KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Owners of Gigaset Android phones have been repeatedly infected with malware since the end of March after threat actors compromised the vendor’s update server in a supply-chain attack.
Gigaset is a German manufacturer of telecommunications devices, including a series of smartphones running the Android operating system.
Starting around March 27th, users suddenly found their Gigaset mobile devices repeatedly opening web browsers and displaying advertisements for mobile game sites.
When inspecting their phone’s running apps, users found an unknown application called ‘easenf ‘ running, that when deleted, would automatically be reinstalled.
According to the German tech site BornCity, the easenf app was installed by the device’s system update app. Other malicious apps found alongside it include ‘gem’, ‘smart’, and ‘xiaoan.’
“Three malware apps were installed on each of the two affected smartphones, which could fortunately be terminated and uninstalled without any problems, but which were then repeatedly reloaded by the update app running in the background as a system process, unless the update app was terminated manually after each restart: easenf or gem, and in both cases smart and xiaoan,” a reader told BornCity.
Gigaset users uploaded some of these malicious packages to VirusTotal [1, 2], where they are detected as adware or downloaders.
Since the attack began, Malwarebytes has been supporting Gigaset owners on their forums and is detecting the threat as ‘Android/PUP.Riskware.Autoins.Redstone.’
Based on their research, Malwarebytes states that the ‘Android/PUP.Riskware.Autoins.Redstone’ app will download further malware on devices that are detected as ‘Android/Trojan.Downloader.Agent.WAGD.’
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
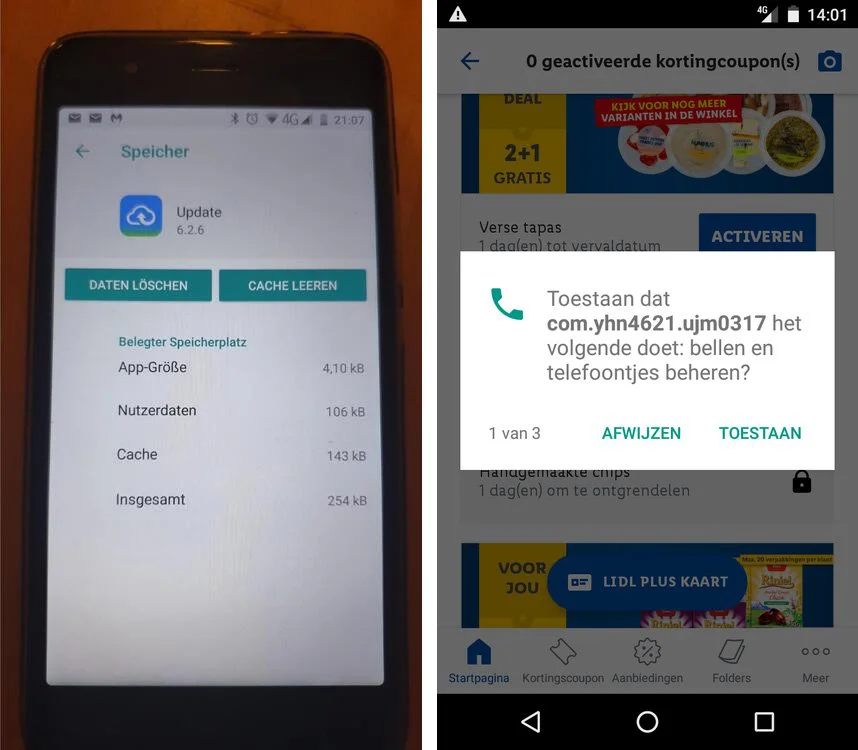
These secondary payloads all start with the name ‘com.wagd,’ and have been seen using the com.wagd.xiaoan, com.wagd.gem, com.wagd.smarter, and com.yhn4621.ujm0317 package names.

Malwarebytes states that these app will display advertisements, install other malicious apps, and attempt to spread via WhatsApp messages.
Malwarebytes found this supply-chain attack is affecting the following Gigaset Android devices:
To prevent the malicious packages from being reinstalled by Gigaset’s compromised update server, a user told Born that they had to forcibly disable the device’s update app using the developer options and adb with the following command:
adb shell pm disable-user –user 0 com.redstone.ota.uiIn a call with Gigaset, Günter Born of BornCity was told that one of the company’s update servers was compromised and used to push down malicious apps.
“An update server used by Gigaset devices for updating was compromised, so that the affected devices were infected by malware,” explains Born.
Gigaset’s SVP of Corporate Communication Raphael Dörr shared the following statement with BleepingComputer regarding the attack and how to remove the malware:
During routine control analyses we noticed that some older smartphones are having problems with malware. This finding was also confirmed by individual customers after enquiries were made. We immediately started investigating the incident intensely by working closely with IT forensic experts and the responsible authorities. In the meantime we were able to identify a solution to the problem.
Only older smartphone models of the GS100, GS160, GS170, GS180, GS270 (plus) and GS370 (plus) series are potentially affected.
Not affected by this incident are the smartphone models of the GS110, GS185, GS190, GS195, GS195LS, GS280, GS290, GX290, GX290plus, GX290 PRO, GS3 and GS4 series.
According to our latest information only some devices from the affected product lines were infected. Only devices on which the software updates provided by Gigaset in the past were not carried out by the user are affected. Malware was installed on these devices by a compromised server belonging to an external update service provider.
Gigaset took immediate action and contacted the update service provider. The update service provider also took immediate action and confirmed to Gigaset that the infection of smartphones could be stopped on 7 April.
Measures have been taken to automatically rid infected devices of the malware. In order for this to happen the devices must be connected to the internet (WLAN, WiFi or mobile data). We also recommend connecting the devices to their chargers. Affected devices should automatically be freed from the malware within 8 hours.
Also Read: 4 Considerations In The PDPA Singapore Checklist: The Specifics
Alternatively, users can check and clean their devices manually. Please proceed as follows:
Check if your device is affected
Uninstall the malware manually
We apologise for any inconvenience caused and will keep you informed of further developments.
Update 4/8/21: Added new statement.