KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The now-defunct WeLeakInfo data breach site has suffered its own data breach after a threat actor leaked the service’s payment information and customer info.
WeLeakInfo was a website that offered paid subscriptions for searchable access to a database containing 12.5 billion user records stolen during data breaches. This data included email addresses, names, phone numbers, addresses, and in many cases, passwords.
Threat actors commonly used the site to conduct phishing campaigns, credential stuffing attacks, and potentially gain access to corporate networks.
In January 2020, an international law enforcement operation including the FBI, UK NCA, the Netherlands National Police Corps, the German Bundeskriminalamt, and the Police Service of Northern Ireland, allowed the FBI to seize the WeLeakInfo domain – effectively shutting down the site’s operation.

Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
Last Thursday, a threat actor released an archive of payment processing data used by WeLeakInfo when processing payments through Stripe.
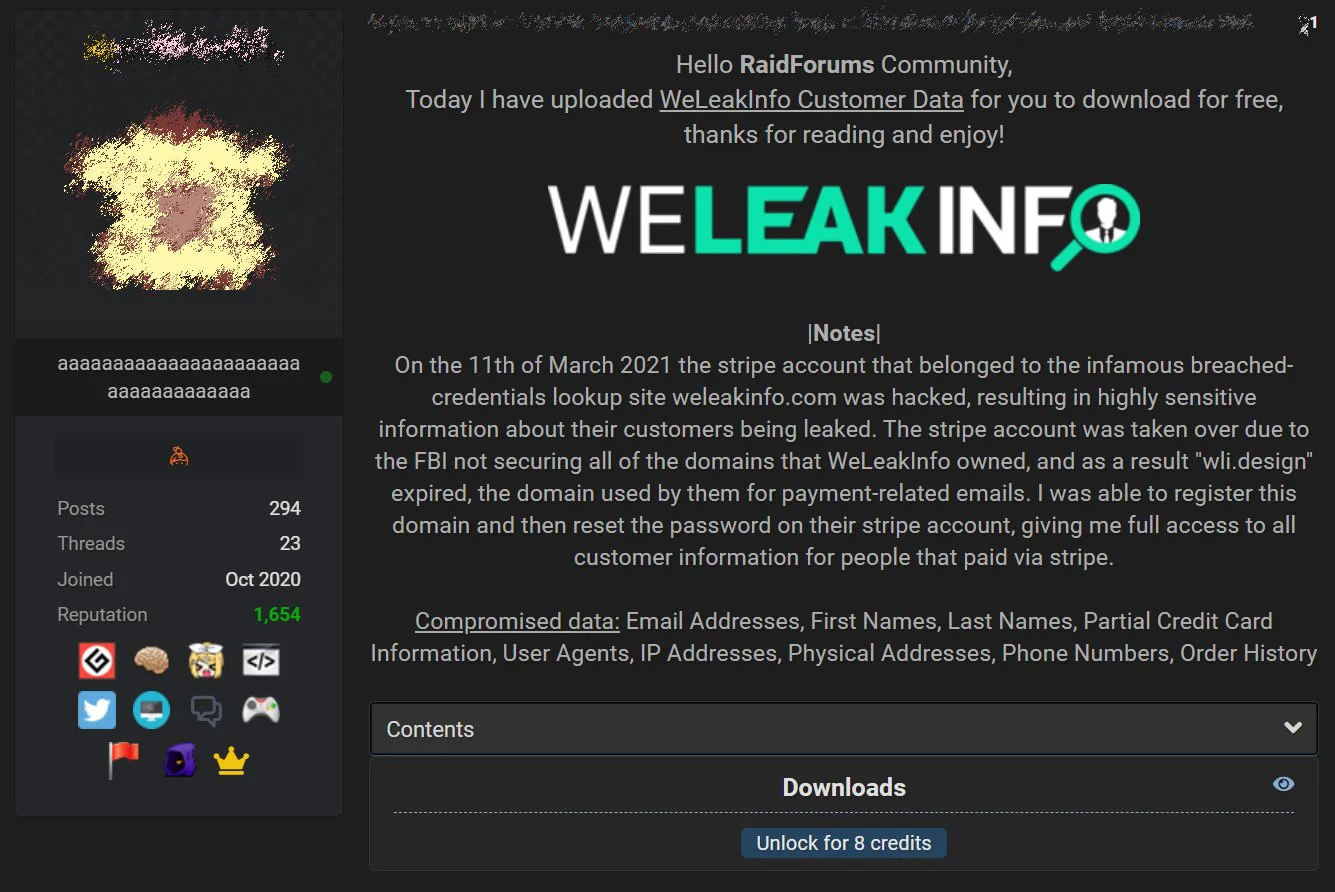
The data was published on a popular hacking forum known as RaidForums, where other threat actors could download WeLeakInfo data by paying eight credits, a form of currency used on the forum, which is equal to about $2.54.
One of the hacking forum administrators posted that they found their data listed in the dump from when they used the service.
The poster states they gained access to the WeLeakInfo payment processing data after the FBI allowed the ‘wli.design’ domain to expire. WeLeakInfo allegedly used this domain for payment-related emails from Stripe.
“The stripe account was taken over due to the FBI not securing all of the domains that WeLeakInfo owned, and as a result “wli.design” expired, the domain used by them for payment-related emails.”
“I was able to register this domain and then reset the password on their stripe account, giving me full access to all customer information for people that paid via stripe,” the threat actor explained in a post leaking the WeLeakInfo data.
Last weekend, cybersecurity intelligence firm Cyble shared samples of the stolen data with BleepingComputer and said there are approximately 10,000 unique customers listed in the data leak.
The leaked data includes screenshots from the Stripe WeLeakInfo account and spreadsheets containing invoices, successful payments, customer lists, and more.
The spreadsheets contain personal and corporate data, such as email addresses, names, billing addresses, last four digits and expiration dates of credit cards, IP addresses, order history, IP addresses, and phone numbers.
The screenshots in the data leak also indicate that WeLeakInfo had close to 24,000 payments and a NET sales amount of £92,000 since January 1st, 2019.
In addition to non-corporate users, the leaked data also included businesses that used the service.
Also Read: 4 Considerations In The PDPA Singapore Checklist: The Specifics
Most of these businesses are security companies that were likely using the data as part of proactive warning services for their customers to warn of exposed credentials and information.