KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







In what appears to be an attack from the Hive ransomware gang, computers of the non-profit Memorial Health System have been encrypted, forcing staff to work with paper charts.
The attack occurred early Sunday morning and the IT department detected it once they noticed that parts of the infrastructure no longer responded as expected.
Memorial Health System is a small network of three hospitals (Marietta Memorial Hospital, Selby General Hospital, and Sistersville General Hospital) in Ohio and West Virginia, outpatient service sites, and provider clinics.
A non-profit integrated health system, the organization counts more than 3,000 employees and is lead by a volunteer board of community members.
The attack caused disruptions of clinical and financial operations, causing urgent surgical cases and radiology exams on Monday to be canceled.
On Sunday, after learning more about the attack, the organization issued a press release to notify the community of the incident.
Memorial Health System president and CEO Scott Cantley said at the time that patient or employee data had not been compromised and that the investigation was ongoing, to get the complete picture of what happened.
Also Read: Data Protection Policy: 8 GDPR Compliance Tips
Typically, ransomware attacks come with a data breach. Before deploying the encryption routine, hackers typically spend time on the network to determine the most valuable systems and to steal data.
By exfiltrating information, the attackers have more leverage to force the victim to pay the ransom in exchange for the promise to not share or leak the stolen data and to provide a decryption tool.
This case appears to be no different. BleepingComputer has seen evidence that the attackers have stolen databases with information belonging to 200,000 patients, which includes sensitive details, such as social security numbers, names, and dates of birth.
The perpetrator is allegedly the Hive ransomware gang, which emerged in late June, discovered by dnwls0719. Despite the short time of activity, the group already claimed multiple victims.
Like most ransomware gangs, Hive has a leak site called HiveLeaks and hosted on the dark web, where they published links to data stolen from almost two dozen victims that did not pay the ransom.
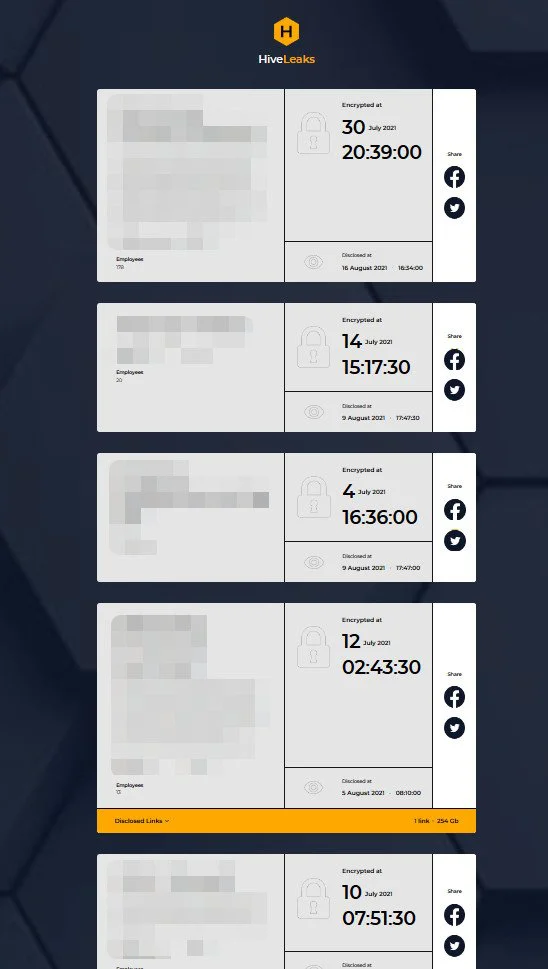
Most of the businesses listed on the leak site appear to be small to medium sized, many having around or less than 100 employees.
Also Read: Don’t Be Baited! 5 Signs of Phishing in Email
The largest of the non-paying victims is Altus Group – a provider of software and data solutions for the commercial real estate industry. According to the attacker, the company has 2,500 employees and a revenue of $500 million.