KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A recently discovered multi-platform credit card skimmer can harvest payment info on compromised stores powered by Shopify, BigCommerce, Zencart, and Woocommerce.
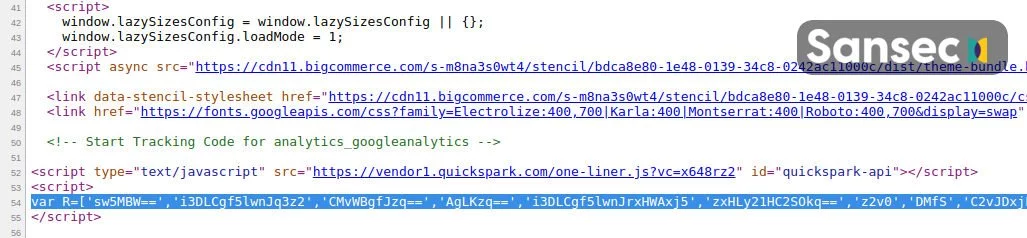
While usually designed to target a single type of e-commerce platform, this new type of web skimming malware can take over the checkout process on shops using multiple online store management systems by injecting a malicious checkout page.
This new skimmer (also known as a Magecart script) can also abuse hosted e-commerce systems such as Shopify and BigCommerce, as researchers at Dutch cyber-security company Sansec found, even though they do not provide support for custom checkout pages scripts.
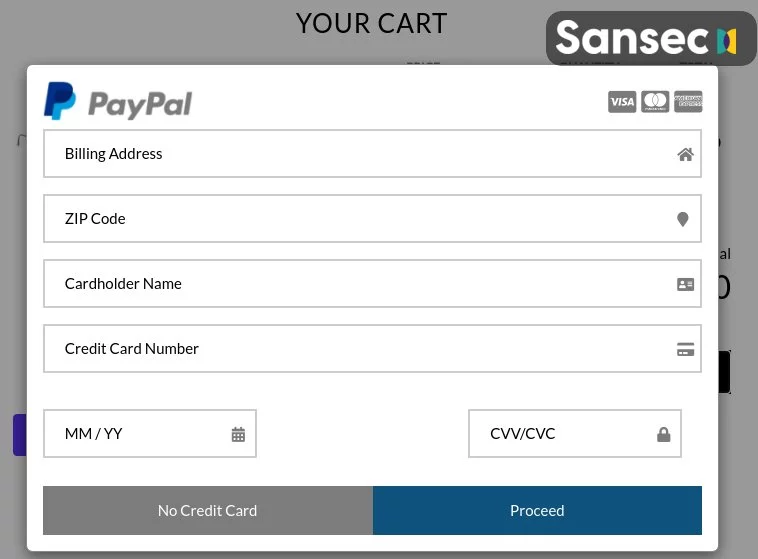
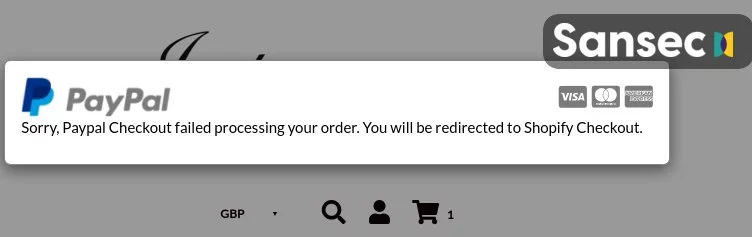
It does that by displaying a fake payment page before the customers land on the real checkout form and using a keylogger to intercept payment and personal information.
The skimmer will also throw an error after the customers hit the “Proceed” button to submit their credit card information to evade detection and not raise any alarm flags., redirecting them back to the legitimate checkout process and payment form.
Also Read: A Look at the Risk Assessment Form Singapore Government Requires
“It is remarkable that so many different platforms are compromised in the same campaign,” Sansec said.
“Typically, criminals exploit a flaw in a single platform. Attackers may have breached a shared component, eg software or a service that is used by all affected merchants.”
Another interesting technique used by this skimmer is the way it exfiltrates data to automatically generated domains based on a counter and encoded using base64 encoding (examples of such domains are zg9tywlubmftzw5ldza[.]com, zg9tywlubmftzw5ldze[.]com, and so on).
This also offers a hint on how long this Magecart campaign has been running for, given that the first such programmatically generated exfiltration domain was first registered on August 31st, 2020.
“To summarize: this campaign shows that platforms are no boundary to the profitable fraud of online skimming,” Sansec added. “Wherever customers enter their payment details, they are at risk.”
During the last few months, Sansec researchers have discovered several Magecart campaigns using innovative tactics for evading detection and gaining persistence on hacked stores.
For instance, they found a credit card stealer script hidden in plain sight using CSS code to avoid getting discovered, a web skimming malware able to camouflage as SVG social media buttons, and an almost impossible to get rid of credit card stealer bundling a persistent backdoor.
They also spotted a stealthy remote access trojan (RAT) malware used by Magecart threat actors to maintain persistence and regain access to the servers of hacked online stores.
Also Read: How to Send Mass Email Without Showing Addresses: 2 Great Workarounds
However, the malware dropper used to load the RAT on infected online shops also inadvertently spilled the beans on a list of dozens of compromised stores.