KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A multi-platform Python-based malware targeting Windows and Linux devices has now been upgraded to worm its way into Internet-exposed VMware vCenter servers unpatched against a remote code execution vulnerability.
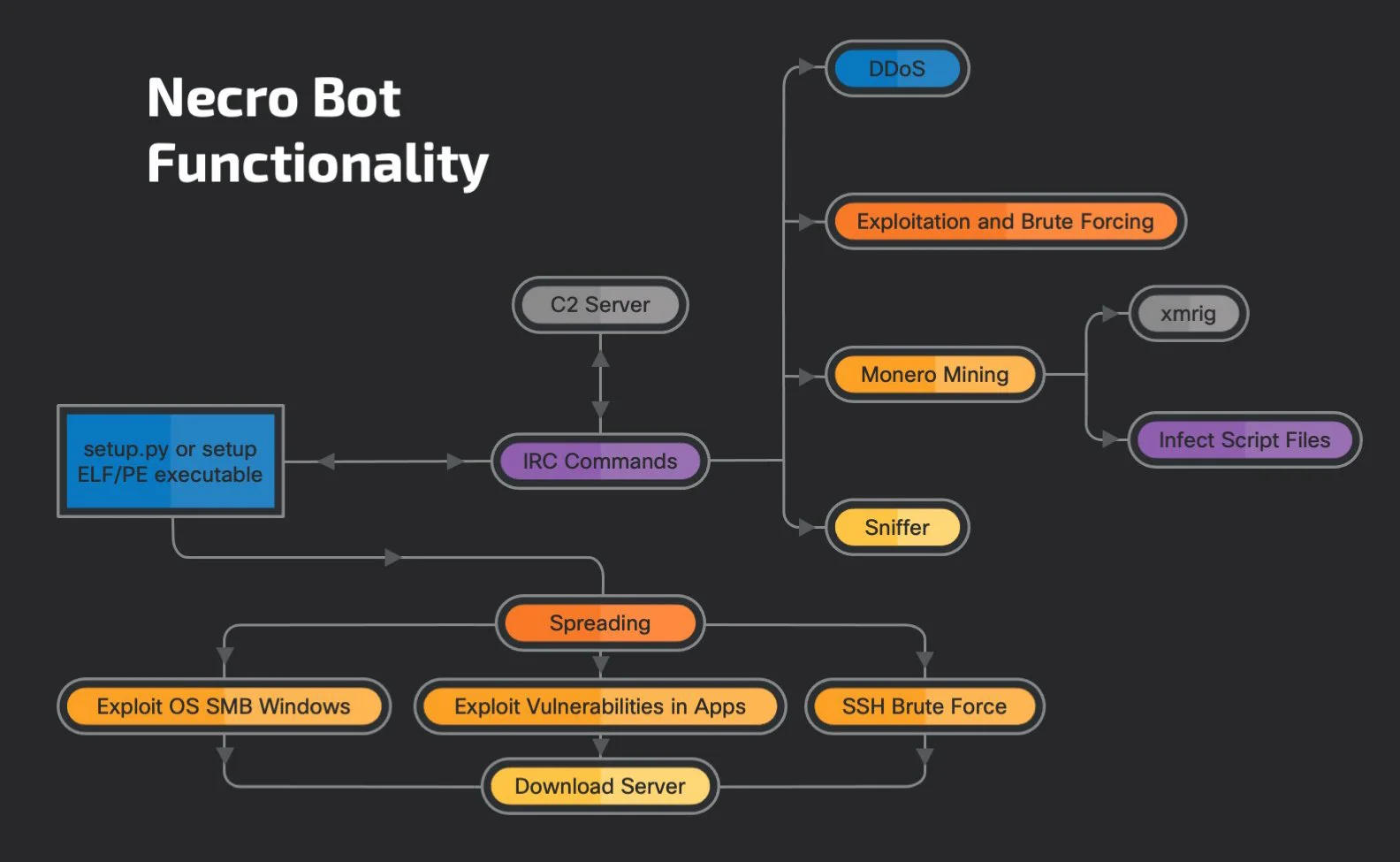
The malware, dubbed FreakOut by CheckPoint researchers in January (aka Necro and N3Cr0m0rPh), is an obfuscated Python script designed to evade detection using a polymorphic engine and a user-mode rootkit that hides malicious files dropped on compromised systems.
FreakOut spreads itself by exploiting a wide range of OS and apps vulnerabilities and brute-forcing passwords over SSH, adding the infected devices to an IRC botnet controlled by its masters.
The malware’s core functionality enables operators to launch DDoS attacks, backdoor infected systems, sniff and exfiltrate network traffic, and deploy XMRig miners to mine for Monero cryptocurrency.
Also Read: Compliance Course Singapore: Spotlight on the 3 Offerings
As Cisco Talos researchers shared in a report published today, FreakOut’s developers have been hard at work improving the malware’s spreading capabilities since early May, when the botnet’s activity has suddenly increased.
“Although the bot was originally discovered earlier this year, the latest activity shows numerous changes to the bot, ranging from different command and control (C2) communications and the addition of new exploits for spreading, most notably vulnerabilities in VMWare vSphere, SCO OpenServer, Vesta Control Panel and SMB-based exploits that were not present in the earlier iterations of the code,” Cisco Talos security researcher Vanja Svajcer said.
FreakOut bots scan for new systems to target either by randomly generating network ranges or on its masters’ commands sent over IRC via the command-and-control server.
For each IP address in the scan list, the bot will try to use one of the built-in exploits or log in using a hardcoded list of SSH credentials.
While early FreakOut versions were able to exploit only vulnerable versions of Lifearay, Laravel, WebLogic, TerraMaster, and Zend Framework (Laminas Project) web apps, the latest ones have more than double the number of built-in exploits.
Also Read: PDPA Singapore Guidelines: 16 Key Concepts For Your Business
Newly added exploits to malware variants observed by Cisco Talos in May include:
The VMware vCenter vulnerability (CVE-2021-21972) is present in the vCenter plugin for vRealize Operations (vROps) and is particularly interesting because it impacts all default vCenter Server installations.