KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new ransomware known as Sarbloh encrypts your files while at the same time delivering a message supporting the protests of Indian farmers.
Last year the Indian government passed a new set of laws called the ‘Indian agriculture acts of 2020’, also known as the Farm Bills, which the government says is necessary to modernize its agricultural industry.
Farmers believe that these new laws will hurt their livelihoods and make it more challenging to generate revenue as the new laws removed restrictions on how farmers can sell goods and for how much.
Since November 2020, thousands of Indian farmers have been protesting these bills outside of New Delhi.
As detailed by numerous security firms, including Malwarebytes, Cyble, and QuickHeal, a new ransomware known as ‘Sarbloh’ is being distributed through malicious Word documents that contain a political message in support of Indian farmers.
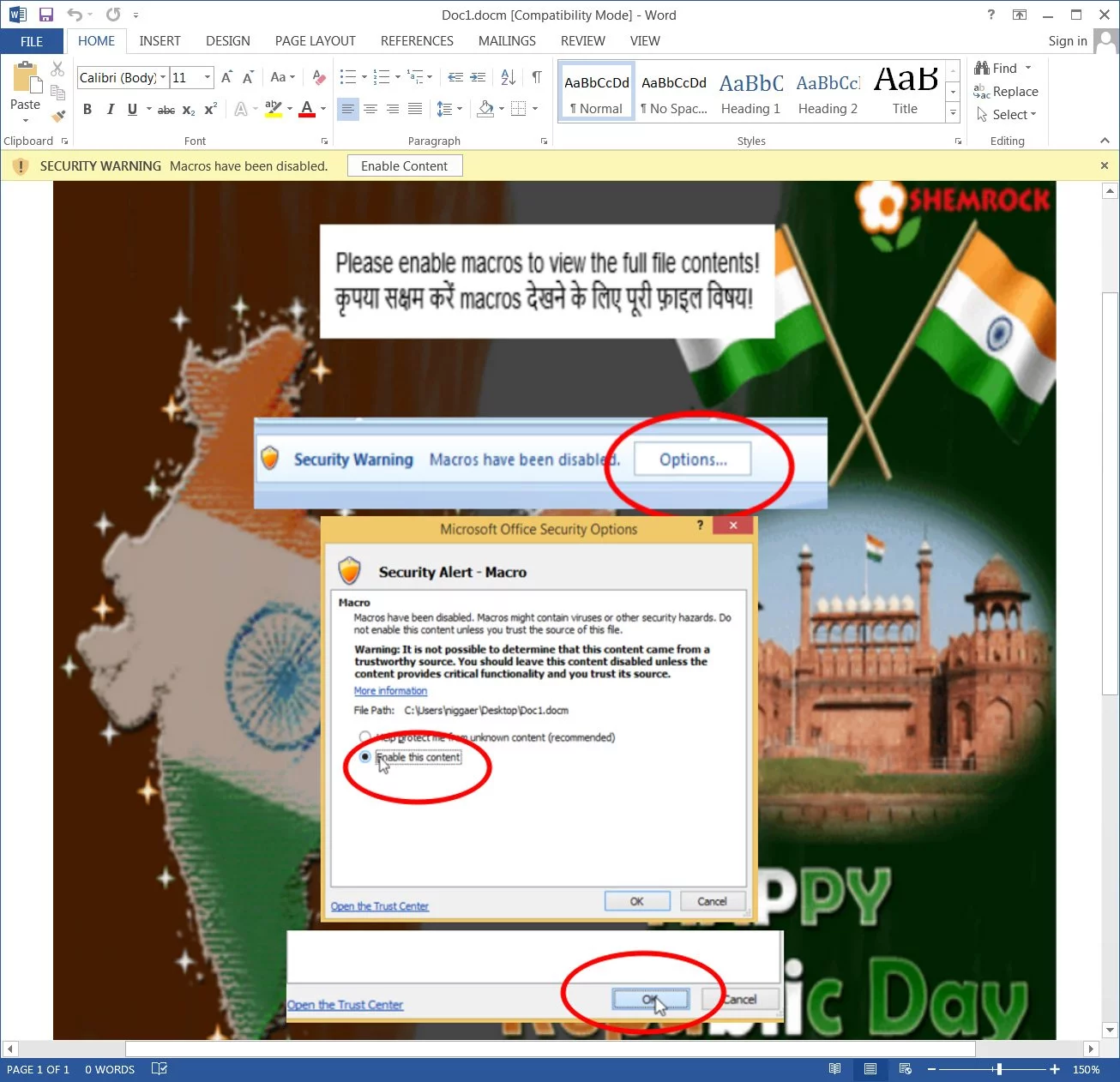
It is unknown whether the malicious Word document is sent via phishing emails or another method, but when opening it, users will be prompted to ‘Enable Content’ to view its content correctly.
Also Read: How a Smart Contract Audit Works and Why it is important
When the button is press, the Word document’s macros will download a file called putty.exe using bitsadmin.exe to the Documents folder and then executed.
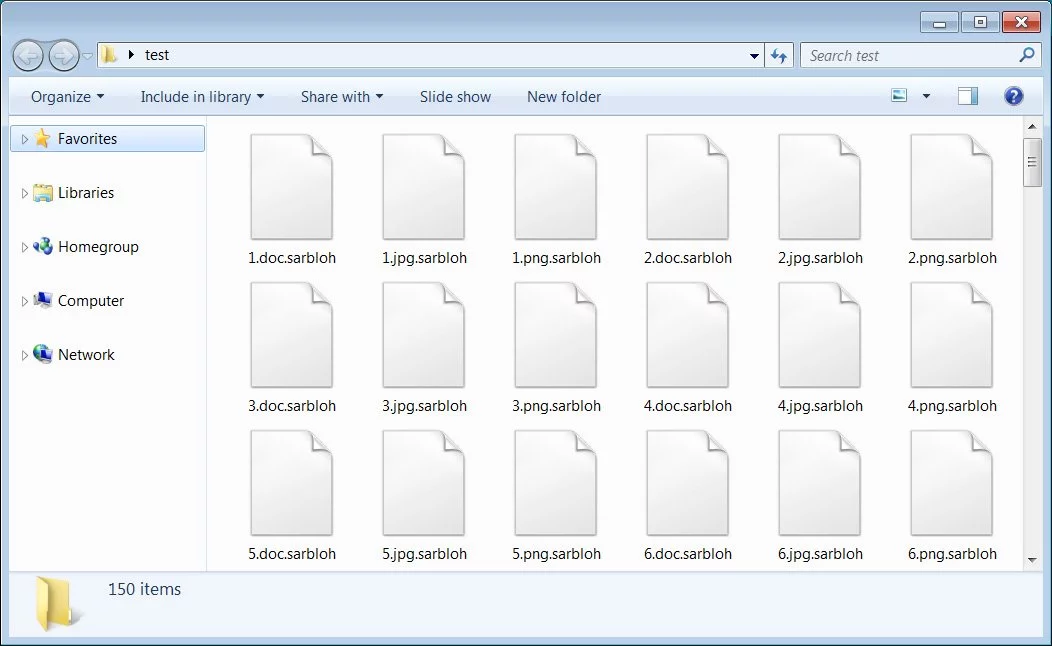
When executed, the ransomware will encrypt files on the computer that match certain file types and append the .sarbloh to the file’s name. For example, the file 1.jpg would be encrypted and renamed to 1.jpg.sarbloh.
After the files on the computer have been encrypted, a ransom note will be created called README_SARBLOH.txt that contains a message supporting the farmers in India.
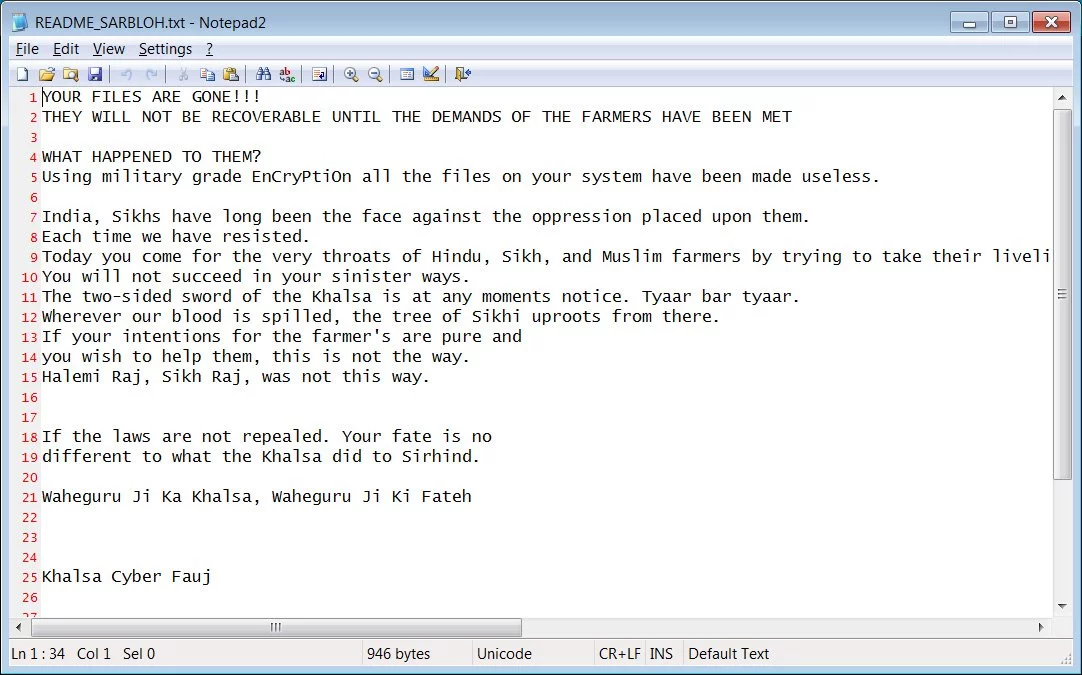
The full text of this ransom note can be read below:
YOUR FILES ARE GONE!!!
THEY WILL NOT BE RECOVERABLE UNTIL THE DEMANDS OF THE FARMERS HAVE BEEN METWHAT HAPPENED TO THEM?
Using military grade EnCryPtiOn all the files on your system have been made useless.India, Sikhs have long been the face against the oppression placed upon them.
Each time we have resisted.
Today you come for the very throats of Hindu, Sikh, and Muslim farmers by trying to take their livelihood.
You will not succeed in your sinister ways.
The two-sided sword of the Khalsa is at any moments notice. Tyaar bar tyaar.
Wherever our blood is spilled, the tree of Sikhi uproots from there.
If your intentions for the farmer’s are pure and
you wish to help them, this is not the way.
Halemi Raj, Sikh Raj, was not this way.
If the laws are not repealed. Your fate is no
different to what the Khalsa did to Sirhind.Waheguru Ji Ka Khalsa, Waheguru Ji Ki Fateh
Khalsa Cyber Fauj
The ransomware appears to be named after the ‘Sarbloh Granth,’ a book of scriptures related to Sikhism.
According to Michael Gillespie, Sarbloh is based on open-source ransomware known as KhalsaCrypt that unfortunately has no known weaknesses.
Also Read: Data Centre Regulations Singapore: Does It Help To Progress?
However, unlike other ransomware, Sarbloh does not remove shadow volume copies, so it may be possible to recover files through shadow volumes.