KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Telegram has fixed a security issue where self-destructing audio and video files were not being deleted from user’s macOS devices as expected.
Telegram offers a ‘Secret Chat’ mode that offers increased privacy than the standard chats.
When in a Secret Chat, the connections are all end-to-end encrypted, you can’t forward messages to other users, and all messages and media can be configured to automatically self-destruct and be removed from all devices after a certain amount of time.
Yesterday, security researcher Dhiraj Mishra told BleepingComputer that he discovered a vulnerability in the Secret Chat feature on Telegram 7.3 for where self-destructing media is deleted from recipients’ devices.
While performing a Telegram security audit on macOS, Mishra discovered that standard chats would leak the sandbox path where received video and audio files are stored.
Also Read: How to Send Mass Email Without Showing Addresses: 2 Great Workarounds
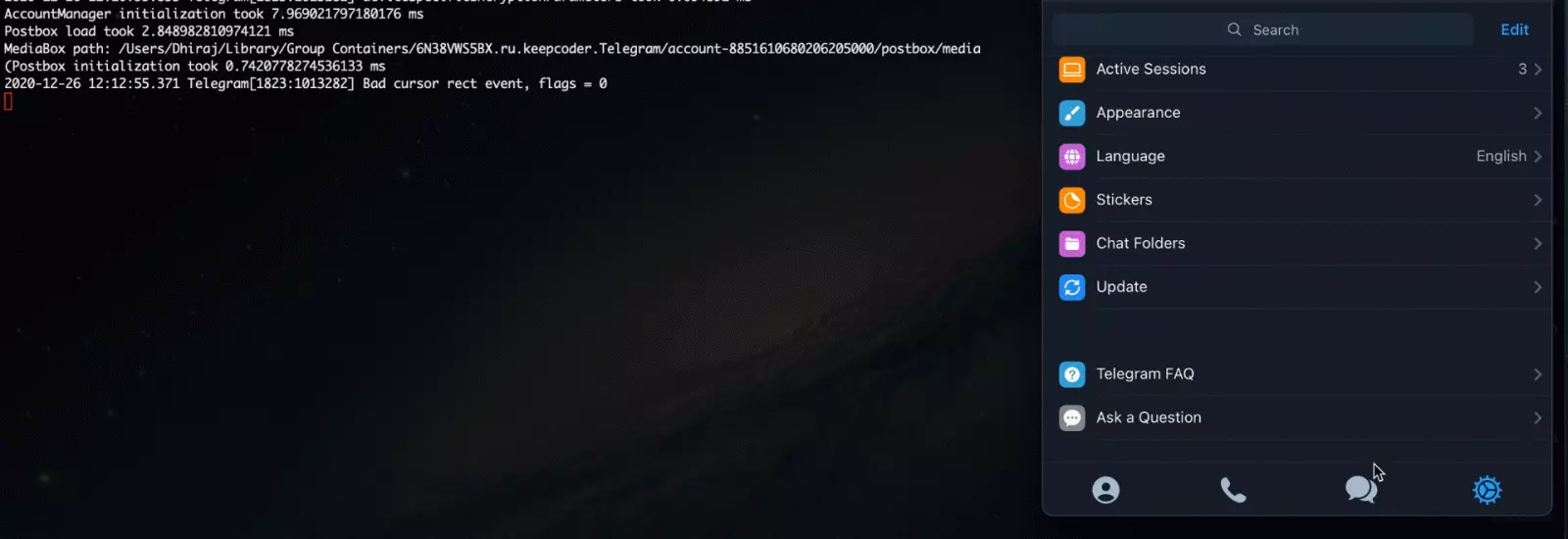
While this path would not be leaked in Secret Chats, received media would still be stored in that same folder.
“In my case the path was (/var/folders/x7/khjtxvbn0lzgjyy9xzc18z100000gn/T/). While performing the same task under secret chat option the MediaResourceData(path://) URI was not leaked but the recorded audio/video message still gets stored on the above path,” Mishra explained in a report on the vulnerability.
Dishra discovered that when the media self-destructed and was removed from the chat, the actual media files were still accessible in the computer’s folder.
“Bob (Attacker using tdesktop macOS) & Alice (Victim) they are communicating under secret chat option and Alice send a recorded audio/video message to Bob with a self-destructed timer of 20 seconds.”
“However the recorded message gets deleted from the chat after 20 seconds but still remains under Bob’s custom path, over here Telegram fails to prevent the privacy for Alice. In general the functionality of self-destructing and leaving no traces failed,” Mishra explains in an attack scenario shared with BleepingComputer.
This bug is particularly concerning for users who may be sending very sensitive video to other Telgrams users under the expectation that the app will automatically remove them after a set time.
To illustrate this security issue, Mishra has provided the following video demonstration.
In addition to the Secret Chat security issue, Mishra discovered that Telegram was storing user’s local passcodes to unlock the app in plain text on the device.
These plaintext passcodes were saved in the Users/[username]/Library/Group Containers/6N38VWS5BX.ru.keepcoder.Telegram/accounts-metadata as a JSON file.
Dishra reported both of these vulnerabilities on December 26th, 2020, and they are now fixed in Telegram 7.4.
Also Read: How a Smart Contract Audit Works and Why it is Important
For reporting both bugs, Mishra received a security bounty of $3,000 from Telegram.