KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Apache Software Foundation has released HTTP Web Server 2.4.51 after researchers discovered that a previous security update didn’t correctly fix an actively exploited vulnerability.
Apache HTTP Server is an open-source, cross-platform web server that powers approximately 25% of websites worldwide.
On Tuesday, Apache released Apache HTTP 2.4.50 to fix an actively exploited path traversal vulnerability in version 2.4.49 (tracked as CVE-2021-41773). This flaw allows threat actors to view the contents of files stored on a vulnerable server.
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
“A flaw was found in a change made to path normalization in Apache HTTP Server 2.4.49. An attacker could use a path traversal attack to map URLs to files outside the expected document root,” disclosed Apache in a security advisory.
“If files outside of the document root are not protected by “require all denied” these requests can succeed. Additionally this flaw could leak the source of interpreted files like CGI scripts.”
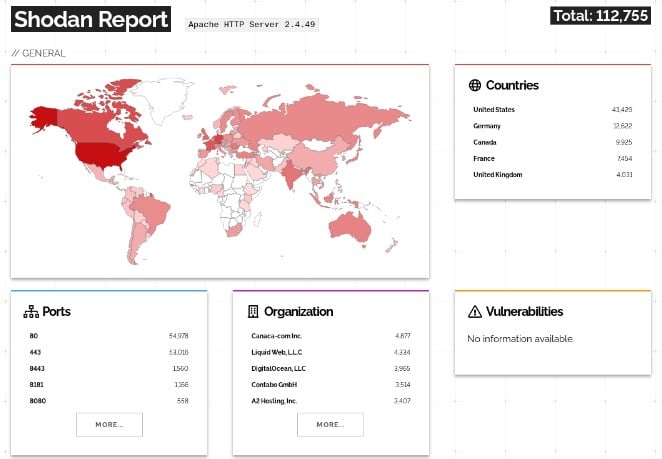
A Shodan search revealed over 112,000 Internet-exposed and vulnerable Apache HTTP servers providing the attackers with a wide selection of potential targets.
Soon after the update was released, security researchers analyzed and disclosed working exploits for the vulnerability. To make matters worse, researchers also discovered that the vulnerability could be used for remote code execution if the mod_cgi module was loaded and the default “Require all denied” option was missing.
With so many servers potentially vulnerable to remote code execution, it became even more critical for admins to update their Apache HTTP servers.
Today, Apache released version 2.4.51 after discovering that their previous fix for the actively exploited CVE-2021-41773 vulnerability was incomplete.
“It was found that the fix for CVE-2021-41773 in Apache HTTP Server 2.4.50 was insufficient. An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives,” announced Apache in an updated advisory.
“If files outside of these directories are not protected by the usual default configuration “require all denied”, these requests can succeed. If CGI scripts are also enabled for these aliased pathes, this could allow for remote code execution.”
This new path traversal vector is being tracked as CVE-2021-42013, and it was disclosed by Juan Escobar from Dreamlab Technologies, Fernando Muñoz from NULL Life CTF Team, and Shungo Kumasaka.
Also Read: What Does A Data Protection Officer Do? 5 Main Things
The United States Computer Emergency Readiness Team (US-CERT) says that this new vulnerability is also being exploited in ongoing attacks.
Active scanning of Apache HTTP Server CVE-2021-41773 & CVE-2021-42013 is ongoing and expected to accelerate, likely leading to exploitation. Please patch immediately if you haven’t already—this cannot wait until after the weekend. Read more: https://t.co/4Ljk730wz4 pic.twitter.com/TYPiXhOluf— US-CERT (@USCERT_gov) October 7, 2021
Now that it has been officially disclosed, it will not be long before other threat actors create their own working exploit.
Due to this, it is strongly recommended that admins immediately upgrade their servers to Apache HTTP 2.4.51 to remove any attack vectors left after the previous patch.