KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A new ransomware gang known as ‘N3TW0RM’ is targeting Israeli companies in a wave of cyberattacks starting last week.
Israeli media Haaretz reported that at least four Israeli companies and one nonprofit organization had been successfully breached in this wave of attacks.
Like other ransomware gangs, N3TW0RM has created a data leak site where they threaten to leak stolen files as a way to scare their victims into paying a ransom.
Two of the Israeli businesses, H&M Israel and Veritas Logistic’s networks, have already been listed on the ransomware gang’s data leak, with the threat actors already leaking data allegedly stolen during the attack on Veritas.
From the ransom notes seen by Israeli media and BleepingComputer, the ransomware gang has not been asking for particularly large ransom demands compared to other enterprise-targeting attacks.
Haaretz reports that Veritas’ ransom demand was three bitcoin, or approximately $173,000, while another ransom note shared with BleepingComputer shows a ransom demand of 4 bitcoins, or roughly $231,000.

Also Read: 4 Best Practices On How To Use SkillsFuture Credit
A WhatsApp message shared among Israeli cybesrecurity researchers also states that the N3TW0RM ransomware shares some characteristics with the Pay2Key attacks conducted in November 2020 and February 2021.
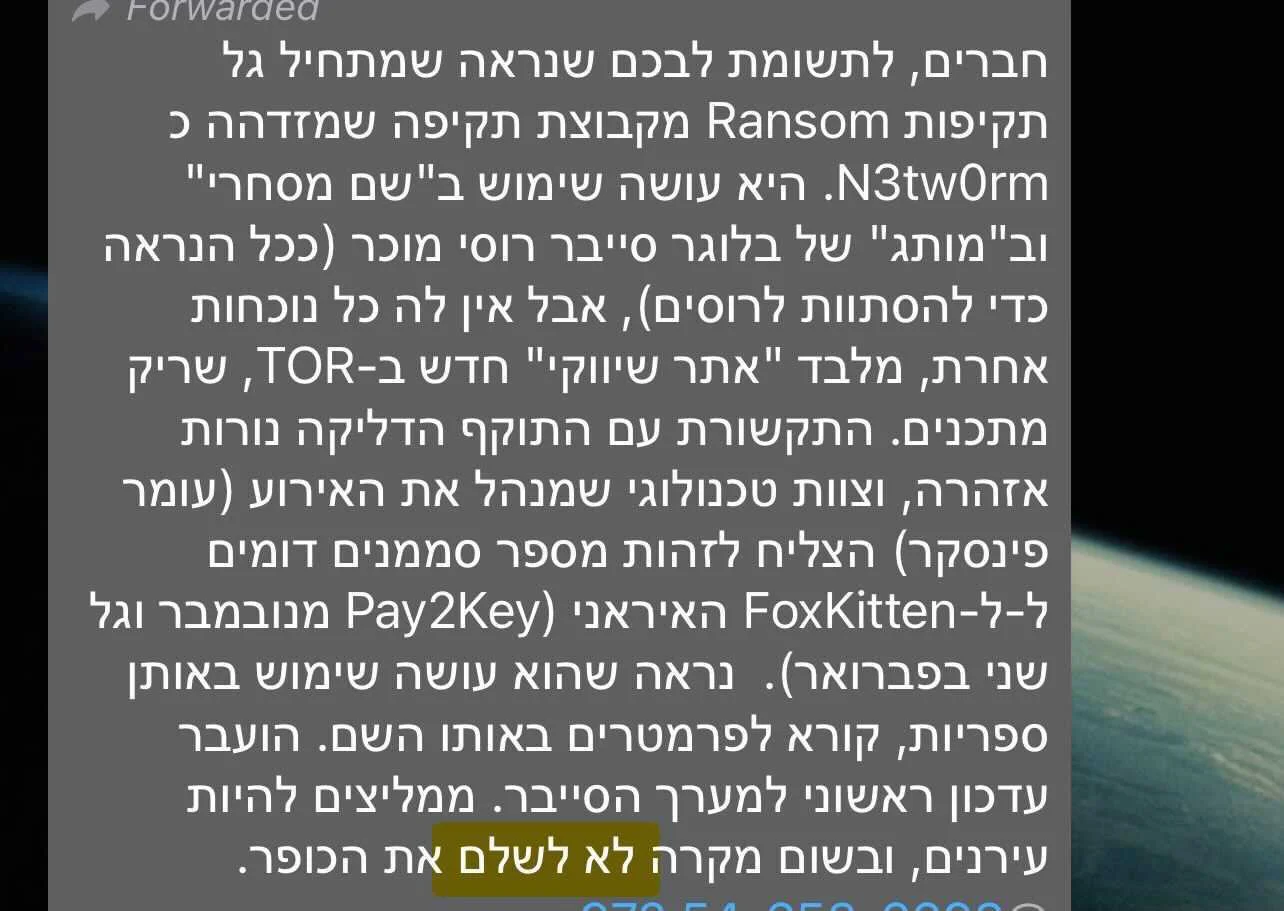
Pay2Key has been linked to an Iranian nation-state hacking group known as Fox Kitten, whose goal was to cause disruption and damage to Israeli interests rather than generate a ransom payment.
The N3TW0RM attacks have not been attributed to any hacking groups at this time.
Due to the low ransom demands and lack of response to negotiations, one source in the Israeli cybersecurity industry has told BleepingComputer that they believe N3TW0RM is also being used for sowing chaos for Israeli interests.
However, Arik Nachmias, CEO of incident response firm Honey Badger Security, told BleepingComputer that he believes that in N3TW0RM’s case, the attacks are motivated by money.
When encrypting a network, threat actors will usually distribute a standalone ransomware executable to every device they wish to encrypt.
N3TW0RM does it a bit differently by using a client-server model instead.
From samples [VirusTotal] of the ransomware seen by BleepingComputer and discussions with Nachmias, the N3TW0RM threat actors install a program on a victim’s server that will listen for connections from the workstations.
Nachmias states that the threat actors then use PAExec to deploy and execute the ‘slave.exe’ client executable on every device that the ransomware will encrypt. When encrypting files, the files will have the ‘.n3tw0rm‘ extension appended to their names.
While BleepingComputer does not have access to the server executable, we set up NetCat to listen and wait for connections on port 80. We then launched the slave.exe client, so it connects back to our IP address on that port.
As you can see below, when the client connects back to port 80 on our device running NetCat, it will send an RSA key to the server.
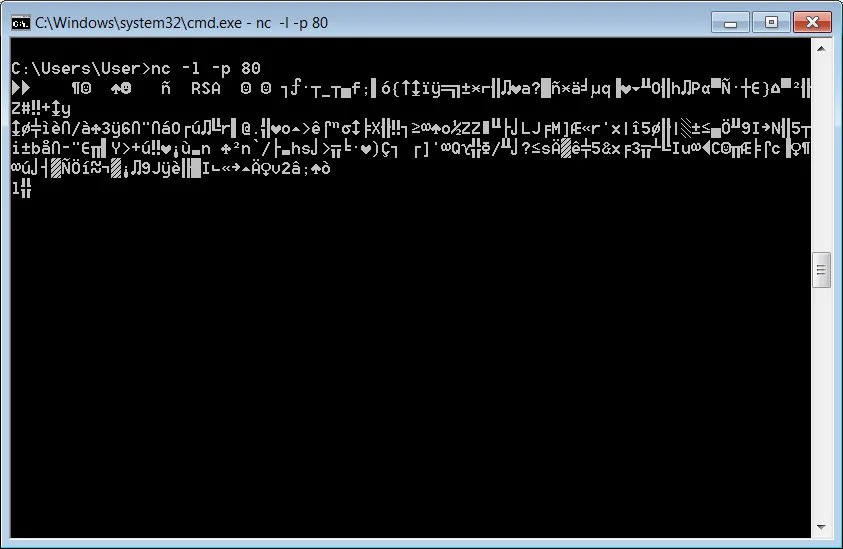
Nachmias told BleepingComputer that the server component would save these keys in a file and then direct the clients to begin encrypting devices.
This approach allows the threat actor to keep all aspects of the ransomware operation within the victim’s network without being traced back to a remote command & control server.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
However, it also adds complexity to the attack and could allow a victim to recover their decryption keys if all of the files are not removed after an attack.