KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The FBI said on Monday that Ranzy Locker ransomware operators had compromised at least 30 US companies this year from various industry sectors.
“Unknown cyber criminals using Ranzy Locker ransomware had compromised more than 30 US businesses as of July 2021,” the FBI said in a TLP: WHITE flash alert.
“The victims include the construction subsector of the critical manufacturing sector, the academia subsector of the government facilities sector, the information technology sector, and the transportation sector.’
The flash alert was issued in coordination with CISA and is designed to provide information to help security professionals detect and guard against such ransomware attack attempts.
Most Ranzy Locker victims who reported attacks told the FBI that the operators breached their networks by brute-forcing Remote Desktop Protocol (RDP) credentials.
More recently, others have reported that the attackers also exploited vulnerable Microsoft Exchange servers or used credentials stolen in phishing attacks.
Also Read: 3 Easy Ways for Hard Disk Recycling Protecting Businesses
Once inside a victim’s network, Ranzy Locker operators will also steal unencrypted documents before encrypting systems on their victims’ corporate networks, a tactic used by most other ransomware gangs.
These exfiltrated files, containing sensitive information, including customer info, personally identifiable information (PII) data, and financial records, are used as leverage to force the victims into paying a ransom to get their files back and not have the data leaked online.
When victims visit the group’s Tor payment site, they will see a ‘Locked by Ranzy Locker’ message and a live chat screen to negotiate with the threat actors.
As part of this “service,” the ransomware operators also allow their victims to decrypt three files for free to prove that the decryptor can restore their files.
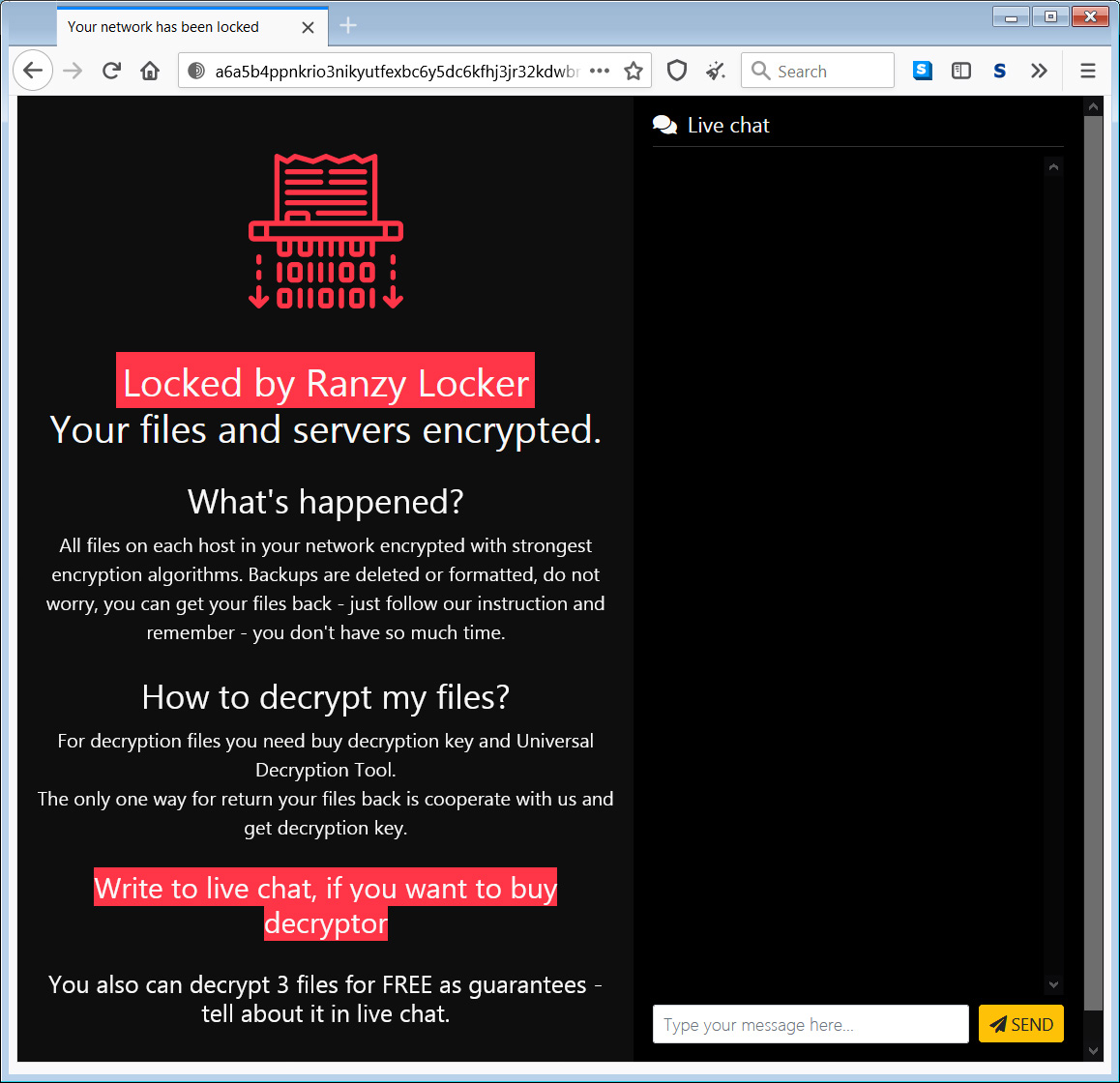
Victims who don’t pay the ransoms will have their stolen documents published on Ranzy Locker’s data leak site, dubbed Ranzy Leak.
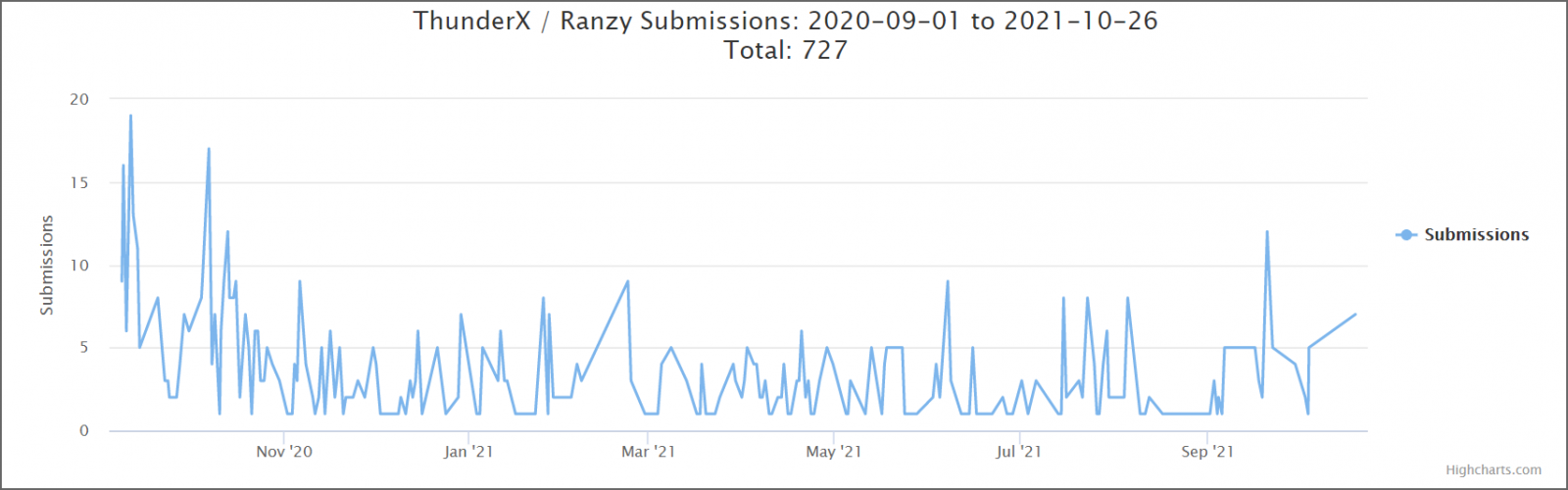
The domain used by their leak site was also used in the past by Ako Ransomware, a move part of the gang’s rebranding from Ako to ThunderX and then Ranzy Locker.
Also Read: How to Write an Effective Privacy Statement for Websites
ThunderX was a ransomware operation launched at the end of August 2020. Within a month from the launch, Tesorion found weaknesses in its encryption, which helped create a free decryptor.
Soon after, the cybercrime group fixed the bugs and released a new version of their ransomware strain under the Ranzy Locker name.
The FBI also provides technical details regarding tactics used in Ranzy Locker attacks, recommended mitigations, as well as indicators of compromise and YARA rules that can be used to detect and defend against such attempts.