KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






A joint advisory from the U.S. National Security Agency (NSA), the Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI) warn that the Russian Foreign Intelligence Service (SVR) is exploiting five vulnerabilities in attacks against U.S. organizations and interests.
In an advisory issued today, the NSA said that it is aware of the Russian SVR using these vulnerabilities against public-facing services to obtain authentication credentials to further compromise the networks of US corporate and government networks.
The NSA is advising all organizations to immediately patch vulnerable devices to protect against cyberattacks that lead to data theft, banking fraud, and ransomware attacks.
“The vulnerabilities in today’s release are part of the SVR’s toolkit to target networks across the government and private sectors,” Rob Joyce, NSA Director of Cybersecurity, said in a statement to BleepingComputer. “We need to make SVR’s job harder by taking them away.”
The U.S. government strongly advises that all admins “urgently implement associated mitigations” for these vulnerabilities to prevent further attacks by the Russian SVR and other threat actors.
“Mitigation against these vulnerabilities is critically important as U.S. and allied networks are constantly scanned, targeted, and exploited by Russian state-sponsored cyber actors.”
“In addition to compromising the SolarWinds Orion software supply chain, recent SVR activities include targeting COVID-19 research facilities via WellMess malware and targeting networks through the VMware vulnerability disclosed by NSA,” warns the joint advisory.
Also Read: How To Comply With PDPA: A Checklist For Businesses
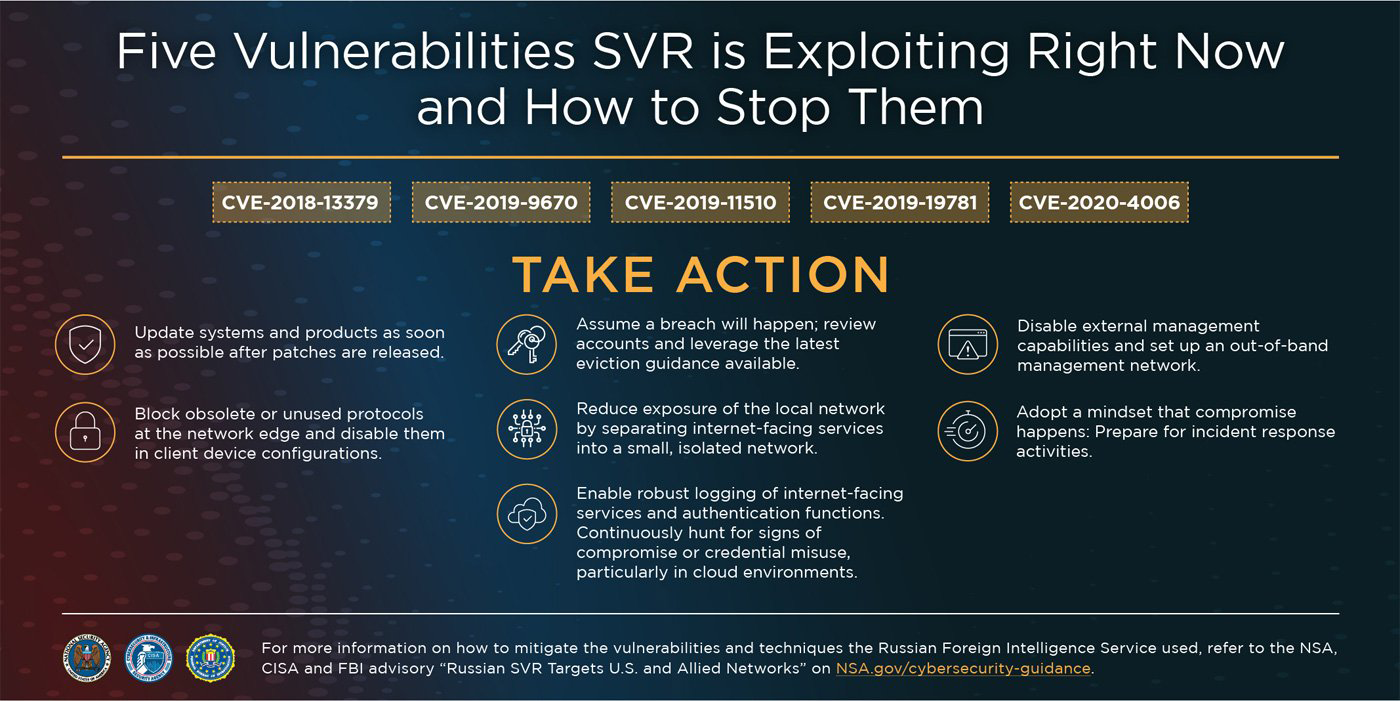
Below are the top five vulnerabilities the NSA, CISA, and the FBI have seen targeted by the Russian SVR.
CVE-2018-13379 targets Fortinet FortiOS 6.0.0 to 6.0.4, 5.6.3 to 5.6.7 and 5.4.6 to 5.4.12:
In Fortinet Secure Sockets Layer (SSL) Virtual Private Network (VPN) web portals, an Improper Limitation of a Pathname to a Restricted Directory (“Path Traversal”) allows an unauthenticated attacker to download system files via special crafted HTTP resource requests.
Threat actors have extensively used this vulnerability in the past to target government agencies and corporate networks, including U.S. govt elections support systems, COVID-19 research organizations, and more recently, to deploy the Cring ransomware.In November 2020, a threat actor leaked the credentials for almost 50,000 Fortinet VPN devices on a hacker forum.
Government advisories: APT29 targets COVID-19 vaccine development & Mitigating Recent VPN Vulnerabilities
CVE-2019-9670 targets Synacor Zimbra Collaboration Suite 8.7.x before 8.7.11p10
In Synacor Zimbra Collaboration Suite, the mailboxd component has an XML External Entity injection (XXE) vulnerability.
Government advisories: APT29 targets COVID-19 vaccine development
CVE-2019-11510 targets Pulse Connect Secure (PCS) 8.2 before 8.2R12.1, 8.3 before 8.3R7.1, and 9.0 before 9.0R3.4
In Pulse Secure VPNs, an unauthenticated remote attacker can send a specially crafted Uniform Resource Identifier (URI) to perform an arbitrary file read.
Pulse Secure VPNs have been a favorite for threat actors for some time, being used to gain access to US government networks, attack hospitals, and deploy ransomware on networks.
Government advisories: Mitigating Recent VPN Vulnerabilities and APT29 targets COVID-19 vaccine development
CVE-2019-19781 targets Citrix ADC and Gateway versions before 13.0.47.24, 12.1.55.18, 12.0.63.13, 11.1.63.15 and 10.5.70.12 and SD-WAN WANOP 4000-WO, 4100-WO, 5000-WO, and 5100-WO versions before 10.2.6b and 11.0.3b.
Citrix Application Delivery Controller (ADC) and Gateway allow directory traversal.
The CVE-2019-19781 vulnerability is known to be used by threat actors, including ransomware gangs, to gain access to corporate networks and deploy malware.
Government advisories: Mitigate CVE-2019-19781, APT29 targets COVID-19 vaccine development, and Detect and Prevent Web Shell Malware.
CVE-2020-4006 targets VMware One Access 20.01 and 20.10 on Linux, VMware Identity Manager 3.3.1 – 3.3.3 on Linux, VMware Identity Manager Connector 3.3.1 – 3.3.3 and 19.03, VMware Cloud Foundation 4.0 – 4.1, and VMware Vrealize Suite Lifecycle Manager 8.x.
VMware Workspace One Access, Access Connector, Identity Manager, and Identity Manager Connector have a command injection vulnerability.
In December 2020, the US government warned that Russian state-sponsored threat actors were exploiting this vulnerability to deploy web shells on vulnerable servers and exfiltrate data.
Government advisories: Russian State-Sponsored Actors Exploiting Vulnerability and Performing Out-of-Band Network Management.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
As the Russian SVR has been utilizing a combination of these vulnerabilities in their attacks, it is strongly advised that all administrators install the associated security updates immediately.
The NSA warned last year that two of these vulnerabilities, CVE-2019-11510 and CVE-2019-19781, are also in the top 25 vulnerabilities utilized by China state-sponsored hackers.