KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







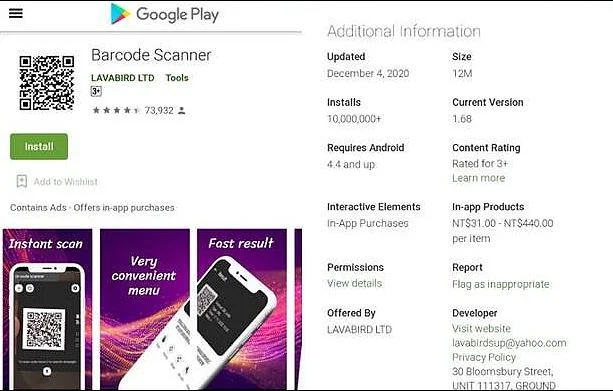
Google has removed a popular Android barcode scanner app with over 10 million installs from the Play Store after researchers found that it turned malicious following a December 2020 update.
After lying dormant for years, the previously legitimate Barcode Scanner app developed by LAVABIRD LTD self-updated and took over the users’ devices using malicious code now tagged by security vendors as trojan malware.
The malicious behavior experienced by its millions of users included seeing their default browser launching without any user interaction and displaying ads that promoted other, potentially malicious, Android apps.
“Many of the patrons had the app installed on their mobile devices for long periods of time (one user had it installed for several years),” Malwarebytes malware researcher Nathan Collier said.
“Then all of sudden, after an update in December, Barcode Scanner had gone from an innocent scanner to full on malware!”
Also Read: How to Send Mass Email Without Showing Addresses: 2 Great Workarounds
Even though this wouldn’t be the first time malicious code has been found in Android apps, such incidents usually involve the use of third-party software development kits (SDKs) used by free app versions to display ads for monetization.
However, in this case, the obfuscated and signed malicious code was bundled with the app and installed on the devices of more than 10 million users in one fell swoop.
“To verify this is from the same app developer, we confirmed it had been signed by the same digital certificate as previous clean versions,” Collier added.
“Because of its malign intent, we jumped past our original detection category of Adware straight to Trojan, with the detection of Android/Trojan.HiddenAds.AdQR.”
Google removed LAVABIRD’s Barcode Scanner app from the Play Store after receiving Malwarebytes’ disclosure in December.
Despite this, there might still be millions of other devices still affected and displaying unwanted ads to its unwitting userbase.
Also Read: How a Smart Contract Audit Works and Why it is Important
A LAVABIRD spokesperson was not immediately available for comment when contacted by BleepingComputer earlier today for comment.