KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A new botnet is hunting down and transforming infected routers, DVRs, and UPnP network devices into honeypots that help it find other targets to infect.
The malware, dubbed ZHtrap by the 360 Netlab security researchers who spotted it, is loosely based on Mirai’s source code, and it comes with support for x86, ARM, MIPS, and other CPU architectures.
Once it takes over a device, it prevents other malware from re-infecting its bots with the help of a whitelist that only allows already running system processes, blocking all attempts to run new commands.
ZHtrap bots use a Tor command-and-control (C2) server to communicate with other botnet nodes and a Tor proxy to conceal malicious traffic.
The botnet’s main capabilities include DDoS attacks and scanning for more vulnerable devices to infect. However, it also comes with backdoor functionality allowing the operators to download and execute additional malicious payloads.
To propagate, ZHtrap uses exploits targeting four N-day security vulnerabilities in Realtek SDK Miniigd UPnP SOAP endpoints, MVPower DVR, Netgear DGN1000, and a long list of CCTV-DVR devices.
It also scans for devices with weak Telnet passwords from a list of randomly generated IP addresses and collected with the help of the honeypot it deploys on devices already ensnared in the botnet.
Also Read: The Difference Between GDPR and PDPA Under 10 Key Issues
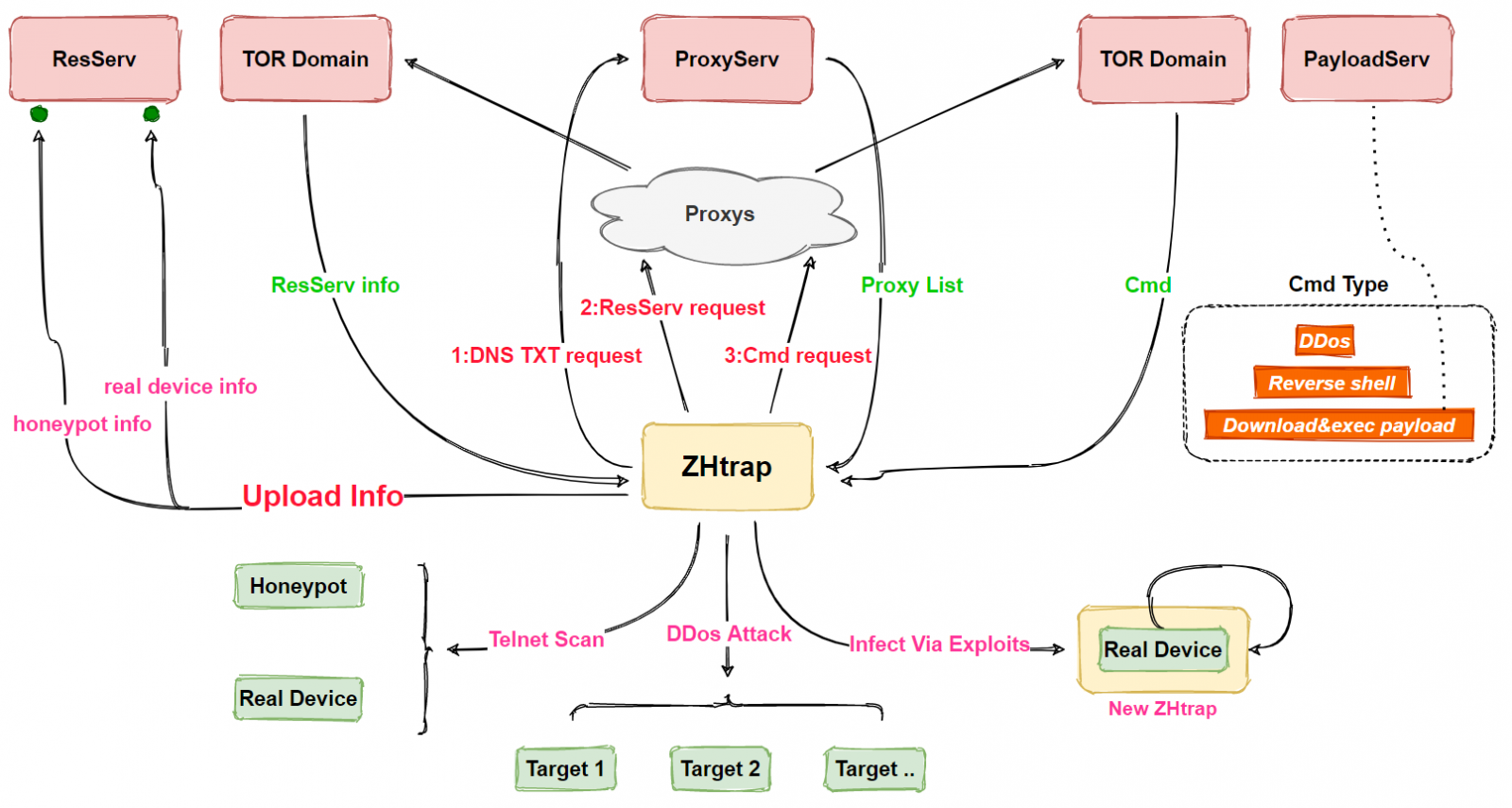
ZHtrap’s most interesting feature is how it turns infected devices into honeypots to collect IP addresses of more targets likely vulnerable to its propagation methods or already infected by other malware.
Once deployed, ZHtrap’s honeypot starts listening to a list of 23 ports, and it sends all IPs connecting to them to its scanning module as potential targets in its attacks.
“Compared to other botnets we have analyzed before, the most interesting part of ZHtrap is its ability to turn infected devices into honeypot,” 360 Netlab said.
“Honeypots are usually used by security researchers as a tool to capture attacks, such as collecting scans, exploits, and samples.
“But this time around, we found that ZHtrap uses a similar technique by integrating a scanning IP collection module, and the collected IPs are used as targets in its own scanning module.”
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
360 Netlab researchers have also recently spotted an upgraded version of the z0Miner cryptomining botnet, which now attempts to infect vulnerable Jenkins and ElasticSearch servers to mine for Monero (XMR) cryptocurrency.