KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






A wormable vulnerability in the HTTP Protocol Stack of the Windows IIS server can also be used to attack unpatched Windows 10 and Server systems publicly exposing the WinRM (Windows Remote Management) service.
Microsoft already patched the critical bug tracked as CVE-2021-31166 during the May Patch Tuesday.
Luckily, although it can be abused by threat in remote code execution (RCE) attacks, the vulnerability ONLY impacts versions 2004 and 20H2 of Windows 10 and Windows Server.
Microsoft recommended prioritizing patching all affected servers because the vulnerability could allow unauthenticated attackers to execute arbitrary code remotely “in most situations” on vulnerable computers.
Adding to this, over the weekend, security researcher Axel Souchet has published proof-of-concept exploit code that can be used to crash unpatched systems using maliciously crafted packets by triggering blue screens of death.
The bug was found in the HTTP Protocol Stack (HTTP.sys) used as a protocol listener by the Windows IIS web server for processing HTTP requests.
However, as discovered by security researcher Jim DeVries, it also impacts Windows 10 and Server devices running the WinRM service (short for Windows Remote Management), a component of the Windows Hardware Management feature set which also makes use of the vulnerable HTTP.sys.
Also Read: Got Hacked? Here Are 5 Ways to Handle Data Breaches
While home users have to enable the WinRM service manually on their Windows 10 systems, enterprise Windows Server endpoints have WinRM toggled on by default which makes them vulnerable to attacks if they’re running versions 2004 or 20H2.
“[CVE-2021-31166] is commonly used in corporate environments. It’s enabled by default on servers,” DeVries told BleepingComputer.
“I don’t think this is a big risk for home PCs but, should someone marry this to a worm and ransomware, it could run wild in corporate environments.”
DeVries’ findings have also been confirmed by CERT/CC vulnerability analyst Will Dormann who successfully crashed a Windows system exposing the WinRM service using Souchet’s DoS exploit.
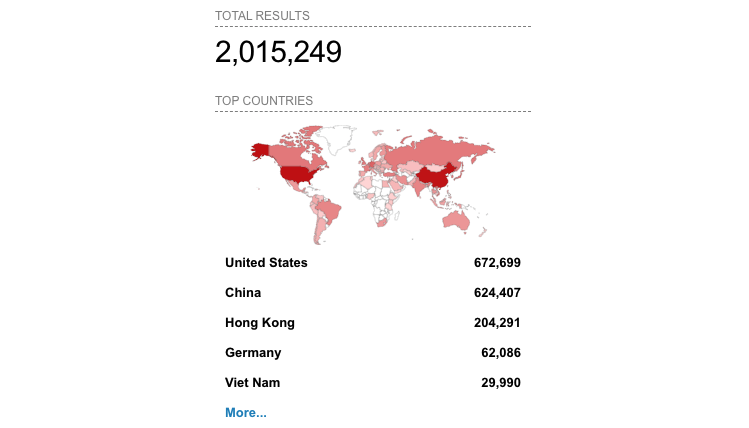
Dormann also discovered that over 2 million Windows systems reachable over the Internet are exposing the vulnerable WinRM service.
Luckily, only a subset of all these Internet-exposed Windows systems is vulnerable seeing that the vulnerability only impacts Windows 10 and Windows Server, versions 2004 and 20H2.
The exploit’s release could likely enable adversaries to create their own exploits faster, potentially also allowing remote code execution.
Also Read: Compliance Course Singapore: Spotlight on the 3 Offerings
However, the impact should also be limited and the patching process quite quick since most home users using affected Windows 10 versions have probably updated their systems last week.
Similarly, many companies should likely be safe from attacks targeting the bug since they don’t usually deploy the latest Windows Server versions as soon as they are released.