KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







University researchers in the US have developed a new fingerprint capturing and browser spoofing attack called Gummy Browsers. They warn how easy the attack is to carry out and the severe implications it can have.
A digital fingerprint is a unique online identifier associated with a particular user based on a combination of a device’s characteristics. These characteristics could include a user’s IP address, browser and OS version, installed applications, active add-ons, cookies, and even how the user moves their mouse or types on the keyboard.
Websites and advertisers can use these fingerprints to confirm a visitor is a human, track a user between sites, or for targeted advertising. Fingerprints are also used as part of some authentication systems, allowing MFA or other security features to be potentially bypassed if a valid fingerprint is detected.
Digital fingerprints are so valuable that they are sold on dark web marketplaces, allowing threat actors and scammers to spoof users’ online fingerprints to take over accounts more easily or conduct ad fraud.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
The ‘Gummy Browsers’ attack is the process of capturing a person’s fingerprint by making them visit an attacker-controlled website and then using that fingerprint on a target platform to spoof that person’s identity.
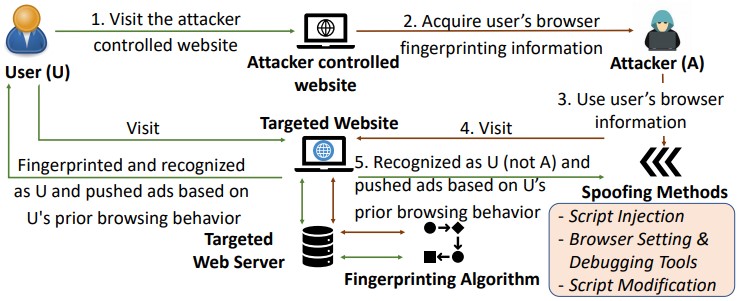
After generating a fingerprint of a user using existing or custom scripts, the researchers developed the following method to spoof the user on other sites:
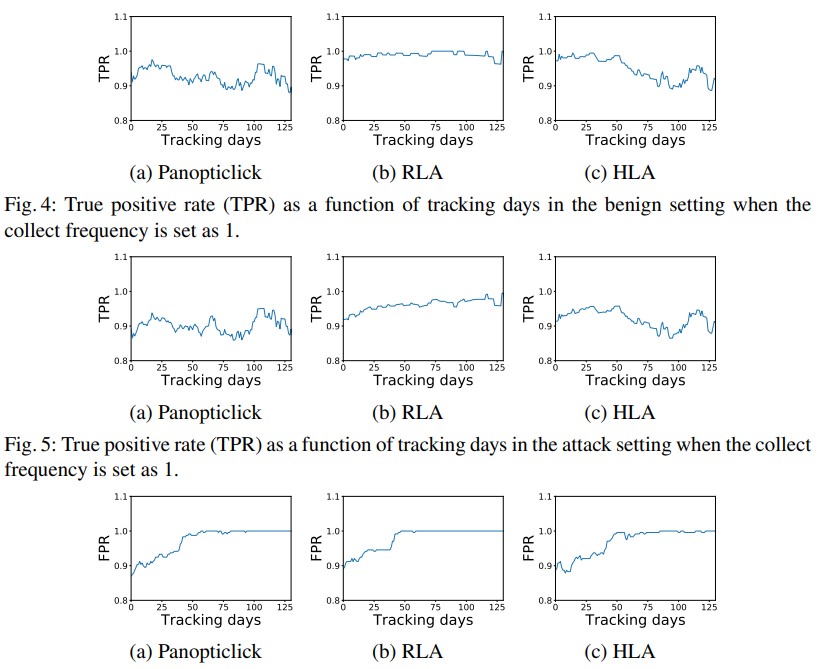
By capturing the victim’s fingerprint only once, the researchers said they could trick state-of-the-art fingerprinting systems such as FPStalker and Panopliclick for extensive periods.
“Our results showed that Gummy Browsers can successfully impersonate the victim’s browser transparently almost all the time without affecting the tracking of legitimate users,” the researchers explain in an Arxiv paper published yesterday.
Also Read: 4 Considerations In The PDPA Singapore Checklist: The Specifics
“Since acquiring and spoofing the browser characteristics is oblivious to both the user and the remote web-server, Gummy Browsers can be launched easily while remaining hard to detect”
Their tests returned a true positive rate of 0.9 and raised no alarms to alert the spoofed user that their online ‘identity’ was stolen.
The researchers state that threat actors can easily use the Gummy Browsers attack to trick systems utilizing fingerprinting.
“The impact of Gummy Browsers can be devastating and lasting on the online security and privacy of the users, especially given that browser-fingerprinting is starting to get widely adopted in the real world,” warned the researchers.
“In light of this attack, our work raises the question of whether browser fingerprinting is safe to deploy on a large scale.”
The attack can spoof a user’s identity to make a script appear as a human rather than a bot and be served targeted ads to perform ad fraud.
The Gummy Browsers attack may also help bypass security features used to detect legitimate users in authentication services. Examples of authentication systems that use fingerprinting include Oracle, Inauth, and SecureAuth IdP.
For example, SecureAuth ADP can be configured not to perform multi-factor authentication if a legitimate fingerprint is found.
“When a User logs into a realm, it is possible to use Device Recognition to prevent them having to MFA every time they access the realm,” explains an SecureAuth IDP support article.
Finally, many banks and retail sites use fingerprinting as part of their fraud detection mechanisms, which can be bypassed by spoofing a legitimate user’s identity.
Update 10/20/21: Added further context regarding how threat actors can use Gummy Browsers to bypass 2FA on auth systems. Also fixed two occurances of us calling it a Gummy Bear attack.