KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







JBS, the world’s largest beef producer, has confirmed that they paid an $11 million ransom after the REvil ransomware operation initially demanded $22.5 million.
On May 31, JBS was forced to shut down some of its food production sites after the REvil ransomware operators breached their network and encrypted some of its North American and Australian IT systems.
JBS said they paid $11 million to prevent their stolen data from being publicly leaked and mitigate possible technical issues in a statement released last night.
“This was a very difficult decision to make for our company and for me personally,” said Andre Nogueira, CEO, JBS USA. “However, we felt this decision had to be made to prevent any potential risk for our customers.”
On June 1st, a negotiation chat claiming to be between JBS and the REvil ransomware operation was shared with BleepingComputer.
At the start of negotiations, the ransom demand was initially $22.5 million, with the REvil ransomware negotiator warning that data would be leaked if they were not paid.
Also Read: This Educator Aims to Make Good Cyber Hygiene a Household Practice
“We want to inform that your company local network have been hacked and encrypted. We have all your local network data. The Price to unlock is $22,500,000,” REvil told the JBS representative.
“Now we’re keeping it a secret, but if you do not reply us within 3 days it will be posted on our news-site. Think about the financial damage to your stock price from this publication.”
Before negotiating further, the JBS representative asked to be shown the data stolen during the attack.
It appears REvil knew the worldwide attention JBS’ attack was receiving as they refused to show any of the stolen data until a payment was made.
“After analyzing the available information, my boss came to the conclusion that the transfer of files will take place only after payment,” REvil told JBS in the negotiation chat.
JBS explained that they only needed the ransomware decryptor to decrypt two specific databases as the rest of the data was being restored from backups.
After a series of offers and counter-offers, JBS and REvil agreed to a ransom of $11 million, and payment in bitcoins was sent that same day, June 1st.
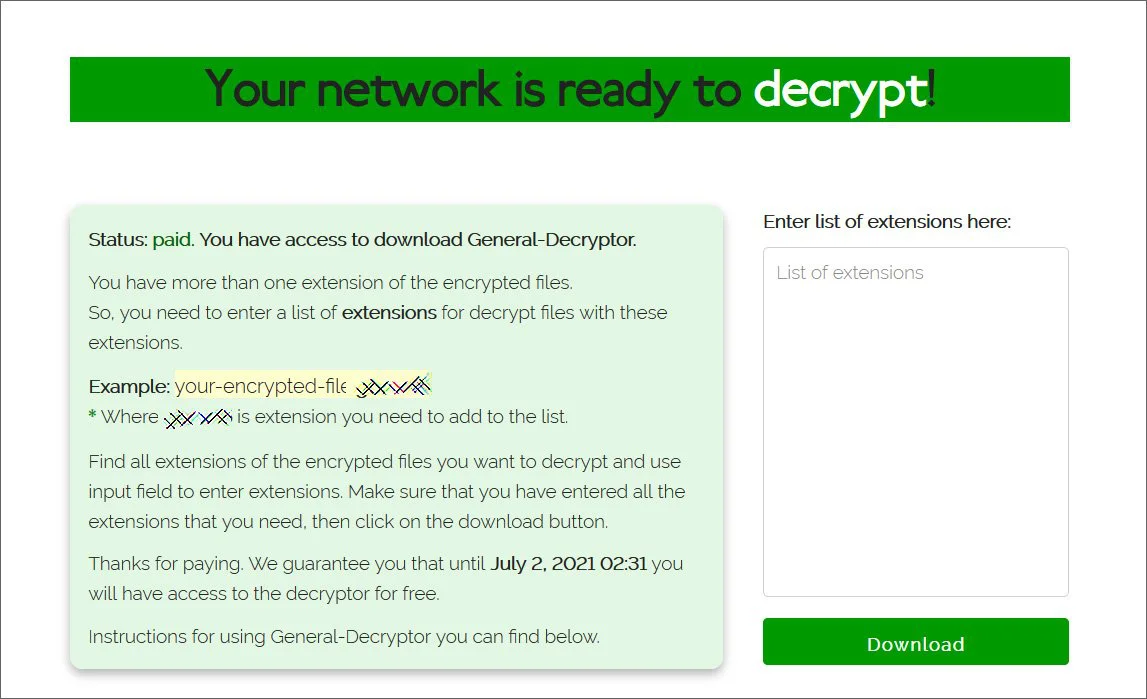
After the ransomware gang received the payment, they provided the decryptor, shown below.
BleepingComputer was also shown that the ransom was paid in bitcoin before the threat actors provided proof of stolen data in the negotiation chat.
When we contacted JBS that night to confirm if they were paying the ransomware, we were told that the chat went silent, and no further discussions took place other than the request of a universal decryptor.
REvil offers ransomware negotiation firms a private backchannel to talk with the ransomware operation. BleepingComputer believes that the JBS negotiators began using that once we reached out about the ransom payment.
While BleepingComputer was assured that this was the JBS negotiation, we did not report on it as we could not independently verify the victim at the time.
JBS is not alone in paying a significant ransom demand to bring a critical infrastructure operation back online.
Also Read: The 5 Phases of Penetration Testing You Should Know
Last month, Colonial Pipeline confirmed they paid a $5 million ransom to DarkSide to quickly get the fuel pipeline operational.
Unfortunately, paying these ransoms will only show ransomware gangs that critical infrastructure is a target that pays, and we may see more targeted attacks in the future.