KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







South Korean conglomerate and retail giant E-Land has suffered a ransomware attack causing 23 of its retail stores to suspend operations while they deal with the attack.
E-Land owns sixty retail brands, primarily focusing on apparel, sold through 5,000 franchise retail stores. In addition, E-Land owns and operates hotels and restaurants in South Korea.
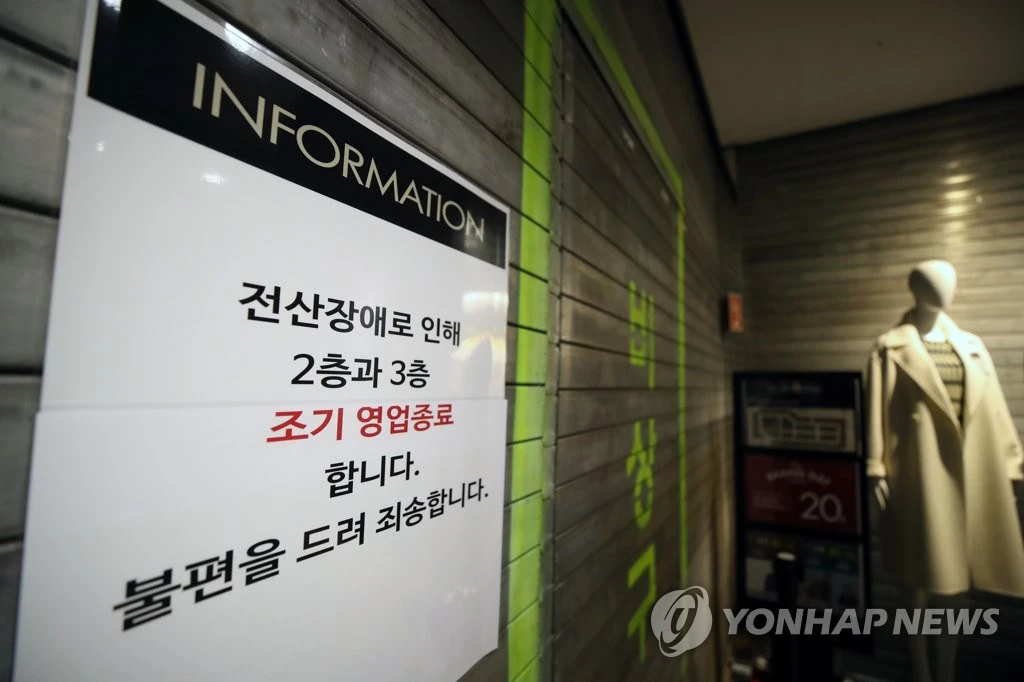
According to South Korean media Yonhap News Agency, E-Land suffered a ransomware attack over the weekend, causing the temporary shut down of 23 out of 50 NC Department Store and NewCore Outlet retail stores.
Today, Chang-Hyun Seok, CEO of E-Land Retail, confirmed the cyberattack and stated that ransomware was deployed at the E-Land headquarters on the morning of November 22nd.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
To prevent the spread of the ransomware attack, E-Land shut down a portion of their IT system, which has impacted their retail outlets’ operation.
“In this regard, intensive measures were taken to shut down the server to prevent further damage. As a result , there was a disruption in the business of some stores, We sincerely apologize to our customers,” Seok apologized in a statement.
Seok says that customer and other sensitive data is encrypted on separate servers and is safe.
Depending on the ransomware operation that conducted the attack, it is possible that unencrypted files and data were stolen.
Since November 2019, most ransomware operations have increasingly been stealing unencrypted files and threatening to release them if not paid. This double-extortion tactic is meant to apply pressure on a victim due to the risks of government fines, data breach notifications, potential lawsuits, and the tarnishing of their reputation.
Unfortunately, unless a company transparently discloses that data was stolen, employees and customers may never know if a ransom is paid. If the ransom is not paid, stolen data will typically be published on ransomware data leak sites designed to shame victims.
Also Read: 15 Best Tools For Your Windows 10 Privacy Settings Setup
At this time, no ransomware operation has claimed responsibility for the attack on E-Land.