KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







BlackTech cyber-espionage APT (advanced persistent threat) group has been spotted targeting Japanese companies using novel malware that researchers call ‘Flagpro’.
The threat actor uses Flagpro in the initial stage of an attack for network reconnaissance, to evaluate the target’s environment, and to download second-stage malware and execute it.
The infection chain begins with a phishing email crafted for the target organization, pretending to be a message from a trustworthy partner.
Also Read: The 3 Main Benefits Of PDPA For Your Business
The email carries a password-protected ZIP or RAR attachment that contains a Microsoft Excel file (.XLSM) laced with a malicious macro. Running this code creates an executable in the startup directory, the Flagpro.
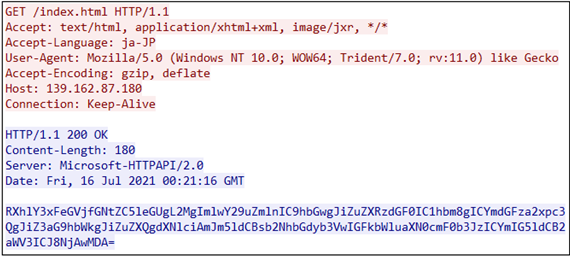
On its first execution, Flagpro connects to the C2 server via HTTP and sends system ID details obtained by running hardcoded OS commands.
In response, the C2 can send back additional commands or a second-stage payload that Flagpro can execute.
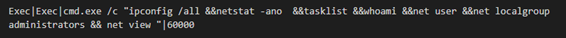
The communication between the two is encoded with Base64, and there’s also a configurable time delay between connections to avoid creating a pattern of identifiable operations.
According to a report by NTT Security, Flagpro has been deployed against Japanese firms for more than a year, since at least October 2020. The most recent sample the researchers could retrieve is from July 2021.
The targeted entities are from various sectors, including defense technologies, media, and communications.
Also Read: What Do 4 Messaging Apps Get From You? Read The iOS Privacy App Labels
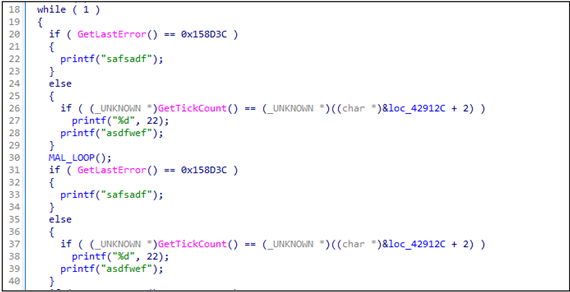
At some point in their analysis, NTT researchers noticed a new version of Flagpro, which can automatically close dialogs relevant to establishing external connections that could reveal its presence to the victim.
“In the implementation of Flagpro v1.0, if a dialog titled “Windows セキュリティ” is displayed when Flagpro accesses to an external site, Flagpro automatically clicks OK button to close the dialog,” explains the NTT Security report.
“This handling also works when the dialog is written in Chinese or English. It indicates the targets are in Japan, Taiwan, and English-speaking countries.”
BlackTech APT is a lesser-known actor that TrendMicro researchers first spotted in the summer of 2017 and is associated with China.
Its typical targets are in Taiwan, although it occasionally attacked companies in Japan and Hong Kong to steal technology.
In February 2021, a Unit 42 report connected BlackTech to WaterBear; another cyber-espionage group believed to be backed by the Chinese government.
As an APT, BlackTech possesses the knowledge and sophistication to adjust its tools to new reports like this one, so Flagpro will likely now be modified for stealthier deployment.
As the NTT report concludes: “Recently, they (BlackTech) have started using other new malware called “SelfMake Loader” and “Spider RAT”. It means that they are actively developing new malware.”
Defenders need to take note of the new indicators of compromise related to the new malware and follow all best security practices to maintain strong defenses against sophisticated threats like BlackTech.