KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A vigilante developer turns the tables on software pirates by distributing malware that prevents them from accessing pirated software sites in the future.
Threat actors commonly use pirated software and fake crack sites to distribute malware to unsuspecting users who think they are downloading the latest game or movie.
Malware distributed via these methods is typically information-stealing trojans, ransomware, or cryptominers that can be used to generate value for the threat actor.
In a new report, SophosLabs shares how a vigilante malware is being distributed that prevents pirates from accessing the most popular copyrighted content torrent site, The Pirate Bay.
“In one of the strangest cases I’ve seen in a while, one of my Labs colleagues recently told me about a malware campaign whose primary purpose appears to stray from the more common malware motives.” explains SophosLabs Principal Researcher Andrew Brandt in the new report.
“Instead of seeking to steal passwords or to extort a computer’s owner for ransom, this malware blocks infected users’ computers from being able to visit a large number of websites dedicated to software piracy by modifying the HOSTS file on the infected system.”
Also Read: How to Choose a Penetration Testing Vendor
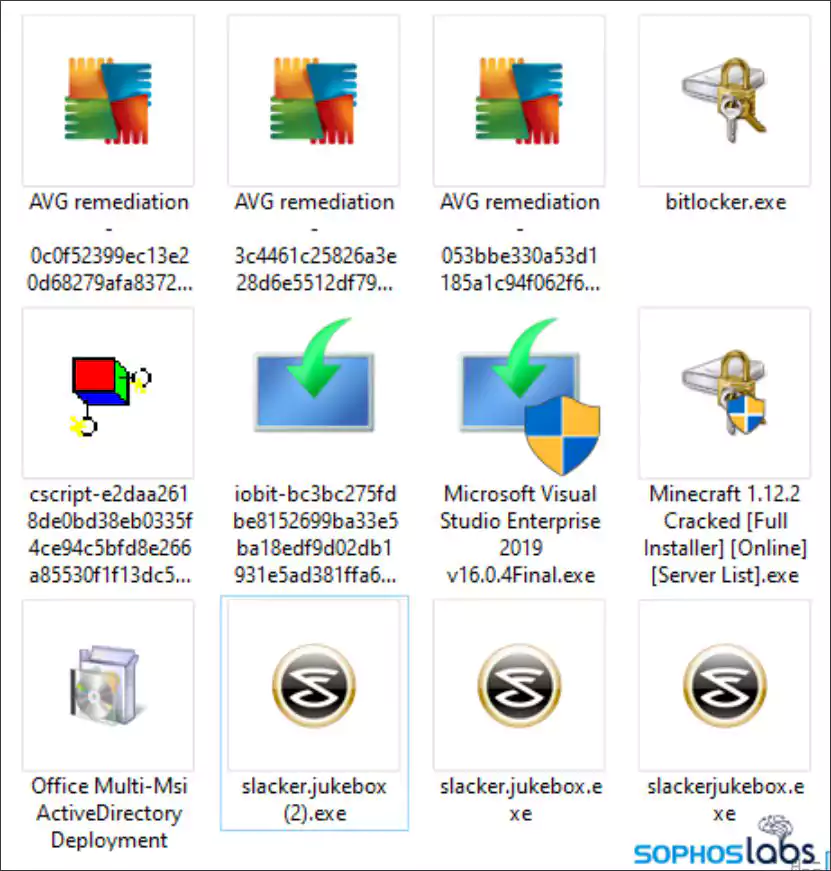
On sites like The Pirate Bay, the malware is being distributed in a similar way to other torrent files in the sense that they contain readme files, NFO files, and shortcut files back to thepiratebay.org.
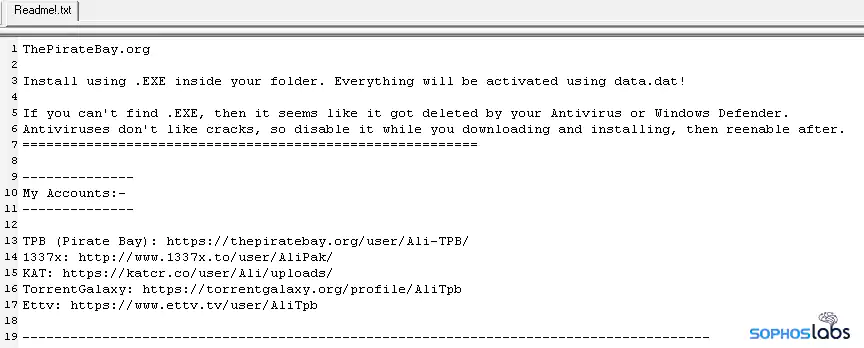
However, many of the files contained in these torrent archives serve no purpose and are only added as filler to impersonate your typical pirated software/movie torrent.
“Looking more closely at these files bundled with the installer, it’s clear that they have no practical benefit other than to give the archive the appearance of files typically shared over Bittorrent, and to modify hash values with the addition of random data,” says Brandt in his report.
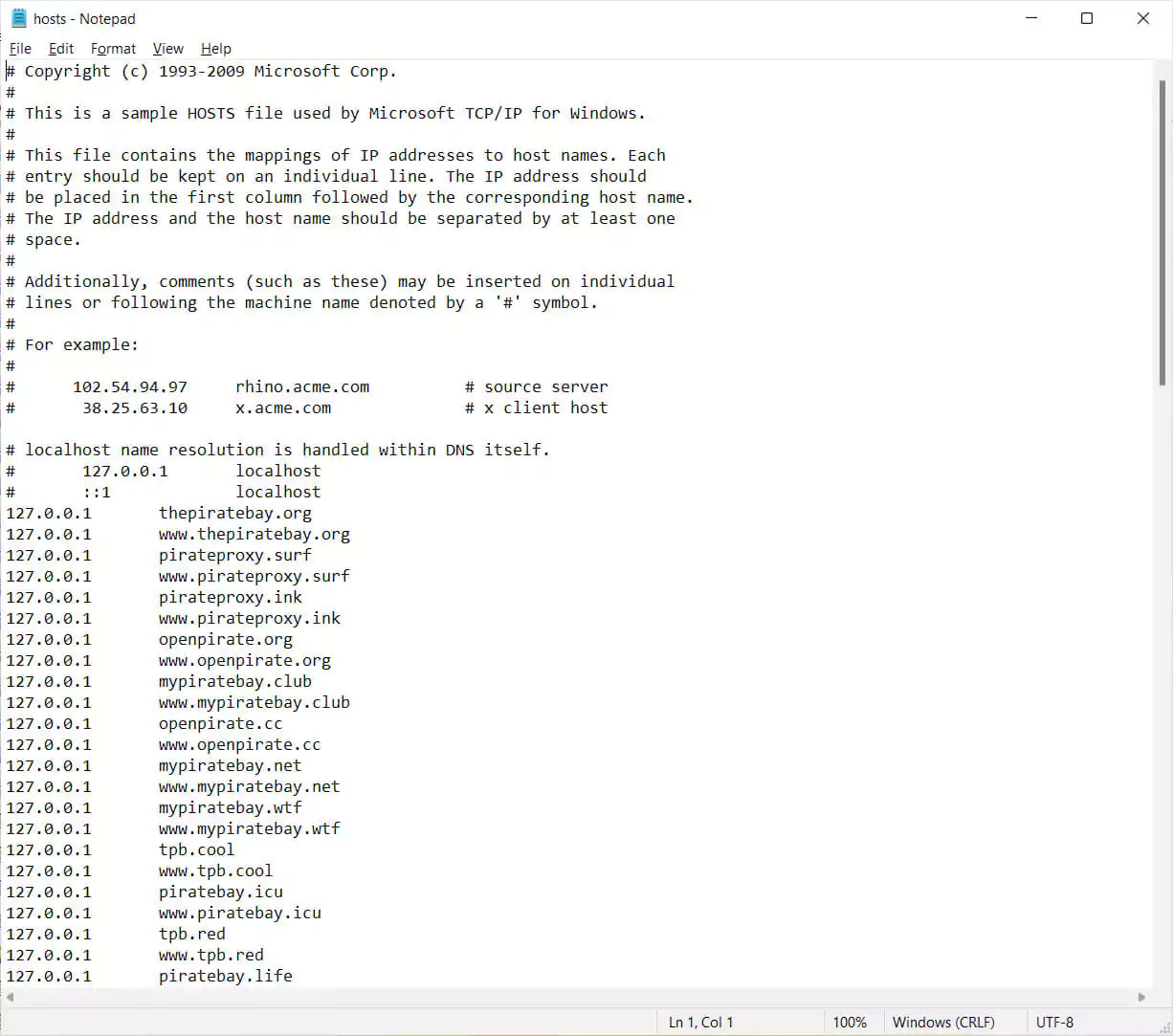
Once a user runs the malware executable, it will modify the Windows HOSTS file to add numerous entries that point to 127.0.0.1 for sites associated with The Pirate Bay.
Also Read: This Educator Aims to Make Good Cyber Hygiene a Household Practice
After adding these HOSTS entries, when a user attempts to access one of the listed sites, they will instead be redirected to their localhost and be unable to connect to the site’s actual IP address. This effectively blocks access to the listed sites that are distributing torrents for copyrighted content.
To make matters worse, when the vigilante malware is executed, it will connect to a remote host under the attacker’s control and send the name of the fake pirated software that has infected the user.
As web servers usually log a visitor’s IP address, the attacker now has both the pirate’s IP address and the name of the software or movie that they attempted to use.
While it is unknown what this information is used for, the threat actors could share it with ISPs, copyright agencies, or even law enforcement.
The attackers could also use this information in further attacks, such as email extortion campaigns where the attacker threatens to reveal the user’s illegal activity if they don’t pay a small extortion demand.
Brandt told BleepingComputer that this malware campaign was live between October 2020 and January 2021, when the attacker’s site went offline.
According to Brandt, the malicious torrents have also stopped being distributed, likely after users stopped seeding them after learning that the files were malicious or fake.
While rare, vigilantes have taken justice in their own hands in the past by hacking into Netgear to remove malware, distributing malware to secure IoT devices, releasing weaponized version.