KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Mozilla has released Firefox 85.0.1 and includes a fix that prevents a Windows 10 NTFS corruption bug from being triggered from the browser.
Last month, BleepingComputer reported that a bug in Windows 10 and Windows XP allows non-privileged users to mark an NTFS volume as dirty.
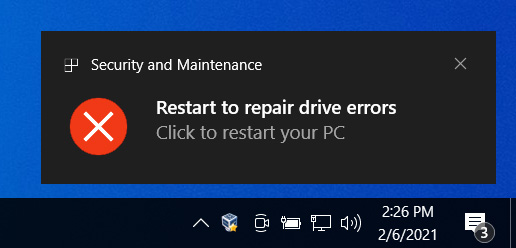
Once the volume was marked dirty, Windows 10 would display an error dialog that states the drive was corrupted and prompt the user to reboot to fix the problem.
For most of the people who tested the bug, rebooting and performing chkdsk would resolve the issue. However, a test by BleepingComputer on a virtual machine caused problems that were not fixed by Chkdsk or Windows 10 startup repair.
Also Read: 15 Best Tools For Your Windows 10 Privacy Settings Setup
In Firefox 85 and earlier, the NTFS corruption bug could be triggered simply by trying to access the path in the browser’s address bar.
With the release of Firefox 85.0.1, instead of trying to access the path, Firefox will simply ignore the path and not attempt to access it.
“Prevent access to NTFS special paths that could lead to filesystem corruption,” states that changelog for Firefox 85.0.1.
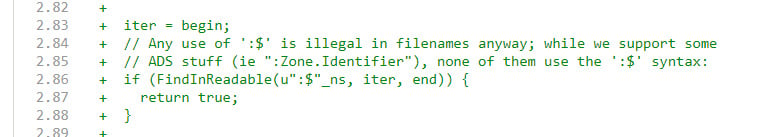
This change can be seen in the Firefox code below that states, “Any use of ‘:$’ is illegal in filenames anyway; while we support some ADS stuff (ie “:Zone.Identifier”), none of them use the ‘:$’ syntax.”
Firefox 85.0.1 also fixes four other bugs and a security vulnerability described in this releases’ changelog.
Existing Firefox users can upgrade to version 85.0.1 by going into the Firefox Menu and selecting Help -> About Firefox. Firefox will then check for a new update, install it, and then prompt you to relaunch Firefox to complete the installation.
Also Read: Going Beyond DPO Meaning: Ever Heard Of Outsourced DPO?
TThis bug can still be abused in Google Chrome and Windows 10 but will hopefully be fixed in next week’s Microsoft Patch Tuesday for February 2021.