KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







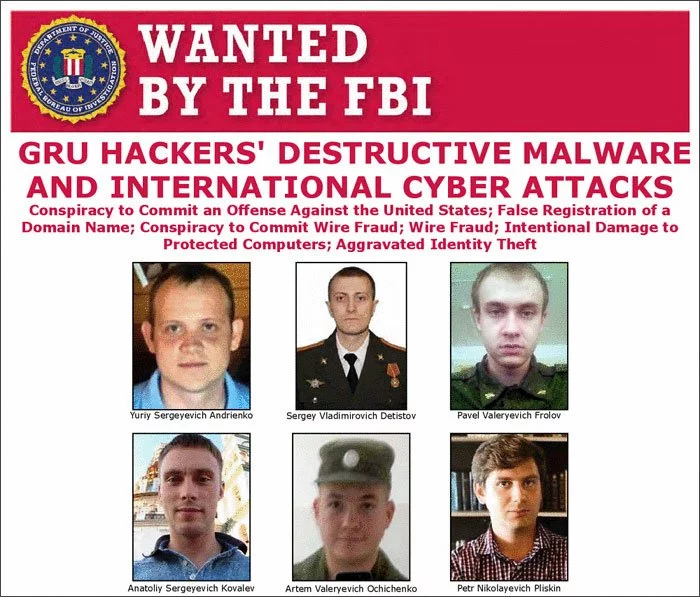
The U.S. Department of Justice has charged six Russian intelligence operatives for hacking operations related to the Pyeongchang Winter Olympics, the 2017 French elections, and the notorious NotPetya ransomware attack.
Believed to be part of the elite Russian hacking group known as “Sandworm”, the indictment states that all six individuals are part of the Russian Main Intelligence Directorate known as GRU.
“No country has weaponized its cyber capabilities as maliciously or irresponsibly as Russia, wantonly causing unprecedented damage to pursue small tactical advantages and to satisfy fits of spite,” said Assistant Attorney General for National Security John C. Demers.
The US indicted Yuriy Sergeyevich Andrienko, 32; Sergey Vladimirovich Detistov, 35; Pavel Valeryevich Frolov, 28; Anatoliy Sergeyevich Kovalev, 29; Artem Valeryevich Ochichenko, 27; and Petr Nikolayevich Pliskin, 32.
Also Read: Deemed Consent PDPA: How Do Businesses Comply?
They are all charged with conspiracy to conduct computer fraud and abuse, conspiracy to commit wire fraud, wire fraud, damaging protected computers, and aggravated identity theft.
The hacking activities they were indicted for include:
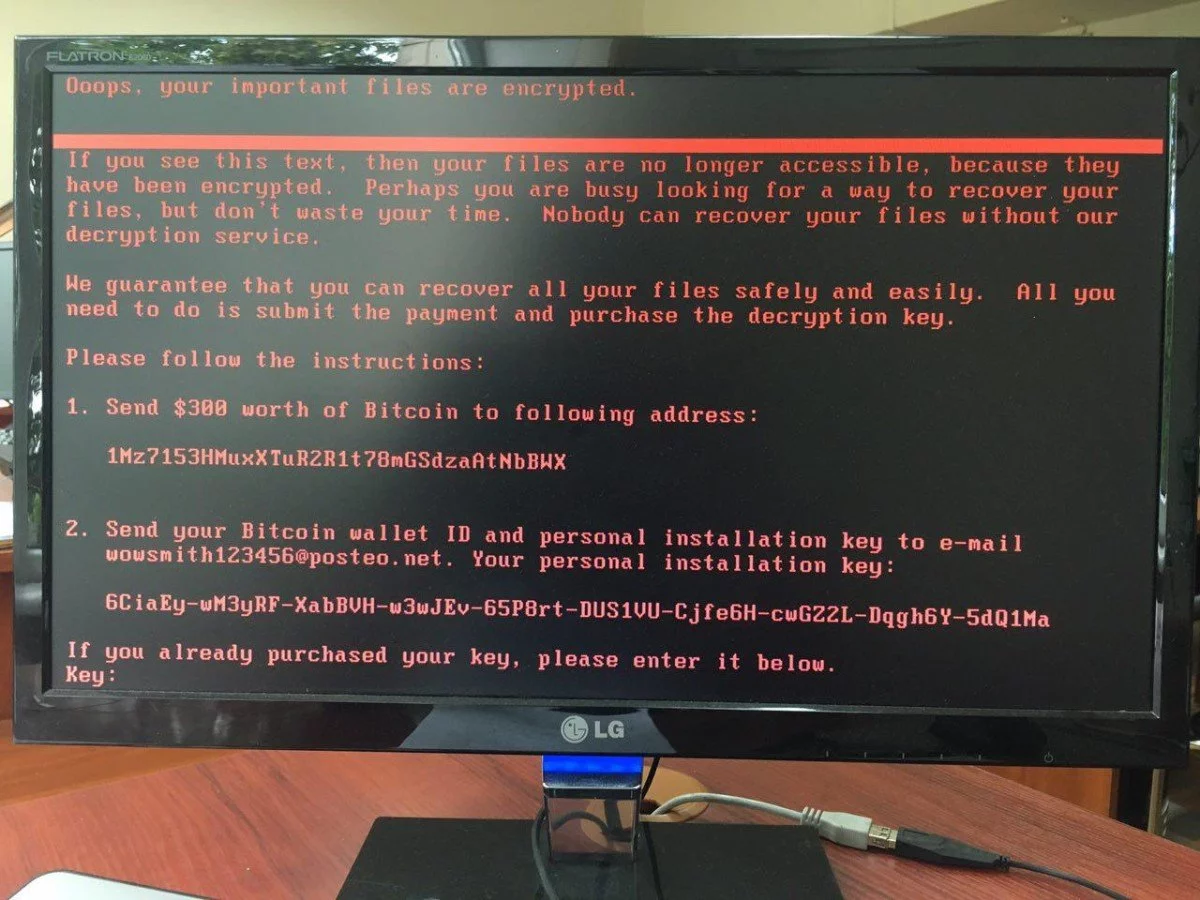 NotPetya attack
NotPetya attack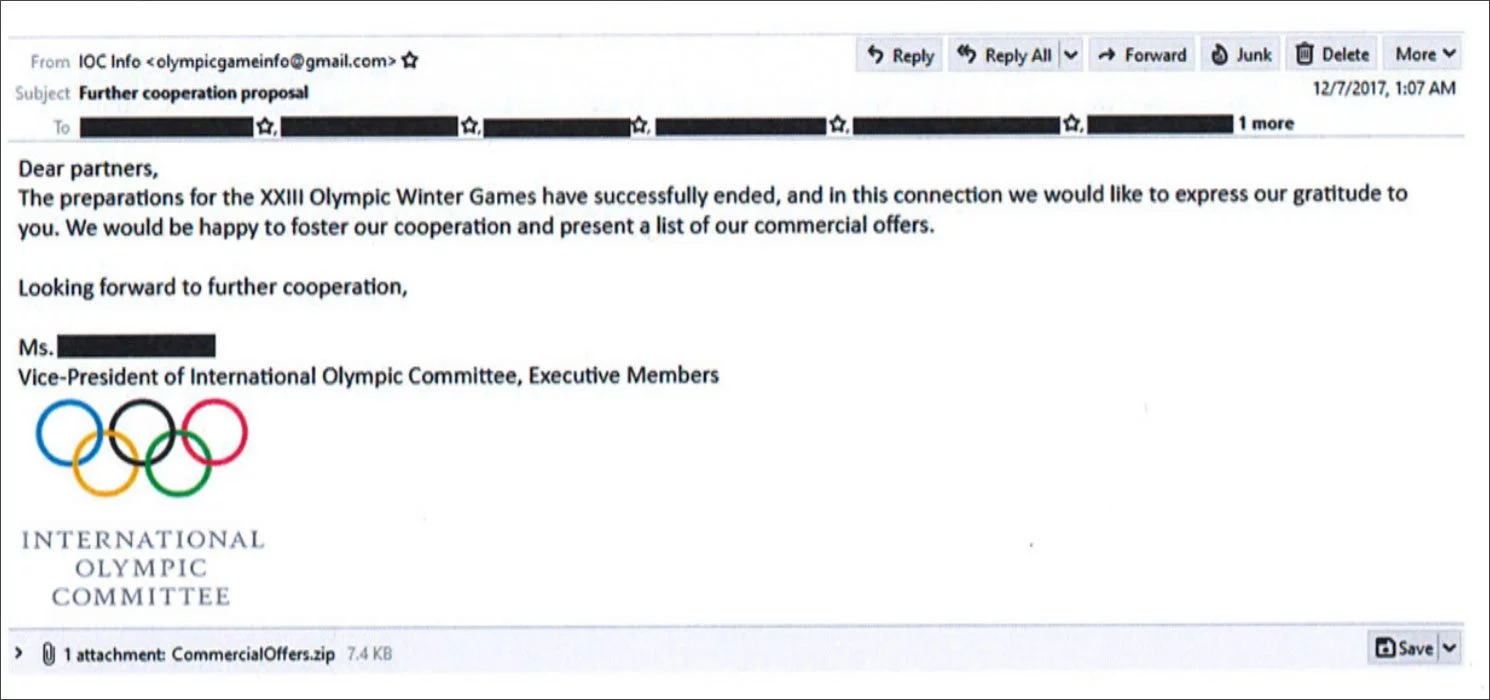 PyeongChang Winter Olympics spearphishing example
PyeongChang Winter Olympics spearphishing exampleIn rare detail, the Department of Justice has detailed each charged person with the specific activity and operations that they were involved in.
| Defendant | Summary of Overt Acts |
| Yuriy Sergeyevich Andrienko | · Developed components of the NotPetya and Olympic Destroyer malware. |
| Sergey Vladimirovich Detistov | · Developed components of the NotPetya malware; and· Prepared spearphishing campaigns targeting the 2018 PyeongChang Winter Olympic Games. |
| Pavel Valeryevich Frolov | · Developed components of the KillDisk and NotPetya malware. |
| Anatoliy Sergeyevich Kovalev | · Developed spearphishing techniques and messages used to target:- En Marche! officials;- employees of the DSTL;- members of the IOC and Olympic athletes; and- employees of a Georgian media entity. |
| Artem Valeryevich Ochichenko | · Participated in spearphishing campaigns targeting 2018 PyeongChang Winter Olympic Games partners; and· Conducted technical reconnaissance of the Parliament of Georgia official domain and attempted to gain unauthorized access to its network. |
| Petr Nikolayevich Pliskin | · Developed components of the NotPetya and Olympic Destroyer malware. |
One of the indicted people, Anatoliy Sergeyevich Kovalev, was previously charged in 2018 for hacking the DNC and running the DCLeaks site.
Also Read: 10 Principles On How To Build A Good Governance Model
NotPetya has previously been attributed to the Sandworm group, also known as BlackEnergy and TeleBots. They were also tied to the KillDisk wiper attacks targeting Ukrainian banks and sea transportation companies.
The cyberattacks targeting the 2017 French election were previously attributed to another state-sponsored Russian hacking group known as Fancy Bear.