KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






GitHub has revoked weak SSH authentication keys generated using a library that incorrectly created duplicate RSA keypairs.
GitHub allows you to authenticate to their service without a user name and password using the SSH protocol. To do this, users would generate an SSH keypair and add the public key to their accounts’ SSH key setting.
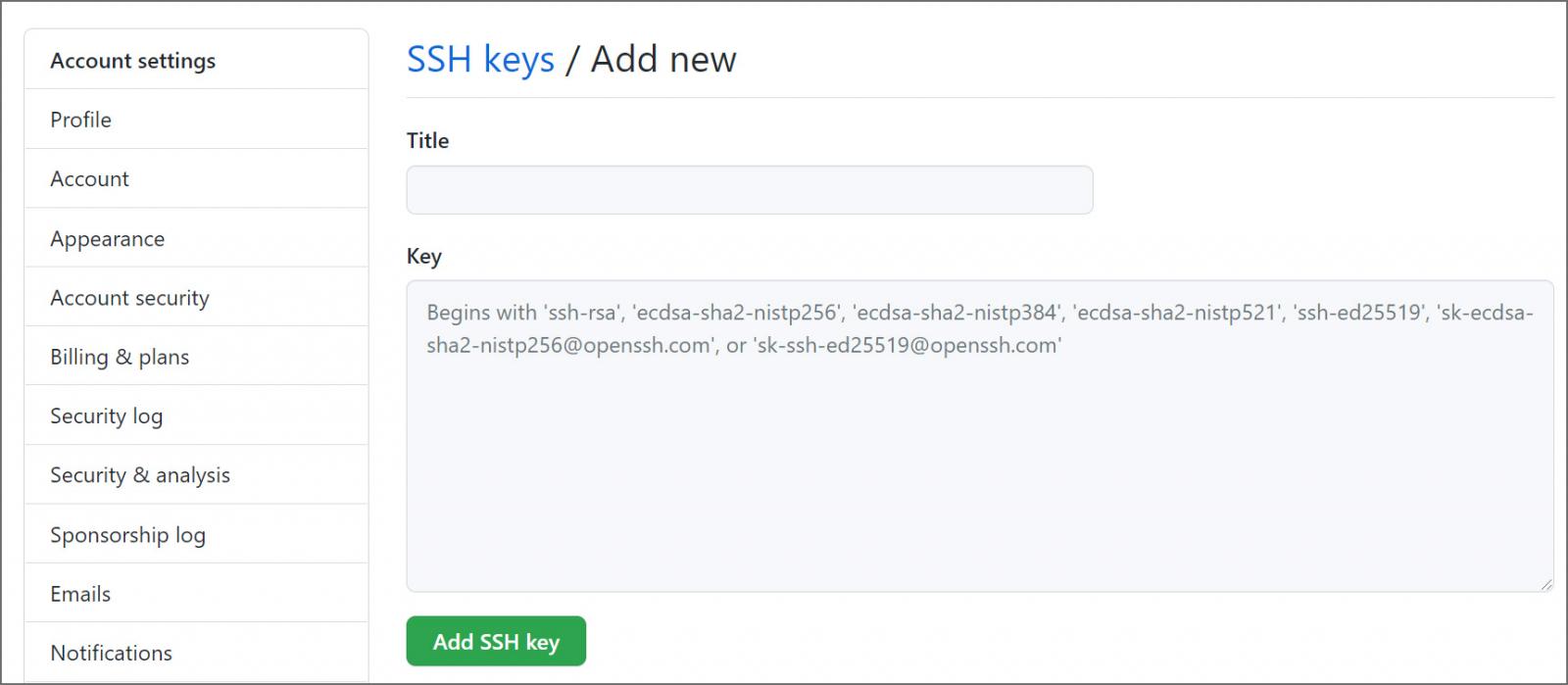
Once the key has been added to your account, you can use it with a Git client to automatically log in to GitHub without entering a user name and password.
Also Read: PDPA Compliance for HR Managers in Singapore: A Must
Today, in a coordinated disclosure between GitHub and Axosoft, LLC., the makers of the popular GitKraken Git client, GitHub said they revoked weak SSH keys generated by the ‘keypair‘ library used by the software.
“An underlying issue with a dependency, called keypair, resulted in the GitKraken client generating weak SSH keys. This issue affected versions 7.6.x, 7.7.x, and 8.0.0 of the GitKraken client, and you can read GitKraken’s disclosure on their blog,” disclosed GitHub today in a new security advisory.
Keypair is a JavaScript library that allows for the programmatic generation of SSH keys.
A bug in the library’s pseudo-random number generator allowed for the generation of duplicate RSA keys, enabling users to access other GitHub accounts secured with the same SSH key.
“A bug in the pseudo-random number generator used by keypair versions up to and including 1.0.3 could allow for weak RSA key generation. This could enable an attacker to decrypt confidential messages or gain authorized access to an account belonging to the victim. We recommend replacing any RSA keys that were generated using keypair version 1.0.3 or earlier,” explained the Keypair advisory.
The bug was discovered by Axosoft engineer Dan Suceava, “who noticed that keypair was regularly generating duplicate RSA keys.”
To protect their users, GitHub revoked all keys generated by GitKraken at 17:00 UTC or 1 PM EST.
GitHub also revoked other potentially weak keys that were created by other clients using the same keypair library.
Also Read: 5 Workplace Tips: Protecting Information on Mobile Devices
Users whose keys have been revoked are notified by GitHub and recommended to review their SSH keys and replace them if the vulnerable library generated them.
Axosoft recommends users of their software generate new SSH keys using GitKraken 8.0.1, or later, for each Git service provider.