download software cracks no matter how much we tell them not to.
However, properly configuring security on the network, such as requiring MFA for Remote Desktop connections and restricting access from specific locations or IP addresses, would have prevented this attack.