KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Canon has finally confirmed publicly that the cyberattack suffered in early August was caused by ransomware and that the hackers stole data from company servers.
BleepingComputer was the first to report the attack after tracking a suspicious outage on the cloud photo and video storage service (image.canon) that caused users to lose files.
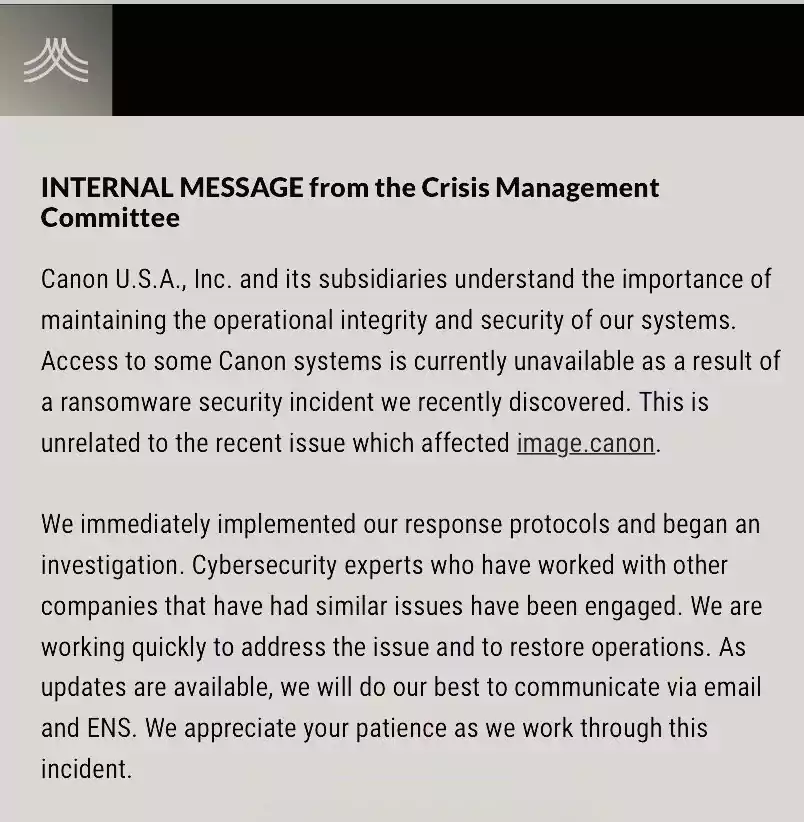
On August 5, Canon USA sent out a company-wide notification informing employees of extensive system issues that made multiple applications – Teams and email among them, unavailable.
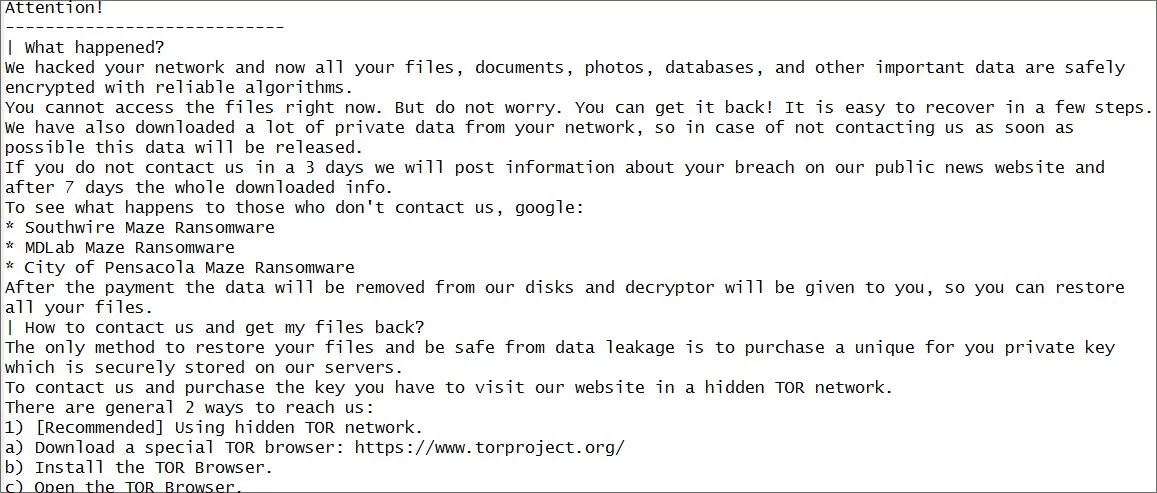
A partial screenshot of the ransom note obtained by BleepingComputer showed that the outage had been caused by Maze ransomware, a group that typically steals data from compromised networks to pressure victims into paying up.
Also Read: What Is A Governance Framework? The Importance And How It Works
Canon started to investigate the incident and found evidence of unauthorized activity on its network between July 20 and August 6.
The threat actor had accessed its file servers that also hosted “information about current and former employees from 2005 to 2020 and their beneficiaries and dependents.”
In a public announcement on Wednesday evening, Canon says that the data accessed by the attacker included employees’ names, Social Security number, date of birth, the number for the driver’s license number or government-issued ID, the bank account number for direct deposits from Canon, and their electronic signature.
Shortly after the attack, Maze ransomware told BleepingComputer that they had stolen from Canon 10 terabytes of data and private databases before detonating the file-encrypting malware on August 5.
Surprisingly, the image.canon issue and the general Canon USA outage caused by the attack were unrelated. Maze confirmed that their actions did not extend to the storage service.
While it took three months to confirm the ransomware attack publicly, Canon admitted the nature of the security incident to its employees in an internal security notice on August 6.
The Maze cybercriminal group was one of the big-league players in the ransomware business. On November 1, the gang shut down its operations that had started about a year and a half earlier, in May 2019.
Also Read: 5 Self-Assessment Tools To Find The Right Professional Fit
They are responsible for the current double-extortion trend embraced by most ransomware operators today where they steal data before encrypting it and threaten to leak the files unless the victim pays the ransom.
Among their victims are important companies Allied Universal, Southwire, City of Pensacola, Canon, LG Electronics, and Xerox.